## BYOS: Bring your own stager 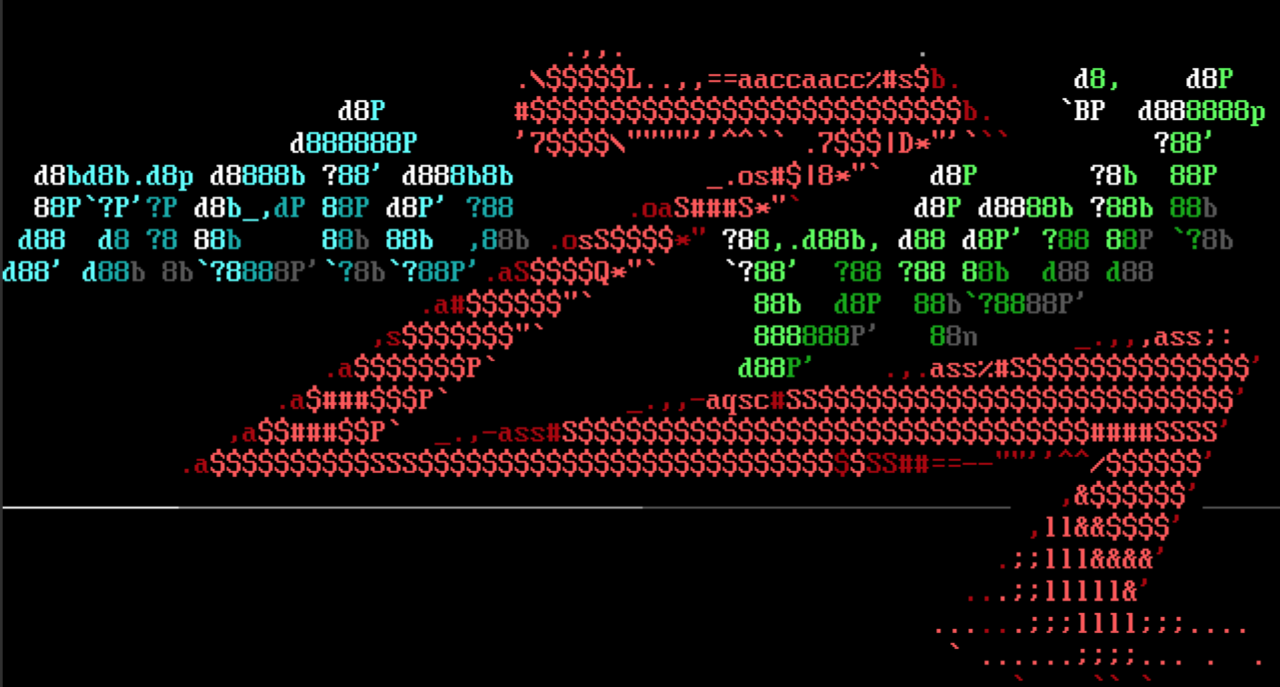 We try hard to make sure we have a great choice of fully-functional ...
Continue Reading
September 16, 2022
### Impact Harbor fails to validate the user permissions when updating a robot account that belongs to a project that the authenticated user doesnt have access to. API call: PUT /robots/{robot_id} B ...
Continue Reading
September 16, 2022
### Impact It's possible to store JavaScript in an attachment name, which will be executed by anyone trying to move the corresponding attachment. For example, an attachment with name `>.jpg` will e ...
Continue Reading
September 16, 2022
### Impact The Rego compiler provides a (deprecated) `WithUnsafeBuiltins` function, which allows users to provide a set of built-in functions that should be deemed unsafe and as such rejected by ...
Continue Reading
September 16, 2022
The PBKDF2-based JWE key management algorithms expect a JOSE Header Parameter named `p2c` ([PBES2 Count](https://www.rfc-editor.org/rfc/rfc7518.html#section-4.8.1.2)), which determines how many PBKDF2 ...
Continue Reading
September 16, 2022
### Impact Harbor fails to validate the user permissions when updating tag retention policies. API call: PUT /retentions/{id} By sending a request to update a tag retention policy with an id that b ...
Continue Reading
September 16, 2022
### Impact Harbor fails to validate the user permissions when updating tag retention policies. API call: PUT /retentions/{id} By sending a request to update a tag retention policy with an id that b ...
Continue Reading
September 16, 2022
### Impact Harbor fails to validate the user permissions to view Webhook policies including relevant credentials configured in different projects the user doesnt have access to, resulting in malicio ...
Continue Reading
September 16, 2022

Back to Main


