
Today, Talos is publishing a glimpse into the most prevalent threats we’ve observed between May 5 and May 12. As with previous roundups, this post isn’t meant to be an in-depth analysis. Instead, this post will summarize the threats we’ve observed by highlighting key behavioral characteristics, indicators of compromise, and discussing how our customers are automatically protected from these threats.
As a reminder, the information provided for the following threats in this post is non-exhaustive and current as of the date of publication. Additionally, please keep in mind that IOC searching is only one part of threat hunting. Spotting a single IOC does not necessarily indicate maliciousness. Detection and coverage for the following threats is subject to updates, pending additional threat or vulnerability analysis. For the most current information, please refer to your Firepower Management Center, [Snort.org](), or [ClamAV.net]().
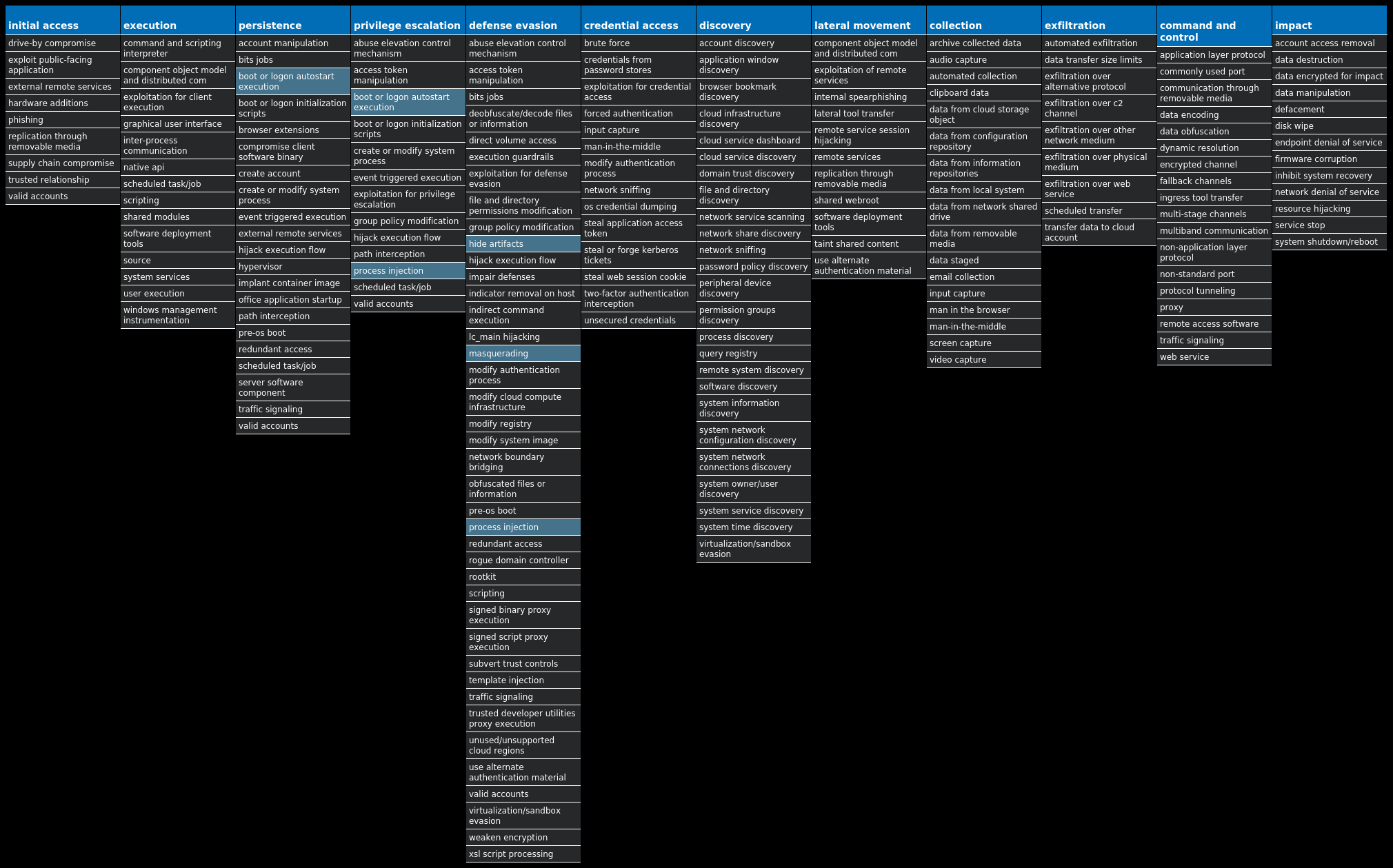
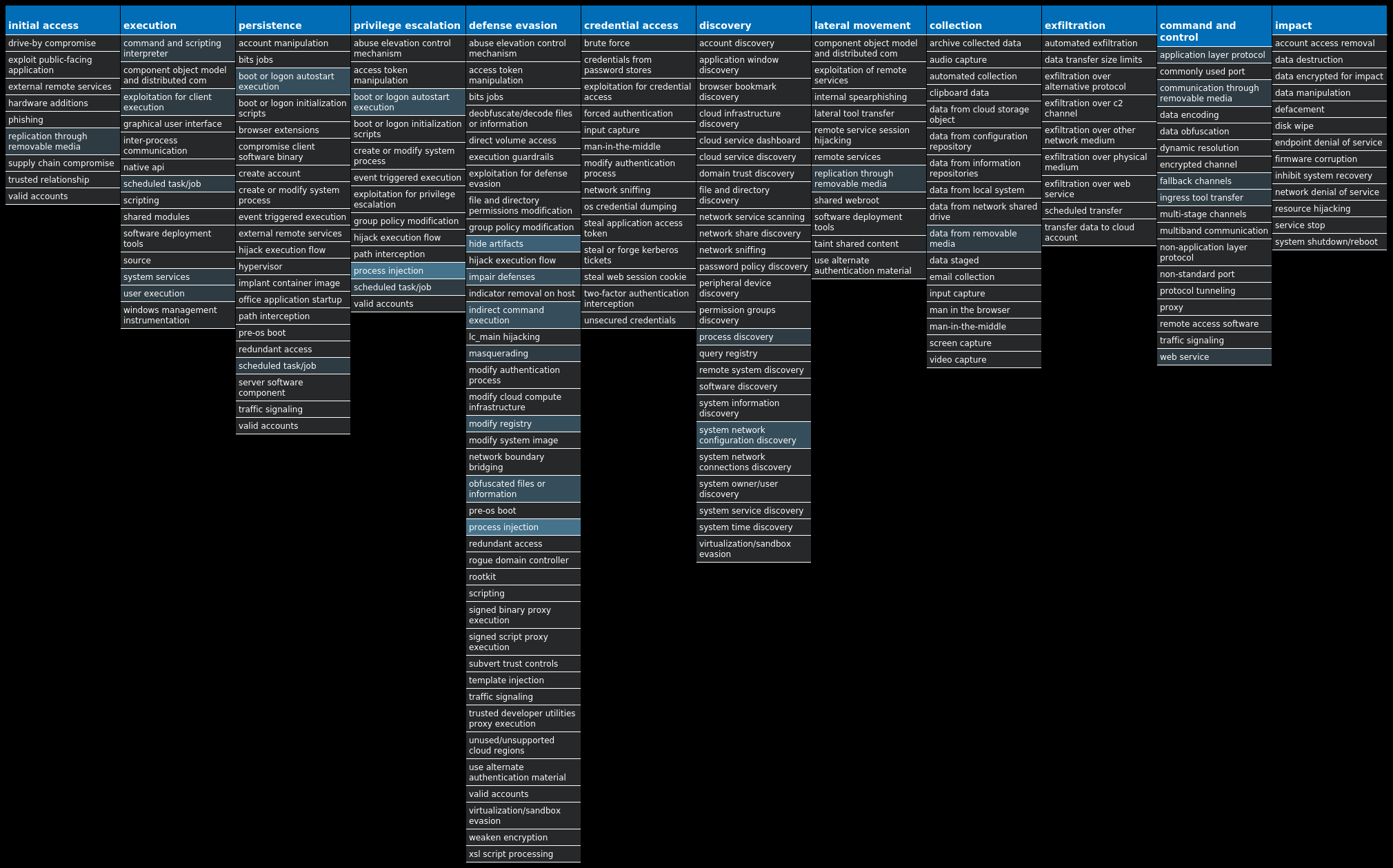
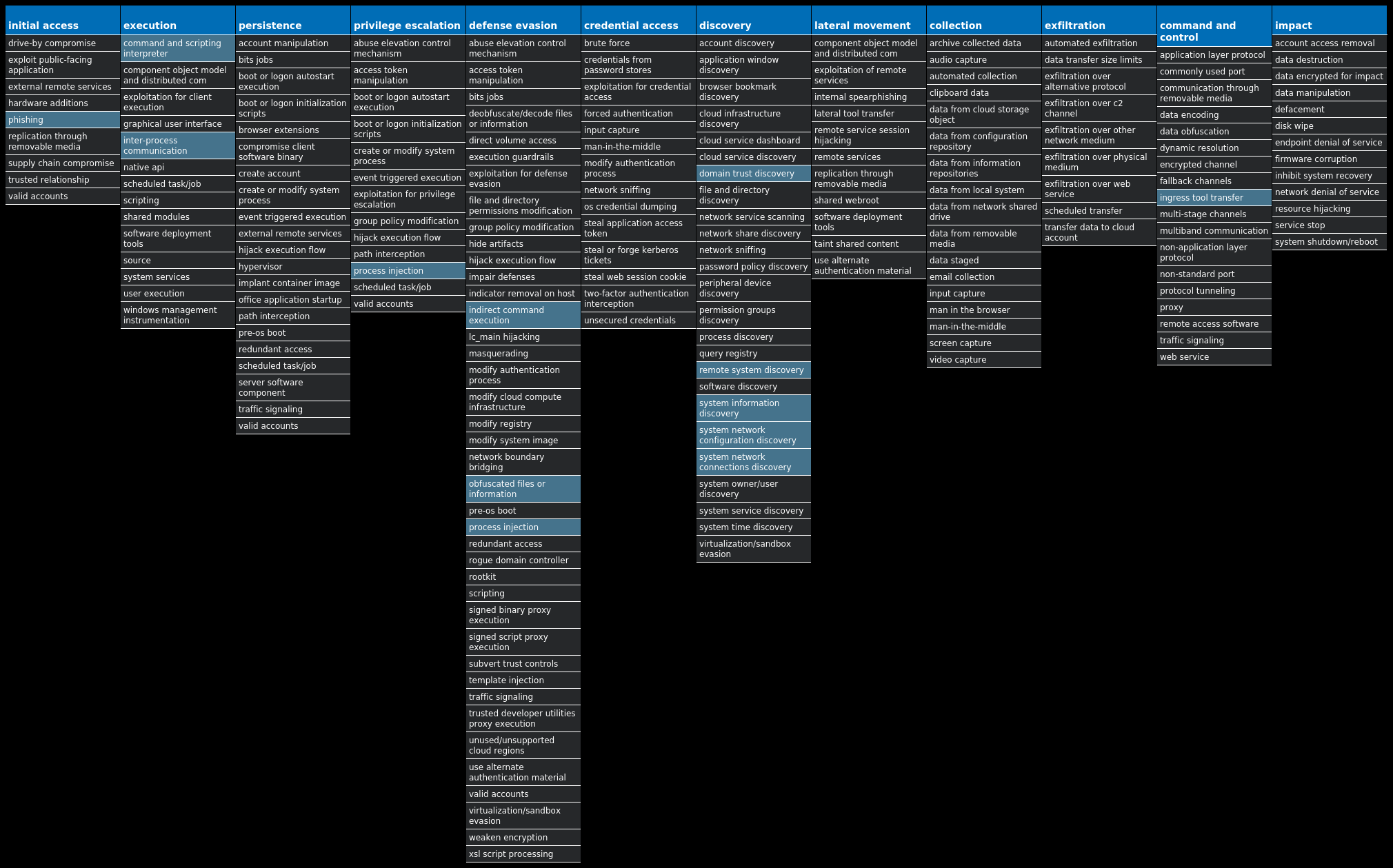
