
Today, Talos is publishing a glimpse into the most prevalent threats we’ve observed between June 30 and July 7. As with previous roundups, this post isn’t meant to be an in-depth analysis. Instead, this post will summarize the threats we’ve observed by highlighting key behavioral characteristics, indicators of compromise, and discussing how our customers are automatically protected from these threats.
As a reminder, the information provided for the following threats in this post is non-exhaustive and current as of the date of publication. Additionally, please keep in mind that IOC searching is only one part of threat hunting. Spotting a single IOC does not necessarily indicate maliciousness. Detection and coverage for the following threats is subject to updates, pending additional threat or vulnerability analysis. For the most current information, please refer to your Firepower Management Center, [Snort.org](), or [ClamAV.net]().
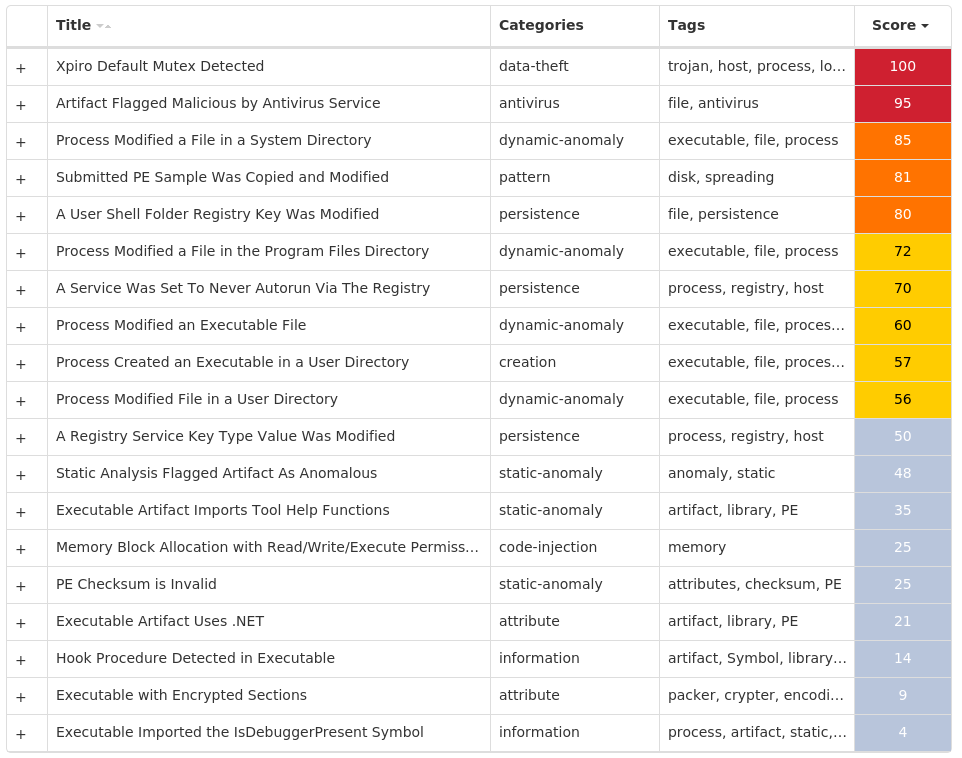
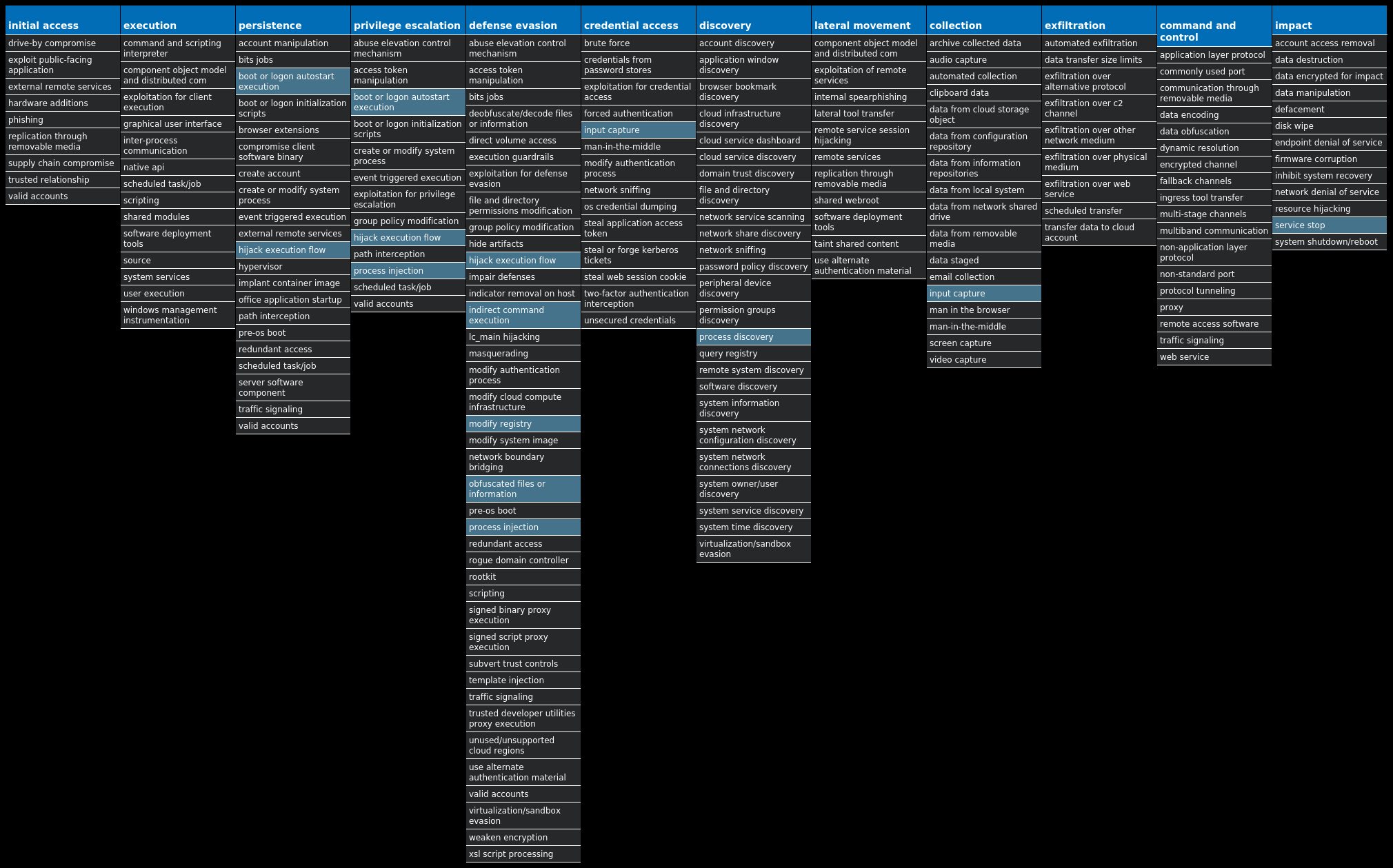
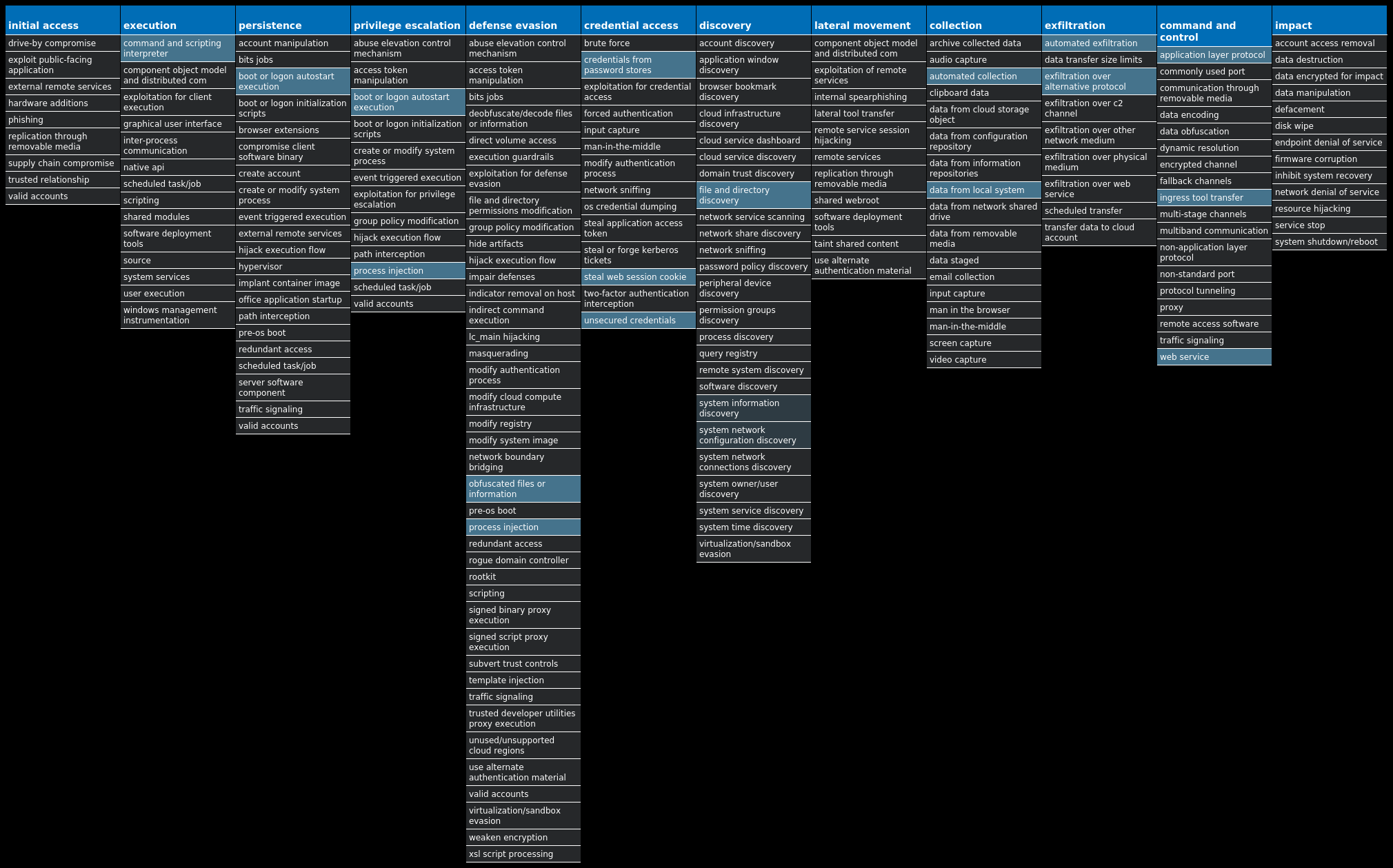
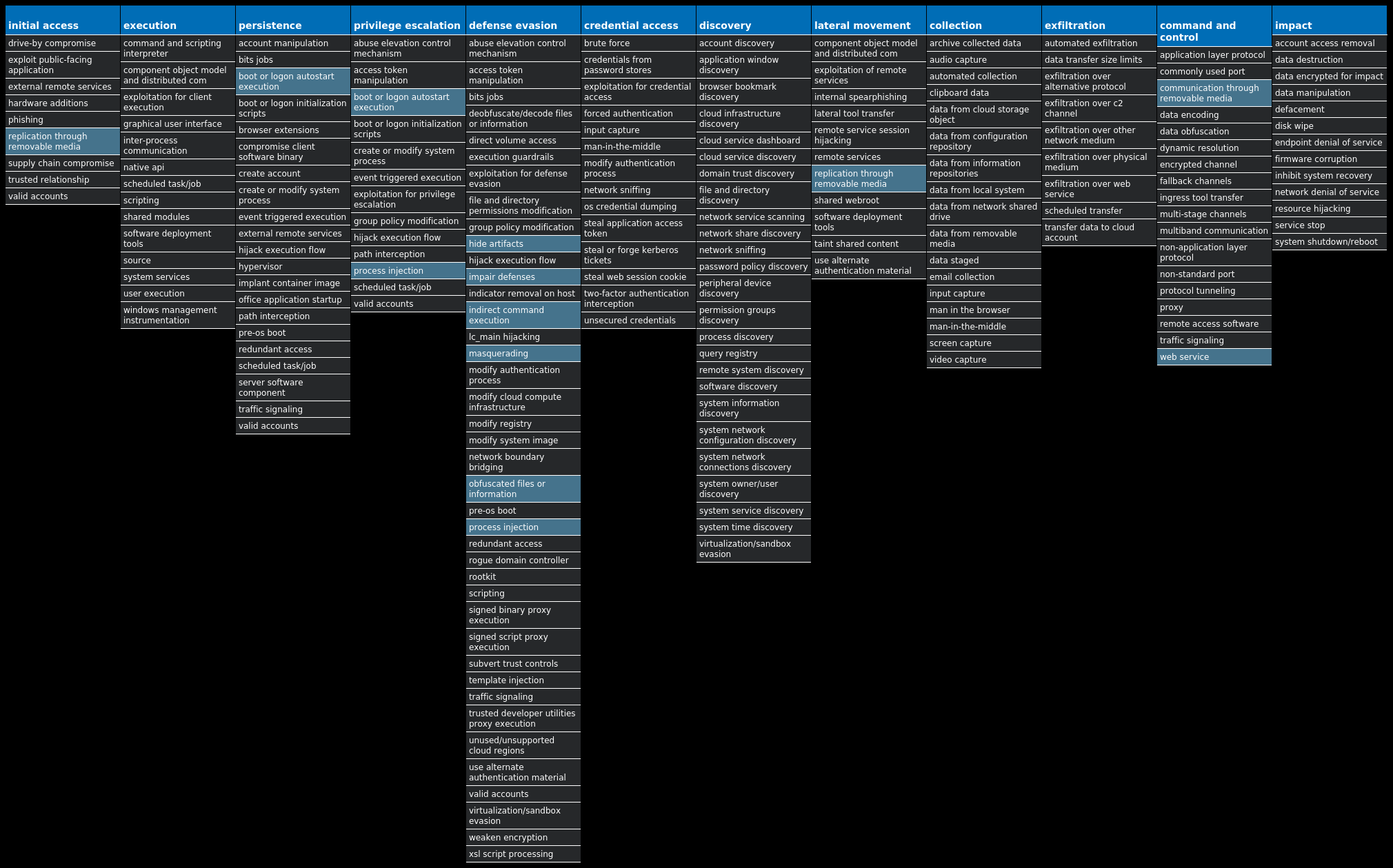
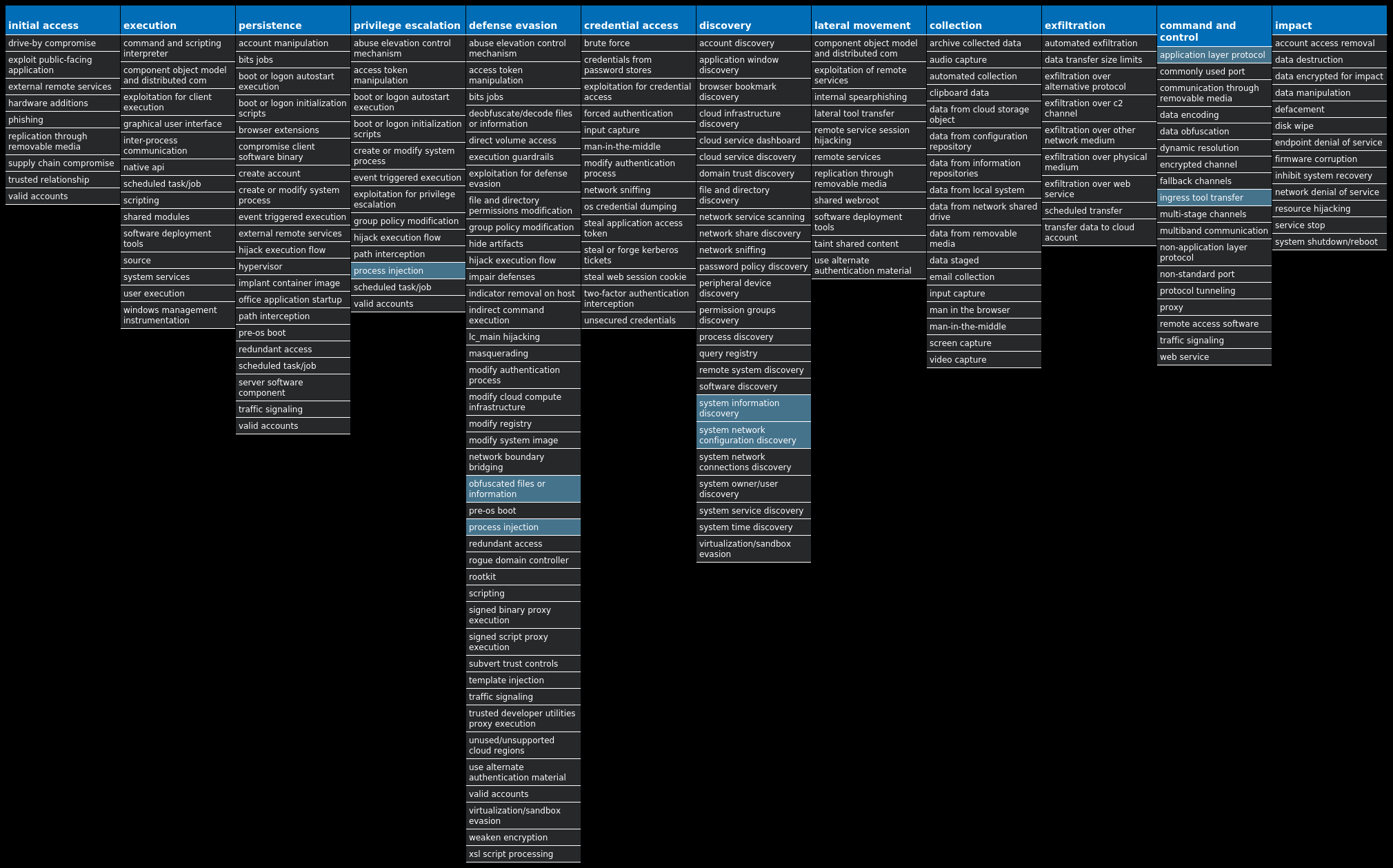
For each threat described below, this blog post only lists 25 of the associated file hashes and up to 25 IOCs for each category. An accompanying JSON file can be found [here]() that includes the complete list of file hashes, as well as all other IOCs from this post. A visual depiction of the MITRE ATT&CK techniques associated with each threat is also shown. In these images, the brightness of the technique indicates how prevalent it is across all threat files where dynamic analysis was conducted. There are five distinct shades that are used, with the darkest indicating that no files exhibited technique behavior and the brightest indicating that technique behavior was observed from 75 percent or more of the files.
The most prevalent threats highlighted in this roundup are:
Threat Name| Type| Description
—|—|—
Win.Virus.Xpiro-10005555-1| Virus| Expiro is a known file infector and information-stealer that hinders analysis with anti-debugging and anti-analysis tricks.
Win.Packed.Dridex-10005543-1| Packed| Dridex is a well-known banking trojan that aims to steal credentials and other sensitive information from an infected machine.
Win.Packed.njRAT-10005525-1| Packed| njRAT, also known as Bladabindi, is a remote access trojan (RAT) that allows attackers to execute commands on the infected host, log keystrokes and remotely turn on the victim’s webcam and microphone. njRAT was developed by the Sparclyheason group. Some of the largest attacks using this malware date back to 2014.
Win.Packed.Azorult-10005443-0| Packed| Azorult is a banking trojan that attempts to steal credit card data and other sensitive information to facilitate cybercrime.
Win.Worm.Vobus-10005311-1| Worm| Vobus is a worm that spreads itself through removable drives. Once installed, Vobus will often download and execute additional malware.
Win.Packed.Zusy-10005219-0| Packed| Zusy, also known as TinyBanker or Tinba, is a trojan that uses man-in-the-middle attacks to steal banking information. When executed, it injects itself into legitimate Windows processes such as “explorer.exe” and “winver.exe.” When the user accesses a banking website, it displays a form to trick the user into submitting personal information.
Win.Packed.Upatre-10005147-0| Packed| Upatre is a malicious downloader often used by exploit kits and phishing campaigns. It downloads and executes malicious executables, such as banking malware.
Win.Packed.Redline-10005632-0| Packed| Redline Stealer is an information-stealer written in .NET and sold on hacking forums.
* * *
## Threat Breakdown
### Win.Virus.Xpiro-10005555-1
#### Indicators of Compromise
* IOCs collected from dynamic analysis of 15 samples
Registry Keys| Occurrences
—|—
`SYSTEMCONTROLSET001SERVICESCLR_OPTIMIZATION_V4.0.30319_64
Value Name: Type`| 15
`SYSTEMCONTROLSET001SERVICESCLR_OPTIMIZATION_V4.0.30319_64
Value Name: Start`| 15
`SYSTEMCONTROLSET001SERVICESCOMSYSAPP
Value Name: Type`| 15
`SYSTEMCONTROLSET001SERVICESCOMSYSAPP
Value Name: Start`| 15
`SYSTEMCONTROLSET001SERVICESIDSVC
Value Name: Type`| 15
`SYSTEMCONTROLSET001SERVICESIDSVC
Value Name: Start`| 15
`SYSTEMCONTROLSET001SERVICESIEETWCOLLECTORSERVICE
Value Name: Type`| 15
`SYSTEMCONTROLSET001SERVICESIEETWCOLLECTORSERVICE
Value Name: Start`| 15
`SYSTEMCONTROLSET001SERVICESMOZILLAMAINTENANCE
Value Name: Type`| 15
`SYSTEMCONTROLSET001SERVICESMOZILLAMAINTENANCE
Value Name: Start`| 15
`SYSTEMCONTROLSET001SERVICESMSISERVER
Value Name: Type`| 15
`SYSTEMCONTROLSET001SERVICESMSISERVER
Value Name: Start`| 15
`SYSTEMCONTROLSET001SERVICESOSE
Value Name: Type`| 15
`SYSTEMCONTROLSET001SERVICESOSE
Value Name: Start`| 15
`SYSTEMCONTROLSET001SERVICESUI0DETECT
Value Name: Type`| 15
`SYSTEMCONTROLSET001SERVICESUI0DETECT
Value Name: Start`| 15
`SYSTEMCONTROLSET001SERVICESVDS
Value Name: Type`| 15
`SYSTEMCONTROLSET001SERVICESVDS
Value Name: Start`| 15
`SYSTEMCONTROLSET001SERVICESCLR_OPTIMIZATION_V2.0.50727_32
Value Name: Start`| 15
`SYSTEMCONTROLSET001SERVICESALG
Value Name: Start`| 15
`SYSTEMCONTROLSET001SERVICESEHRECVR
Value Name: Start`| 15
`SYSTEMCONTROLSET001SERVICESEHSCHED
Value Name: Start`| 15
`SYSTEMCONTROLSET001SERVICESFAX
Value Name: Start`| 15
`SYSTEMCONTROLSET001SERVICESMICROSOFT SHAREPOINT WORKSPACE AUDIT SERVICE
Value Name: Start`| 15
`SYSTEMCONTROLSET001SERVICESMSDTC
Value Name: Start`| 15
Mutexes| Occurrences
—|—
`Globalmlbjlegc`| 15
`GlobalMedia Center Tuner Request`| 1
Files and or directories created| Occurrences
—|—
`%CommonProgramFiles(x86)%microsoft sharedSource EngineOSE.EXE`| 15
`%ProgramFiles(x86)%Microsoft OfficeOffice14GROOVE.EXE`| 15
`%ProgramFiles(x86)%Mozilla Maintenance Servicemaintenanceservice.exe`| 15
`%SystemRoot%Microsoft.NETFramework64v2.0.50727mscorsvw.exe`| 15
`%SystemRoot%Microsoft.NETFramework64v3.0Windows Communication Foundationinfocard.exe`| 15
`%SystemRoot%Microsoft.NETFramework64v4.0.30319mscorsvw.exe`| 15
`%SystemRoot%Microsoft.NETFrameworkv2.0.50727mscorsvw.exe`| 15
`%SystemRoot%Microsoft.NETFrameworkv4.0.30319mscorsvw.exe`| 15
`%System32%FXSSVC.exe`| 15
`%System32%UI0Detect.exe`| 15
`%System32%VSSVC.exe`| 15
`%System32%alg.exe`| 15
`%System32%dllhost.exe`| 15
`%System32%ieetwcollector.exe`| 15
`%System32%msdtc.exe`| 15
`%System32%msiexec.exe`| 15
`%System32%snmptrap.exe`| 15
`%System32%vds.exe`| 15
`%SystemRoot%ehomeehrecvr.exe`| 15
`%SystemRoot%ehomeehsched.exe`| 15
`%SystemRoot%Microsoft.NETFrameworkv2.0.50727ngen_service.log`| 15
`%SystemRoot%Microsoft.NETFramework64v2.0.50727ngen_service.log`| 15
`%SystemRoot%SysWOW64dllhost.exe`| 15
`%SystemRoot%SysWOW64msiexec.exe`| 15
`%SystemRoot%SysWOW64svchost.exe`| 15
*See JSON for more IOCs
#### File Hashes
`1c73aef0dcdc4d9a5ecdba97fe58600764bf70698f2893bd24955c94917087e5`
`34d20a508da57e8592ae17817b6f966cc5c3f512e85d42655890c20bc37bc5eb`
`412039c2acef1049a258be2f2915b5c07ce2af0faff727d5e8dc6264e93ba868`
`5c5d9773a002fe318d3ccb93974e1f446991e22871d8e30591e1867c429b2497`
`5cb478d11f449bf98c4e4226f2f1a372aaddfc9e9766817152a07ed0c09fbee6`
`5fa1db30a27b52b990e8b984153599496710d36e49ae2937c26c36d83ee65183`
`6d1c0f751b17a85a1f51f61ef519534cf12188401ba96a68fdd7fd7a163baf05`
`752c6582e31e1b78c7285c4e22ccc0bfb83ffc8cb2da715a2f3dbe1e92d84fcd`
`761ccc8a2cfc286adf98f038c7934d3503647f6572a992f1e1c3db1d4ef25b08`
`9cc86a485a7bd3055a19eccf403df3b5c0ad11730a4a6fd1b5a7a0a3b1671b06`
`b7d7a1660272801230a95d96929f762f60c5283db517fd3424b9dd8c419a9a7f`
`d25a78b131cf423df645ef22b64cc0207462200cb4b79625a0a9d6006ccfe1f6`
`e12f82e10138672ee10051aaec374e1a76614b51be1dc901827f0e0a53f10841`
`f9de73708d356991bbbba348627b8aa27cda1aa0be4f70eb5e777da201d21d3f`
`fe50543951519ea8dddfebd01cf957e494009f03184eef2d664b7c22b6493d10`
#### Coverage
Product| Protection
—|—
Secure Endpoint| 
Cloudlock| N/A
CWS| 
Email Security| 
Network Security| N/A
Stealthwatch| N/A
Stealthwatch Cloud| N/A
Secure Malware Analytics| 
Umbrella| N/A
WSA| N/A
#### Screenshots of Detection
#### Secure Endpoint
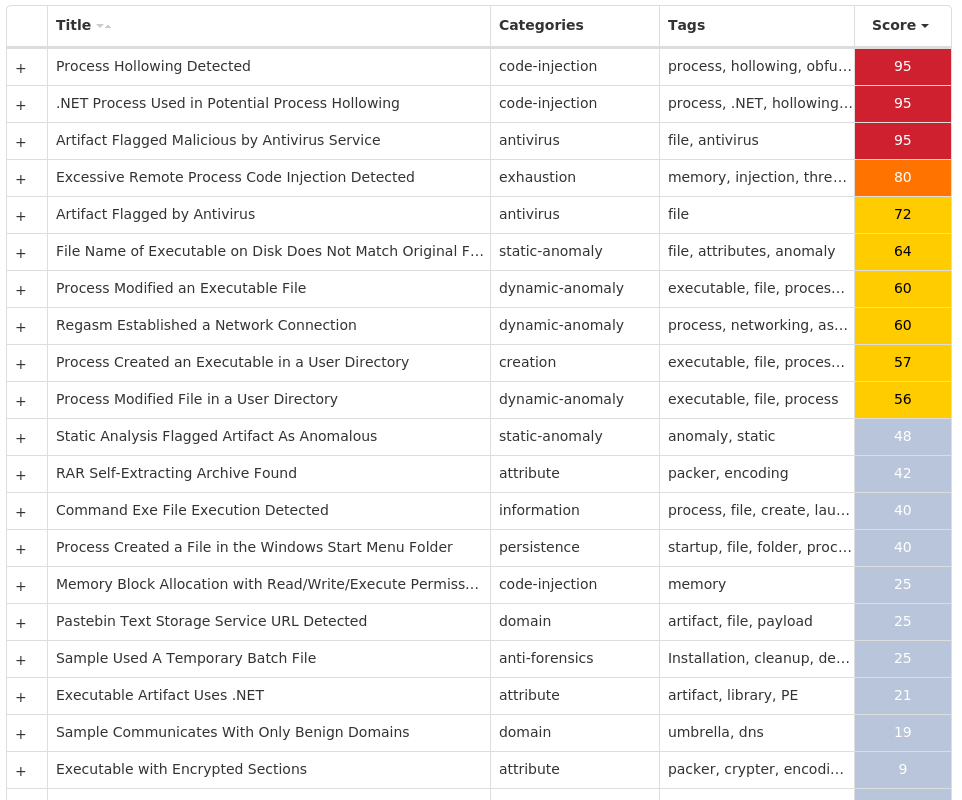
#### Secure Malware Analytics
#### MITRE ATT&CK
* * *
### Win.Packed.Dridex-10005543-1
#### Indicators of Compromise
* IOCs collected from dynamic analysis of 22 samples
Registry Keys| Occurrences
—|—
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUNONCE
Value Name: trkcore`| 22
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONPOLICIESSYSTEM
Value Name: DisableTaskMgr`| 22
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONACTION CENTERCHECKS{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.CHECK.0
Value Name: CheckSetting`| 22
Mutexes| Occurrences
—|—
“| 22
IP Addresses contacted by malware. Does not indicate maliciousness| Occurrences
—|—
`142[.]251[.]40[.]206`| 22
`104[.]20[.]67[.]143`| 9
`104[.]20[.]68[.]143`| 7
`172[.]67[.]34[.]170`| 6
Domain Names contacted by malware. Does not indicate maliciousness| Occurrences
—|—
`pastebin[.]com`| 22
`w[.]google[.]com`| 22
`www[.]4rak7wdwbb[.]com`| 2
`www[.]y8206x7iky[.]com`| 2
`www[.]b80gtnqzu9[.]com`| 2
`www[.]zlkmezpnrd[.]com`| 2
`www[.]sx1zwrixed[.]com`| 2
`www[.]whi33nj4zg[.]com`| 2
`www[.]buytdummiu[.]com`| 2
`www[.]kta6uvcf0u[.]com`| 2
`www[.]3wiqpi0pah[.]com`| 2
`www[.]yygtvkvcgt[.]com`| 2
`www[.]s4j08bdcq7[.]com`| 2
`www[.]ngjtj9t0t2[.]com`| 2
`www[.]5l4uaqwuiw[.]com`| 2
`www[.]edstvaaqay[.]com`| 2
`www[.]hojchurgkj[.]com`| 2
`www[.]kkhqgrgpxj[.]com`| 2
`www[.]tfakt9f97x[.]com`| 1
`www[.]7zgalqlihh[.]com`| 1
`www[.]6rgxtzw8t9[.]com`| 1
`www[.]oekvom89dv[.]com`| 1
`www[.]dwdvdo3uwb[.]com`| 1
`www[.]ci7zigeyi9[.]com`| 1
`www[.]p2fyffcb2d[.]com`| 1
*See JSON for more IOCs
#### File Hashes
`091ddfa7b114578be6349cf89f90db154beae89659343baa0614c737eefa2eda`
`11364341fa9927e9a57ed6613053d7f7fa4f3ee96aefe74e5220bbf2d9e8b188`
`1855173ba31bd5abf20506cd0246f96b8236d148d15d49cf7febdbdebfceda7c`
`247dd8308dcde95d012a2d9e2d0a02e5bde8190447ac34f6db70527270c2e510`
`2a72bba3d05ab4f34aed231ae08e618f89189a1977b1dcf3e7202dd67ffd3c79`
`59d3cc03e038819bd8e0df14ce0e6a1aa56dd7f90376de5bd3b55be4bcce815d`
`6e251bd367cc559675dfcb3e2cc06f46678df8c8d09ac200be3aa72e3e1018f6`
`74fee0f6b328a07d4872d9cc24c0055755ddfaff42d8931360b01be5a68ca201`
`790052d4e1de8895f27b9f8e8a793ca30881e38aaadf4cb72ea1494c3a8fa421`
`8e21d829fd35bb5003ca9f684e9e1e34d9410570cd6f0c60cc913320d7bc86d3`
`90d7caa057aa1bfdd85717d80b81438efebfac3e4e93f957f37f53e2acb817a5`
`9a94308fac175d05986c18b45f9080b00db004721128ac5968ec442ea10b4b1e`
`9ff13e0b09f6cc091c731f2f31156d7f22f8b55ba90a942b87665dd8265b864d`
`a4d11246417b974b307134bf418c7f5c064b2c2d27b04d66aad21da8a0402bde`
`a662c44567c8fd83bbb49bff70da518565b180ec9907e3983837e0246ce88e2d`
`b0813151265a9fb789d2d29579ecb6391c5022d11a65ed4c620740ffcabddc44`
`b5e0dfca470779d7cd614832777d6323c0f99c39054c499f06335d7e726ffd7c`
`c086c1142273d7589fff8d2c0f618660470f623e4ce27ba61d25729eb49ffa26`
`c8b053d48ca41dae36f03ecdc0576f8b4dce657d9b016f01efd3c8bdcff5751a`
`c9d873cbedfc31c3af3dbe22d7d62d0ab94f6ded9dcb858d99c3908bd627521a`
`e2e27e6eba9e15fb02a99580f26a24b7c2926eff70b230cde70ef99476f35a1a`
`e8a34ccd6158bf17cdd1a8493d964a1c3dd5edf130238224044bbf5047ea00cf`
#### Coverage
Product| Protection
—|—
Secure Endpoint| 
Cloudlock| N/A
CWS| 
Email Security| 
Network Security| 
Stealthwatch| N/A
Stealthwatch Cloud| N/A
Secure Malware Analytics| 
Umbrella| N/A
WSA| N/A
#### Screenshots of Detection
#### Secure Endpoint
#### Secure Malware Analytics
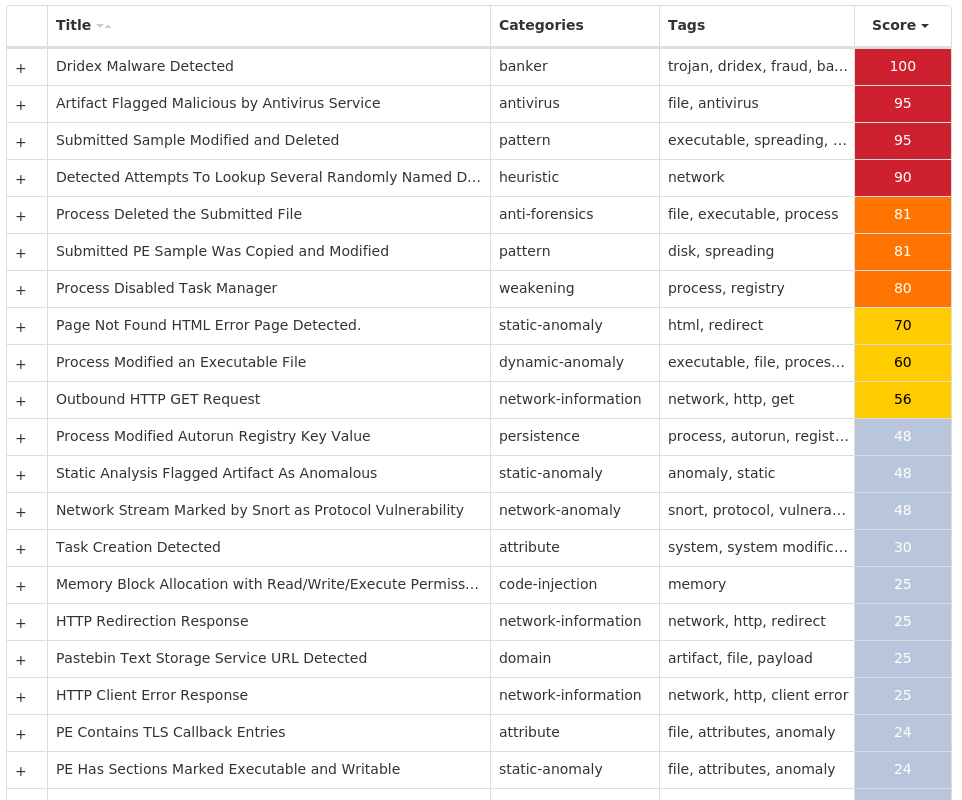
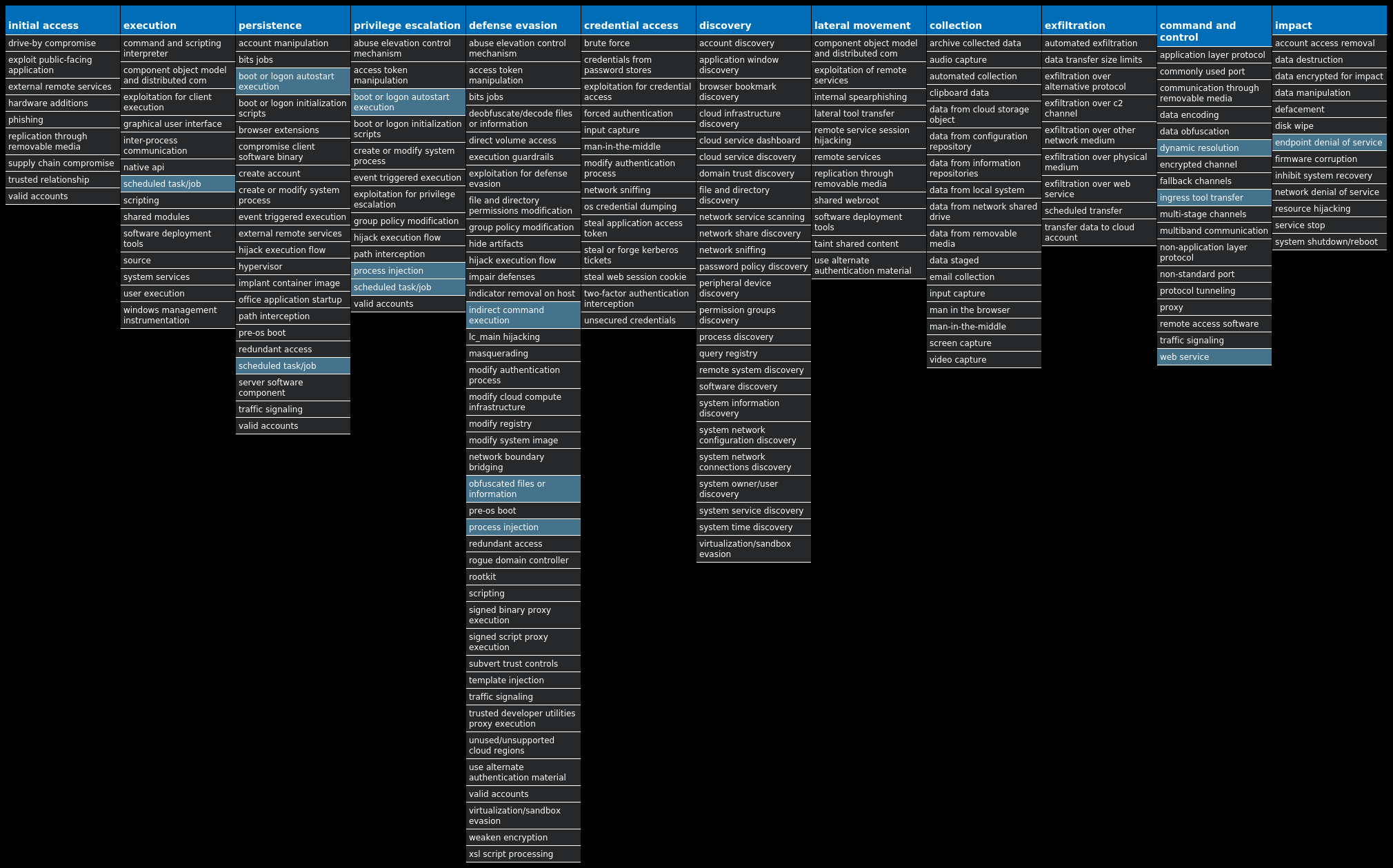
#### MITRE ATT&CK
* * *
### Win.Packed.njRAT-10005525-1
#### Indicators of Compromise
* IOCs collected from dynamic analysis of 91 samples
Registry Keys| Occurrences
—|—
`SOFTWAREMICROSOFTWINDOWS NTCURRENTVERSIONSCHEDULETASKCACHETASKS
Value Name: Path`| 2
`SOFTWAREMICROSOFTWINDOWS NTCURRENTVERSIONSCHEDULETASKCACHETASKS
Value Name: Hash`| 2
`SOFTWAREMICROSOFTWINDOWS NTCURRENTVERSIONSCHEDULETASKCACHETASKS
Value Name: Triggers`| 2
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: 0b2592d5bed09772be6f2120ec5d1e38`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: 8bc2449a0b4cae186dff71d874ecdd87`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: 74cdfe74037de0ebe063775a7be8d61a`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: 09830ddf01a042c930963250c1b2cbb9`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: 49879c18dd0a980ea7348c138e510ac1`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: 8a258bb2745a1ee39524e97dccc49ac3`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: 9bf535e06a1626c1a04514e4e7e60f3c`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: f5216625d81896bb7f49a4c94fade2d5`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: 166c0d067030a42b438a748228b9c466`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: 6462944e37e52e33dce88bf226802c41`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: 4c0288488a0673a8f068842bcaa1eacd`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: 7e222b88435d7fdadee551ee08735103`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: d4e4bba65005822ede934e597684e25a`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: 35e466437eb1ebc61c9f46ca2bbf5bc8`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: 087ffa5bebc0f6982f76d5d465437e42`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: c89e814d4b827b97e2dec133552e2bb3`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: 1a723ba0bd7d3fdd081709949ec9a96d`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: 36684bc19336ad3c85d296d273c3b5ba`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: 522dcda6332f8fccbf277125a6b42b4a`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: 991bf530df55926dc26eedc261e748fd`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: f6ccb4d45196e32da740e90956ea5435`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: 11008ae525da4c3e48917b0e8f498699`| 1
Mutexes| Occurrences
—|—
`3bX4sJbA7K9pPu6V`| 1
`i1cBWf2dmosiaxFd`| 1
`QIIXTdrPWoBnhCHq`| 1
`CJa3depjkhz3Rrrz`| 1
`ljKzvz6mJDSTHsWK`| 1
`pTPz2lb6DYSu2BOH`| 1
`IqHiRcbuVnbxVcvI`| 1
`AQ7McAOn48gsMrao`| 1
`hZ3Y3pVPLfGoDuyt`| 1
`Co4sLNQFf87ujG8A`| 1
`q8cjIFLdoXfkFfVD`| 1
`k5P9hMH9jGFDLszo`| 1
`GKNiwCrZVGLnFY2s`| 1
`H4Y5eQv9rQ6DsZho`| 1
`79afw86ZTQhYbwqr`| 1
`HjNwpDYzmRCLWXfj`| 1
`Bh7a1PoudAiFeAk9`| 1
`WlQ8d0s81SOpQQ0S`| 1
`nR335S89cB4gOSbp`| 1
`ecf0u5N2rEixFNpn`| 1
`sqEor2xkqS0Cycit`| 1
`DV8bYNJi3uczdksS`| 1
`70rrfj9Vryz3Nek0`| 1
`XSLvYVsJZs3bsiZr`| 1
`hP1Pl4miMfRFMFLU`| 1
*See JSON for more IOCs
IP Addresses contacted by malware. Does not indicate maliciousness| Occurrences
—|—
`208[.]95[.]112[.]1`| 91
`193[.]161[.]193[.]99`| 16
`209[.]25[.]140[.]180/31`| 13
`209[.]25[.]140[.]211`| 11
`209[.]25[.]140[.]229`| 5
`187[.]84[.]121[.]138`| 3
`3[.]68[.]56[.]232`| 2
`3[.]67[.]15[.]169`| 2
`18[.]198[.]77[.]177`| 2
`52[.]28[.]112[.]211`| 2
`185[.]230[.]55[.]72`| 2
`3[.]125[.]223[.]134`| 1
`3[.]125[.]209[.]94`| 1
`3[.]124[.]142[.]205`| 1
`35[.]158[.]159[.]254`| 1
`3[.]126[.]224[.]214`| 1
`3[.]125[.]188[.]168`| 1
`18[.]192[.]31[.]165`| 1
`3[.]67[.]161[.]133`| 1
`3[.]64[.]4[.]198`| 1
`209[.]25[.]140[.]212`| 1
`18[.]158[.]58[.]205`| 1
`209[.]25[.]140[.]223`| 1
`212[.]187[.]4[.]161`| 1
`85[.]66[.]212[.]235`| 1
*See JSON for more IOCs
Domain Names contacted by malware. Does not indicate maliciousness| Occurrences
—|—
`ip-api[.]com`| 91
`prevalent-63525[.]portmap[.]host`| 3
`white-camcorders[.]at[.]ply[.]gg`| 3
`lake-region[.]at[.]ply[.]gg`| 3
`hxd-54486[.]portmap[.]host`| 3
`m0m0w3b-55979[.]portmap[.]host`| 3
`4[.]tcp[.]eu[.]ngrok[.]io`| 2
`7[.]tcp[.]eu[.]ngrok[.]io`| 2
`considered-arrest[.]at[.]ply[.]gg`| 2
`q-medicaid[.]at[.]ply[.]gg`| 2
`countries-knights[.]at[.]ply[.]gg`| 2
`deletedapo-46418[.]portmap[.]host`| 2
`head-transit[.]at[.]ply[.]gg`| 2
`5[.]tcp[.]eu[.]ngrok[.]io`| 1
`6[.]tcp[.]eu[.]ngrok[.]io`| 1
`0[.]tcp[.]eu[.]ngrok[.]io`| 1
`ed-sleeping[.]at[.]ply[.]gg`| 1
`based-calculation[.]at[.]ply[.]gg`| 1
`ms-slovakia[.]at[.]ply[.]gg`| 1
`existing-bios[.]at[.]ply[.]gg`| 1
`wasted9sss1-42260[.]portmap[.]host`| 1
`which-wicked[.]at[.]ply[.]gg`| 1
`katarina1[.]ddns[.]net`| 1
`society-mastercard[.]at[.]playit[.]gg`| 1
`support-gone[.]at[.]ply[.]gg`| 1
*See JSON for more IOCs
Files and or directories created| Occurrences
—|—
`%APPDATA%MICROSOFTWINDOWSSTART MENUPROGRAMSSTARTUP.exe`| 16
`%APPDATA%a5cd4f0b99bdf067173acf84d35d4420.exe`| 1
`%APPDATA%9b652cfeeeba0e8895cbb61a14d7288a.exe`| 1
`%APPDATA%MicrosoftWindowsStart MenuProgramsStartup9b652cfeeeba0e8895cbb61a14d7288a.exe`| 1
`%System32%Tasksa5cd4f0b99bdf067173acf84d35d4420`| 1
`%System32%Tasks9b652cfeeeba0e8895cbb61a14d7288a`| 1
`%APPDATA%4bc880598bd07233f93104a7e6561610.exe`| 1
`%APPDATA%MicrosoftWindowsStart MenuProgramsStartup4bc880598bd07233f93104a7e6561610.exe`| 1
`%APPDATA%44a60f57e78721124291fcf664cc3a0e.exe`| 1
`%System32%Tasks4bc880598bd07233f93104a7e6561610`| 1
`%APPDATA%MicrosoftWindowsStart MenuProgramsStartup44a60f57e78721124291fcf664cc3a0e.exe`| 1
`%System32%Tasks44a60f57e78721124291fcf664cc3a0e`| 1
`%APPDATA%834a90d3bdf682a1a8a546e336afe6af.exe`| 1
`%APPDATA%MicrosoftWindowsStart MenuProgramsStartup834a90d3bdf682a1a8a546e336afe6af.exe`| 1
`%System32%Tasks834a90d3bdf682a1a8a546e336afe6af`| 1
`%APPDATA%MicrosoftWindowsStart MenuProgramsStartupd0d8fd8abb162af4bdb69572399956d3.exe`| 1
`%APPDATA%d0d8fd8abb162af4bdb69572399956d3.exe`| 1
`%System32%Tasksd0d8fd8abb162af4bdb69572399956d3`| 1
`%APPDATA%2b50540c53ab7d1c24c07f9525c54509e72c73a99d4a96365365d2799bfeecb.exe`| 1
`%APPDATA%1129d910145211033817289e086467903492b1c24a572521486518ff93916a74.exe`| 1
`%System32%Tasks2b50540c53ab7d1c24c07f9525c54509e72c73a99d4a96365365d2799bfeecb`| 1
`%APPDATA%153954284c10d9cf8a2d6197f2f98ca1c47e0a4c3dfdf8701d010afda794a6a5.exe`| 1
`%System32%Tasks1129d910145211033817289e086467903492b1c24a572521486518ff93916a74`| 1
`%APPDATA%a977484f6f9467af7eccef84a1d1522e04d8daf395fbd82e75c25a55b405ead.exe`| 1
`%System32%Tasks153954284c10d9cf8a2d6197f2f98ca1c47e0a4c3dfdf8701d010afda794a6a5`| 1
*See JSON for more IOCs
#### File Hashes
`023fedd1d56923cedd19fa8692a1d5f07f44a674322a69b25db1f5d1ba1721d6`
`02b50540c53ab7d1c24c07f9525c54509e72c73a99d4a96365365d2799bfeecb`
`030091e9ef98945ae7fec16072d9f8fb20f15f160389b8f7b0e60a7958e76478`
`04ed989aacedc61f1b245e72672dfe559e8a5a2612fb4c771b0c67c2f16c8eed`
`08a5fa046337acac2e274a197ba5344767a064288df49f9c9c04f33cb37d779d`
`091a9232a700d62a7131fc0b9b7d1885f9bfaa89414b7d68a23860d2e6e25a45`
`09f6d9681dcaadd0b66b76155abeff18d68bce3b0f50fbd104194bb6c071eb2e`
`0a977484f6f9467af7eccef84a1d1522e04d8daf395fbd82e75c25a55b405ead`
`0ade718a67d661f925e622044e0553692862976b1968a082537a6ceab77b0f0b`
`0cb9b0d229cc0081f0431b39cb5f1a88b5035bbf38e94fb067a77d40006e3333`
`0de1e6d211afd3613d88877a823b4c8d744d74c9125e5fa23956a0d511ab4a8d`
`0f47c2495d90cf0dacea0c9f45548862bf2574c7c4bd4350c8fb4716f34b4825`
`0f4fac4068cac09d0cbd2f6588fe70e154f15ef39d1a3490e0c580ac11e358e7`
`1129d910145211033817289e086467903492b1c24a572521486518ff93916a74`
`1294e9765dc4d6fdf8c09309552d594e81abb0a87da71565e95e9ca2baf53f9b`
`135d9b51af134429131b1b0fa6b3cbb86dc32ca5730fd7a1fef91e36bb8e9b3d`
`153954284c10d9cf8a2d6197f2f98ca1c47e0a4c3dfdf8701d010afda794a6a5`
`1ae3b1b699cc598232039ab3eb87f3981abb458494b2cea0553cef46bb01a4a1`
`1e990d15311ae6f3281a30755a04db031e82bcd71de9d648a7804a43c97db489`
`1ea7a92374bf5ae3f9e6b3a84666b0b871e9dc48df95c1214690a402e08a15ce`
`1f0346cf39bb2e8b7ffa37640738072fa201e36dccd4f3caba5757103928d73f`
`2296b5ef4a6d30247835f12fbdfa618669b140ce0d1594031c52374c33e39975`
`2311cbef005dbe928ea0d9c734ccd84ba682003301b9f283d2da155268df58fa`
`2317961afafb8424846335de62fed00e9102b2c7acc415567c43df808340c29f`
`2483ae5ef59e5500981f69792add63f8287402f7020a84119379009d26939015`
*See JSON for more IOCs
#### Coverage
Product| Protection
—|—
Secure Endpoint| 
Cloudlock| N/A
CWS| 
Email Security| 
Network Security| 
Stealthwatch| N/A
Stealthwatch Cloud| N/A
Secure Malware Analytics| 
Umbrella| 
WSA| 
#### Screenshots of Detection
#### Secure Endpoint
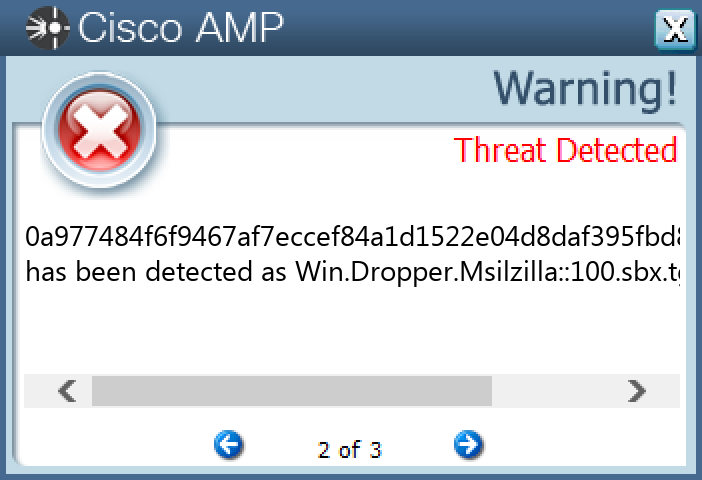
#### Secure Malware Analytics

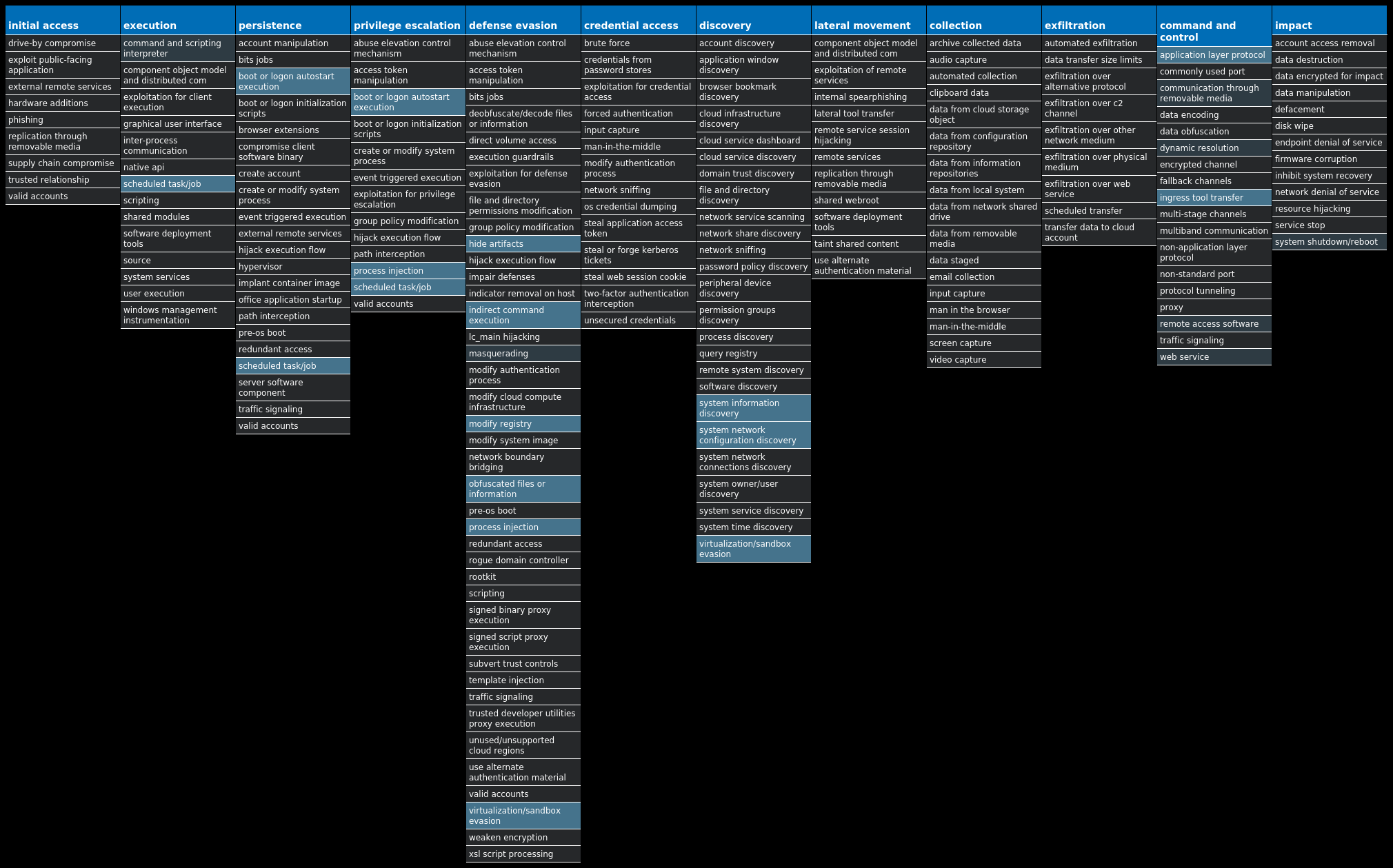
#### MITRE ATT&CK
* * *
### Win.Packed.Azorult-10005443-0
#### Indicators of Compromise
* IOCs collected from dynamic analysis of 16 samples
Mutexes| Occurrences
—|—
`Localfadce40ba6f0cccb5201fbe46cd59acdaf356acc`| 16
`dfgekrgoerkgopskdwefjiweafasfminewiognowes`| 16
IP Addresses contacted by malware. Does not indicate maliciousness| Occurrences
—|—
`45[.]140[.]147[.]214`| 10
`172[.]67[.]34[.]170`| 8
`104[.]20[.]67[.]143`| 7
`104[.]20[.]68[.]143`| 1
`34[.]117[.]59[.]81`| 1
`23[.]221[.]227[.]176`| 1
Domain Names contacted by malware. Does not indicate maliciousness| Occurrences
—|—
`pastebin[.]com`| 16
`ipinfo[.]io`| 1
`apps[.]identrust[.]com`| 1
Files and or directories created| Occurrences
—|—
`%TEMP%RarSFX0`| 16
`%APPDATA%MicrosoftWindowsStart MenuProgramsStartupSystem32.exe`| 16
`%TEMP%RarSFX0system32.exe`| 16
`%TEMP%tmp.tmp`| 10
`%TEMP%RarSFX0ChatGPT-4 Online.exe`| 2
`%TEMP%8LxnTgFTBZ.bat`| 1
`%TEMP%UETUBSwFNh`| 1
`%TEMP%aRMq8s2PZu`| 1
`%TEMP%Ar8UVsFFH`| 1
`%TEMP%add4oKeLWK`| 1
`%TEMP%rOqL1SoRtH.bat`| 1
`%TEMP%EglYUAkHS5`| 1
`%TEMP%4y6pq4Mdxm`| 1
`%TEMP%FEB5JxBvcP`| 1
`%TEMP%57GSqsql8L.bat`| 1
`%TEMP%csHnJfxfgw`| 1
`%TEMP%8qPGiyvjgx`| 1
`%TEMP%plAJRGijyy.bat`| 1
`%TEMP%XzKdA23rT8`| 1
`%TEMP%RarSFX0Cyber Ghost VPN 2023.exe`| 1
`%TEMP%WaJhssybhA`| 1
`%TEMP%XwytQc2jxF`| 1
`%TEMP%q9ZCrYAkiS`| 1
`%TEMP%zSrmjrCHbC`| 1
`%TEMP%RarSFX0BLTools v2.1.2.exe`| 1
*See JSON for more IOCs
#### File Hashes
`05c0d569f272ccb96a820ee096177c1303a3e0aa19ab98468e8237c33c6af37a`
`3b552bdcaa5dacf399416f3db53c1cce8631d97e9e8d23410b5195400504a674`
`5d868eba69e85085ea0b8baac4398297e012d2c00d376bd74414b73efe05b3a3`
`5ee5e591bb2ef8a32f74e08936129f473c1d66a9c61ca454ad86fd6c9a3451d0`
`66ad0798cdc38b13fade98886142b555ceb0097a82db1f509a6c3e8034b278ea`
`72d53a6bed17fb482a405cd140160aa8a728e8912c88172e4e04098437786188`
`82c6e1212af6da4a6a5a4428c9f51736999680daf5b75395082ab3139d6e28c2`
`8a6672b8b7165db85a63750a12a89f8c0d55f7f2a98042f25be8740324469ecc`
`9759b11c05da965795091bdf9d1e51d9c0e3f90712ae1afd198b93d8ff1f5cb9`
`b03e2c049c90e8245e9d3135a24515cce921ac529ddb0395ed2401c4cbe92fb8`
`ba3adebd723bc59f52fcadcd698c651ce61ed6fb099d6583383edab66ac34f2f`
`bfbf48fb4dd150dbc6c34b309dc308326a5b9ab40defafbe32060236243fe8ba`
`d618502188cb64718b8aed6a9343c65f6e319ce8c9f750855176f5b575a6807a`
`daa375be093d880a65d9ce51c2b9127169dfce292c295c93dd4fb3dbc9b61b23`
`e97912bb807c184d0cd506c9ecf6948ce0ae7a582b1eebb70ef29c8d8e999be1`
`f8d79c98ef9080e10beb0760437bdadfed580347a423ee09fead93ec9d6a7b4a`
#### Coverage
Product| Protection
—|—
Secure Endpoint| 
Cloudlock| N/A
CWS| 
Email Security| 
Network Security| 
Stealthwatch| N/A
Stealthwatch Cloud| N/A
Secure Malware Analytics| 
Umbrella| N/A
WSA| N/A
#### Screenshots of Detection
#### Secure Endpoint

#### Secure Malware Analytics
#### MITRE ATT&CK
* * *
### Win.Worm.Vobus-10005311-1
#### Indicators of Compromise
* IOCs collected from dynamic analysis of 63 samples
Registry Keys| Occurrences
—|—
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONEXPLORERADVANCED
Value Name: ShowSuperHidden`| 63
`SOFTWAREPOLICIESMICROSOFTWINDOWSWINDOWSUPDATEAU`| 63
`SOFTWAREPOLICIESMICROSOFTWINDOWSWINDOWSUPDATEAU
Value Name: NoAutoUpdate`| 63
`SOFTWAREPOLICIESMICROSOFTWINDOWSWINDOWSUPDATE`| 63
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: bzxuij`| 2
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: vuinues`| 2
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: ciheq`| 2
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: tuizao`| 2
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: liuoday`| 2
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: lauugoj`| 2
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: rafid`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: wiociey`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: hauuyuk`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: leemiok`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: coakau`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: vaaji`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: waepow`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: slhus`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: jqkaj`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: vieyeg`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: jeowo`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: vaueriq`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: feaic`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: tueek`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: voeifis`| 1
Mutexes| Occurrences
—|—
`A`| 63
IP Addresses contacted by malware. Does not indicate maliciousness| Occurrences
—|—
`199[.]59[.]243[.]223`| 3
`212[.]32[.]237[.]92`| 2
`212[.]32[.]237[.]90/31`| 2
`212[.]32[.]237[.]101`| 1
`23[.]82[.]12[.]32`| 1
`76[.]223[.]26[.]96`| 1
Domain Names contacted by malware. Does not indicate maliciousness| Occurrences
—|—
`ns1[.]chopsuwey[.]com`| 63
`ns1[.]chopsuwey[.]net`| 53
`ns1[.]chopsuwey[.]org`| 53
`ns1[.]chopsuwey[.]biz`| 53
`ns1[.]chopsuwey[.]info`| 53
Files and or directories created| Occurrences
—|—
`autorun.inf`| 63
`System Volume Information.exe`| 63
`$RECYCLE.BIN.exe`| 63
`Secret.exe`| 63
`Passwords.exe`| 63
`Porn.exe`| 63
`Sexy.exe`| 63
`E:autorun.inf`| 63
`E:$RECYCLE.BIN.exe`| 63
`E:Passwords.exe`| 63
`E:Porn.exe`| 63
`E:Secret.exe`| 63
`E:Sexy.exe`| 63
`E:System Volume Information.exe`| 63
`E:x.mpeg`| 63
`.exe`| 63
`E:.exe`| 63
`%HOMEPATH%.exe`| 63
#### File Hashes
`00b230ed3040b090a11e46ebd7207355a106112323dda09ea43050aaed2ce521`
`00b3de85145ced57106d257f7266bb302c9d827239391e81b866766b6fe70f6b`
`00da5d9a6a0e1c49bc47b6523dbf7883f2f067e3315d9e10a3444fdcee4cc449`
`01043e907887d3472f6379f3586906e23a6087c9d71b70e035eea96d43366f51`
`02d2ac467b6eecd05ae1d1a62ce97c16e346b4c8a9191276a7543fb3c71e993e`
`03852fe9d85055f6a5f4d90a2cb92d2381815ff7847a7434677a4bb6df6f6921`
`0460f01fa91872b0a8931f41325941739b455c8905cb3f531f3cc3c921a20786`
`06c4946c9caa563761996f13a02a5a6d5ec6e1812e6e75e2fefd6784030c4574`
`072938f58f95ea4a2c047e243ff602300c402718b94de56138e491dcbea19df1`
`0766a841804df2fdea58be32ccb200ac721b5d26456305d810a14e4935980ac9`
`07fc95465e6ff9ff361066e2a884b8a03c8d48e1e4318ee329bccdd2cdb04894`
`0841ab260709bf50b78c24c7fe33ae736cf04b67b70de6960952a50b6e15ea60`
`091f0b3be99e7bc7f68da59eedb6f54d953b270a77bc4c0dd2aa4e9b9ff06024`
`0932d38f962865f1ec97c477b5d6443c0ceea27db4377df54a62adf8f3bb72ab`
`094f2f6350a4e45f0a00a6080c5beb701157f741c2ed12a6eaf80ebd8e28fb34`
`09861dbfac06f827f0d5dd5f39a2a39bfc7873bba36d9a581c5d573ad28cf111`
`0a18bd843c034727700b5af482c15bc3b4b84c038728ff4dca2fe305673facf9`
`0a9cfb2aad70e78ce59a29b98a9be61cf6ecfd9720184977b1a8d1b5bdac6fc7`
`0aa783e2ab54c5bd004e3d5de90cd5388b87aa193e488d93593f74a99870822a`
`0be2cc908e48d871942d32c749340e89207226a2d6069afa799912f76ad8ba05`
`0c0f8266b4a01b4237847c05eca16cc276e9856cd59901e038cf6dfa9bb92c44`
`0e719bdf2a4a04eb06524a79e294451464abd7c9262efff5988bf32ca135ee1c`
`0ec9e7c9648970a700177f81a9df8bbf2903c49cf57d8b476c960791f9a1b83f`
`0f23de73c22b3ee5b70175866b76ce13ee5fceb2251b8de5713c182895b1d9fa`
`0f3d7037a30dd4eb7ddd018165a5d33d0b88873e9ff8944c65d7cfe674ea5ede`
*See JSON for more IOCs
#### Coverage
Product| Protection
—|—
Secure Endpoint| 
Cloudlock| N/A
CWS| 
Email Security| 
Network Security| N/A
Stealthwatch| N/A
Stealthwatch Cloud| N/A
Secure Malware Analytics| 
Umbrella| 
WSA| 
#### Screenshots of Detection
#### Secure Endpoint
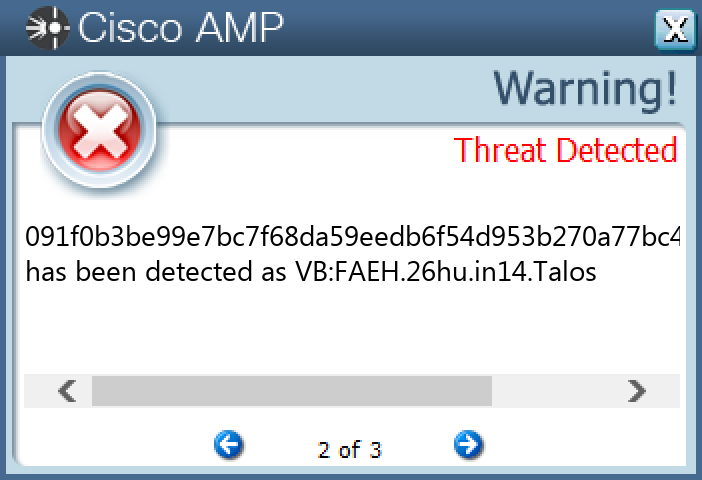
#### Secure Malware Analytics
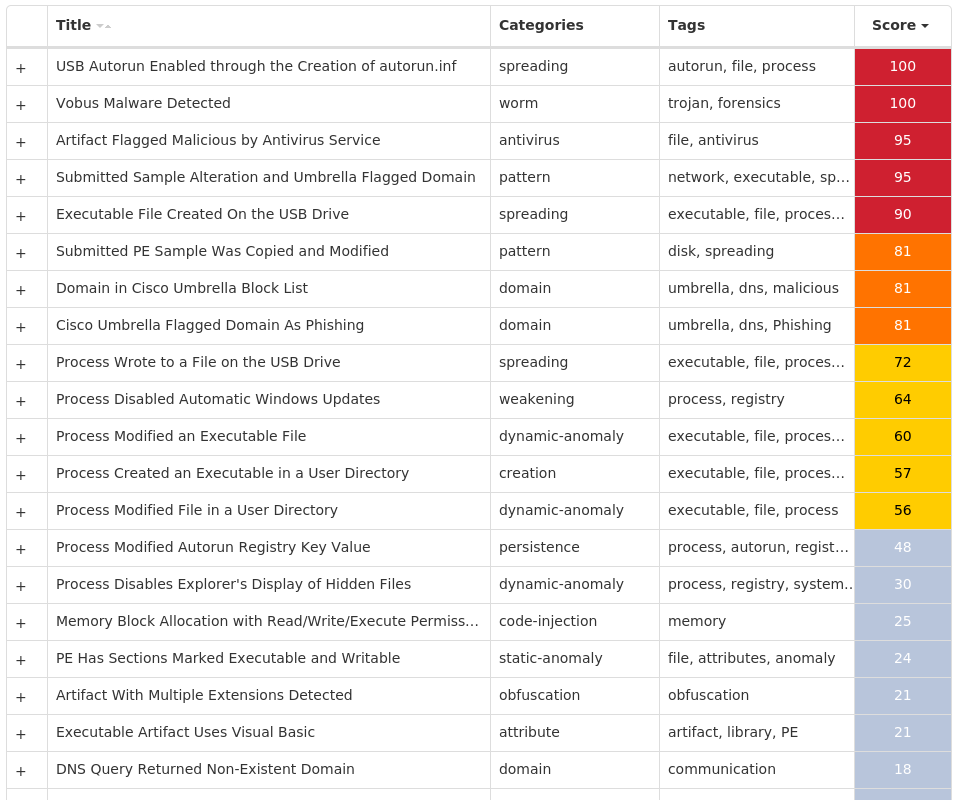
#### MITRE ATT&CK
* * *
### Win.Packed.Zusy-10005219-0
#### Indicators of Compromise
* IOCs collected from dynamic analysis of 27 samples
Registry Keys| Occurrences
—|—
`SYSTEMCONTROLSET001SERVICES\PARAMETERSINTERFACESTCPIP_{9EB90D23-C5F9-4104-85A8-47DD7F6C4070}
Value Name: DhcpNetbiosOptions`| 1
`SYSTEMCONTROLSET001SERVICES\PARAMETERSINTERFACESTCPIP_{9EB90D23-C5F9-4104-85A8-47DD7F6C4070}
Value Name: DhcpNameServerList`| 1
`SYSTEMCONTROLSET001SERVICES\PARAMETERS
Value Name: DhcpScopeID`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONEXPLORERSTARTPAGE
Value Name: StartMenu_Balloon_Time`| 1
IP Addresses contacted by malware. Does not indicate maliciousness| Occurrences
—|—
`188[.]120[.]194[.]101`| 27
`104[.]18[.]114[.]97`| 15
`104[.]18[.]115[.]97`| 12
`173[.]248[.]22[.]227`| 5
`178[.]214[.]221[.]89`| 5
`69[.]144[.]171[.]44`| 4
`98[.]222[.]64[.]184`| 3
`173[.]248[.]31[.]1`| 3
`98[.]246[.]210[.]27`| 3
`71[.]194[.]36[.]73`| 3
`24[.]19[.]25[.]40`| 3
`208[.]123[.]130[.]173`| 3
`24[.]220[.]92[.]193`| 2
`109[.]86[.]226[.]85`| 2
`66[.]196[.]61[.]218`| 2
`65[.]33[.]236[.]173`| 2
`69[.]163[.]81[.]211`| 2
`173[.]248[.]31[.]6`| 2
`71[.]99[.]130[.]24`| 2
`68[.]119[.]5[.]32`| 2
`64[.]111[.]36[.]35`| 2
`173[.]248[.]27[.]163`| 2
`97[.]92[.]125[.]74`| 2
`98[.]204[.]215[.]92`| 2
`24[.]148[.]217[.]188`| 1
*See JSON for more IOCs
Domain Names contacted by malware. Does not indicate maliciousness| Occurrences
—|—
`icanhazip[.]com`| 27
Files and or directories created| Occurrences
—|—
`%TEMP%razacer.exe`| 27
#### File Hashes
`06083b300390634454ad9514dcb76dc292eba525af7f4f6fb88a88a030d0137d`
`0725f9403e693eb417343f5ebef2fb8b20c17573c50c49dbea7472e1acd18f89`
`07a54115a35c502296f144ab1ac063f864625740eed210bf629ae1d90c9f854c`
`0bb14de5996c44ca206c9d1478552d43734e742011570024979432a8df791e99`
`169218c7d50803982b06a8120697f5fb06dd7b20aa5b5553ea3efeb6b6fd3be5`
`18164491280f48454547e2da06e674aad8bccf34b5553126b69f6a58278f7b21`
`249810e968de4a12fa3ee4e03de6ae42e8f847c1204c727a75be9db8911b8da4`
`25634be35352d5a07898857fecd62f480add2eabc7fe27804dab7f902824ce91`
`2ff0e715a62f844013326b7f54ea64c8b2a9bf9f68486aca4d6cdb06de2150bc`
`3c705dc7d93b66549cac81441570b60889c2c64bcbb83e6e2c18437428aa73e6`
`42d4defa7c09129009f8abd4fbdb40c1ccf108eb489cf93c7426fd0e4c7fc736`
`4396a3b692ade1b12b46b2563d30a52b9fe9b72e994f963733bb4277e93f7f0c`
`4e8189a5d0a36afece1dbc25d022c0e129ec63ea9c56e2964a2407d1ec49c744`
`516aca5b9005c1047d181e81e032d56d016f164434714e79bdaae190b0925d7d`
`583108ea56a262d7b44b1bd95f5b37fb72b877238d8c303f973a20d9ec937703`
`593814354f8668818c8eae406f77124745904dee97693bc5e76415cdc48ddf1a`
`5cc7155737abff0909fc82c2ccf83271d243103b849f9bf3c373c57a058a346b`
`5d2210e4072588e6dec44e5a3cde746af95f360e19d0a40118bd05c84d88755c`
`5fcb277befd5cc98b19eafaf75dd2c9ca702d11fbd18b8237e27fae489fffec7`
`719f3e2bae12ec1df14690ce4fce04b2c8513126b639842903fe0c973ad12dd1`
`774be5523ba128c6f3337f18c856eaa8bd91b7caa6c9b1d877efc667f9144056`
`7a0f2400ffbc9b97ec7686eacf526225f17effc9e9305f15ed84504ed01e65bf`
`7e910440620fdaf0cefab1be85029f602455af04f90efbe5c64383757978ee6b`
`81c13a0a8f8e3e7e542f64527b02fcad467a4322f1e9912e0e4e02d14fdb7c56`
`823dc8ce419bacd53d23884a1d604063e406d50165fb33ac69067b1dc3a34f32`
*See JSON for more IOCs
#### Coverage
Product| Protection
—|—
Secure Endpoint| 
Cloudlock| N/A
CWS| 
Email Security| 
Network Security| 
Stealthwatch| N/A
Stealthwatch Cloud| N/A
Secure Malware Analytics| 
Umbrella| N/A
WSA| N/A
#### Screenshots of Detection
#### Secure Endpoint

#### Secure Malware Analytics
#### MITRE ATT&CK
* * *
### Win.Packed.Upatre-10005147-0
#### Indicators of Compromise
* IOCs collected from dynamic analysis of 27 samples
IP Addresses contacted by malware. Does not indicate maliciousness| Occurrences
—|—
`93[.]185[.]4[.]90`| 25
`193[.]122[.]130[.]0`| 6
`132[.]226[.]247[.]73`| 6
`132[.]226[.]8[.]169`| 6
`173[.]216[.]247[.]74`| 5
`193[.]122[.]6[.]168`| 5
`84[.]246[.]161[.]47`| 4
`77[.]48[.]30[.]156`| 4
`64[.]184[.]183[.]20`| 4
`158[.]101[.]44[.]242`| 4
`76[.]84[.]81[.]120`| 3
`24[.]148[.]217[.]188`| 3
`216[.]254[.]231[.]11`| 3
`72[.]174[.]240[.]148`| 3
`63[.]248[.]156[.]246`| 3
`72[.]175[.]10[.]116`| 3
`74[.]116[.]183[.]136`| 3
`64[.]111[.]36[.]52`| 2
`178[.]222[.]250[.]35`| 2
`85[.]135[.]104[.]170`| 2
`217[.]168[.]210[.]122`| 2
`104[.]174[.]123[.]66`| 2
`24[.]33[.]131[.]116`| 2
`24[.]220[.]92[.]193`| 2
`188[.]255[.]239[.]34`| 2
*See JSON for more IOCs
Domain Names contacted by malware. Does not indicate maliciousness| Occurrences
—|—
`checkip[.]dyndns[.]org`| 27
Files and or directories created| Occurrences
—|—
`%TEMP%elarvolume.exe`| 27
#### File Hashes
`03795bdcc508f78484839595f6f02cb0c8e436403f221d61d8e72bdd9537532a`
`07bc9395bad712c89043162111deb1e2d7ddf231d3ad3ad744e2723ead611a1e`
`0e6e6b5de5aa9f5643c483e6055c23cfc98259f4edb900c88b87df62094a2c33`
`108b13b50bb2dd6e91893f4636c0cb42881ddcf540ab8dc7500f42babe1fa0e3`
`123238b09630d0b0a4d412425058da936535cd5d93a23a671dc3446ac3bc8f3a`
`2259416d1a17347551e38526d6f74c9e2bbcc3590ae14bea9a7ca0c725122503`
`2316cc68d9745701459c3cb5fff4e3f31d1961bcce438fdf96881b4af494196c`
`2623040cb9b5ca61bcc3ac56cf81f14f7f4d790757669e8b622f1ef52db4f9bb`
`272ada068cc6851150e7f5bcd17c403ab6ea9d1ad62c7d851f2c7568dd7c1bbc`
`29dd6f15e2a3ef0c72850b498e00b660c51082c5858ccdf68dd3888e444d5f73`
`2abfc6bd75edc3f060c8d50e98a120122e89791d2487103971dba12fc4b2c9ef`
`38472a9975c5777b029d38f3b149d452f1a95d5e194c89d2294566b2ed3cbdb7`
`389b0a459a839e8f323c1f3e1395f0ee22bb34926e523758040a05a51a2a26c9`
`48230f3752a9d8f27114ffa640fd575a1ec52511d2b116c6fa77fa06234f4b4c`
`5ba22ca3d809a8b68a08127f22dbe3b3e7e5623c990d8391542881417fe7ed15`
`5dcc3824a50f90bb980776970a748fe56d5af46e1cd57c977eb544cd6c6a2525`
`652ccf42445786444e5daa5a4a169a2c3d7fbcefd6692a0a6609760cac9a0702`
`68ca72fb9914c65ea445cf666592487a72d7ce52251eef3ecc5e04842b69d134`
`6be7bbc2fe05ac253df3e05a06b8a40b09002a72bfd7f1df9d8f36c465f1a86a`
`700c9b142a2ea5e55281df2381c3b1fa1c4fd02d87929a672fc86b256cff9de2`
`8f7f6d0542b33cdd583b9b7dab279cc39f0c4960c73aa65fb0ea6fb5a1020a99`
`8ff74c0bf36a7a8eb9416f26cc307761b1d0cb9fc8813a3e79749c898b8a371a`
`92443bb6d0a9f15410a79afb3a94f875156c4515d6d981fbf811ec14b53606f2`
`940aaeb071e193227fcae9ce88fa5dc0d7b29fbcaa037085922b75b9f84e48a7`
`97f40bf0644e2234bd6ff3e790d4fc394612d18edf3dcf9c483246d919efee96`
*See JSON for more IOCs
#### Coverage
Product| Protection
—|—
Secure Endpoint| 
Cloudlock| N/A
CWS| 
Email Security| 
Network Security| 
Stealthwatch| N/A
Stealthwatch Cloud| N/A
Secure Malware Analytics| 
Umbrella| N/A
WSA| N/A
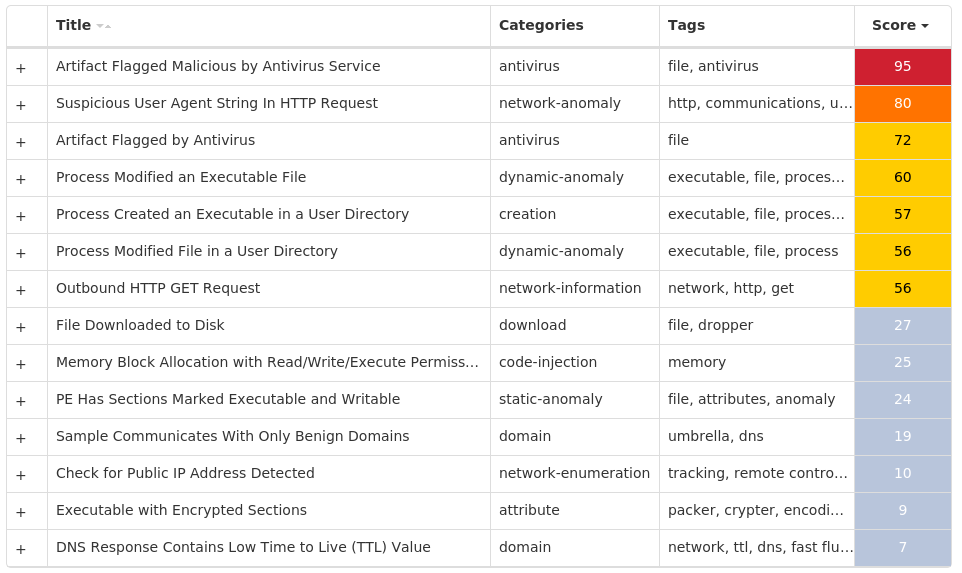
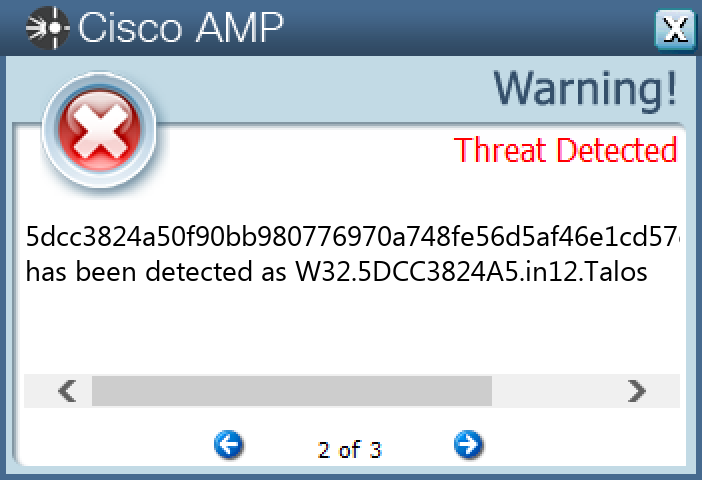
#### Screenshots of Detection
#### Secure Endpoint
#### Secure Malware Analytics
#### MITRE ATT&CK

* * *
### Win.Packed.Redline-10005632-0
#### Indicators of Compromise
* IOCs collected from dynamic analysis of 42 samples
Registry Keys| Occurrences
—|—
`SOFTWAREPOLICIESMICROSOFTWINDOWS DEFENDER
Value Name: DisableAntiSpyware`| 42
`SYSTEMCONTROLSET001SERVICESWINDEFEND
Value Name: Start`| 42
`SOFTWAREPOLICIESMICROSOFTWINDOWSWINDOWSUPDATEAU`| 42
`SOFTWAREPOLICIESMICROSOFTWINDOWSWINDOWSUPDATEAU
Value Name: NoAutoRebootWithLoggedOnUsers`| 42
`SYSTEMCONTROLSET001SERVICESWUAUSERV
Value Name: Start`| 42
`SOFTWAREPOLICIESMICROSOFTWINDOWSWINDOWSUPDATEAU
Value Name: NoAutoUpdate`| 42
`SOFTWAREPOLICIESMICROSOFTWINDOWS DEFENDERREAL-TIME PROTECTION
Value Name: DisableBehaviorMonitoring`| 42
`SOFTWAREPOLICIESMICROSOFTWINDOWS DEFENDERREAL-TIME PROTECTION
Value Name: DisableOnAccessProtection`| 42
`SOFTWAREPOLICIESMICROSOFTWINDOWS DEFENDERREAL-TIME PROTECTION
Value Name: DisableScanOnRealtimeEnable`| 42
`SOFTWAREPOLICIESMICROSOFTWINDOWS DEFENDERREAL-TIME PROTECTION
Value Name: DisableIOAVProtection`| 42
`SOFTWAREPOLICIESMICROSOFTWINDOWS DEFENDER`| 42
`SOFTWAREPOLICIESMICROSOFTWINDOWS DEFENDERREAL-TIME PROTECTION`| 42
`SOFTWAREPOLICIESMICROSOFTWINDOWSWINDOWSUPDATE`| 42
`SOFTWAREWOW6432NODEMICROSOFTWINDOWS DEFENDERFEATURES`| 42
`SOFTWAREWOW6432NODEMICROSOFTWINDOWS DEFENDERFEATURES
Value Name: TamperProtection`| 42
`SOFTWAREPOLICIESMICROSOFTWINDOWS DEFENDERREAL-TIME PROTECTION
Value Name: DisableRealtimeMonitoring`| 42
`SOFTWAREPOLICIESMICROSOFTWINDOWS DEFENDER SECURITY CENTER`| 42
`SOFTWAREPOLICIESMICROSOFTWINDOWSWINDOWSUPDATEAU
Value Name: AUOptions`| 42
`SOFTWAREPOLICIESMICROSOFTWINDOWSWINDOWSUPDATEAU
Value Name: AutoInstallMinorUpdates`| 42
`SOFTWAREPOLICIESMICROSOFTWINDOWS DEFENDER SECURITY CENTERNOTIFICATIONS`| 42
`SOFTWAREPOLICIESMICROSOFTWINDOWS DEFENDER SECURITY CENTERNOTIFICATIONS
Value Name: DisableNotifications`| 42
`SOFTWAREPOLICIESMICROSOFTWINDOWSWINDOWSUPDATEAU
Value Name: UseWUServer`| 42
`SOFTWAREPOLICIESMICROSOFTWINDOWSWINDOWSUPDATE
Value Name: DoNotConnectToWindowsUpdateInternetLocations`| 42
#### File Hashes
`013f9a67879da9274a96e9252732f1275cae7ae76cea876b256cb405881477ed`
`023a107f218ddba25a9974b938023a233de0738c94bc35a8aa1fcbf5fb5be6b2`
`0630f02d54915d443b89a0caee7e099fcf1e0be4ee5cf2e6341ac33531a6a659`
`0c5a5d3d2f150e55cf47476e5e0058ea8bcceb155a09dcc6acff0e34f773965c`
`0d2ea64a807283f0998f74e131bd95436a73e7f09d7db1cebd2a5c6160ab25a7`
`116e012f29aa293084be378f00485fb92dcfe3703eb7d687109976c5c54c7953`
`11e1492ad2c4eca711c4f120eda65391660f4a889c7df1e378f347ece9c23c3f`
`14017b66abc03e1062a6bee7b2d75a3d49fa6960f08bdb8631c8ec920784eeea`
`1413b8951a3b3a61ebc2a4947cf81f3053d924286b6c76bd2ea0d4cabcc3f6df`
`145c8037c413f00333b72c129d488eca8b900ef583f84e8370d4f1646bf5b71f`
`149e556c92aa3d90d5559a81e152b2e5edc62dd2ba9d454af1ed967ac1da0dcb`
`16674c540246f15bd1f7aaf7d450a84a81b408cb3767265e96671c974310a2dd`
`19a7ede77d763b2897bae40e13d2179434374005bf0736eb59413fef040a12c2`
`1ac843c2dbe6f48eb4a0bbc6d39479df09a7dad86821558cdc330d6c09bac924`
`1ad96dc3b615d9bbf725586c0f5abfffb2cf29c2303f27a5d92a194529264959`
`1b1f622f76d669eefc8dbc9d51f4d10747cba3521cc6073fc2dae4ef23d01aad`
`1bb6186654216b8090a26720ce9ce91ff1b279a09ee315187fc8f12237d93945`
`1cacbbb632e0141ab9562a88a0e88a668d8f451396069456b9f6b09b65b2c66b`
`1f0ecb8d77e1a2a4ad3a90626bc296288dc7dfe689b0b90d8221fd7216ffd01b`
`212792319c73f82e9a4f0691ec902f97c16e7e762a76b8776bf3d3e2373f8332`
`22aa379527abdc74bc57a59fa4c9dbec82fc714607a143506c9625ccb3473e4f`
`2810221a2656afb58b3fb2f99ff98c1c002f68a7cea35b4b2a43e1a424bc4503`
`2b4eb458a5f42d854d93daf743d0c7a6c099ff17e599c86c6ebd316c00afdc5b`
`2be65b87d98057081d253c3e880e90229e8a984c316237b95349a65bc0d72982`
`2c811d54e832c20ac045df28accb86ca3e3e1687d1c5e4552b108e699ce5b55d`
*See JSON for more IOCs
#### Coverage
Product| Protection
—|—
Secure Endpoint| 
Cloudlock| N/A
CWS| 
Email Security| 
Network Security| N/A
Stealthwatch| N/A
Stealthwatch Cloud| N/A
Secure Malware Analytics| 
Umbrella| N/A
WSA| N/A
#### Screenshots of Detection
#### Secure Endpoint
#### Secure Malware Analytics

#### MITRE ATT&CK
* * *Read More
References

Back to Main


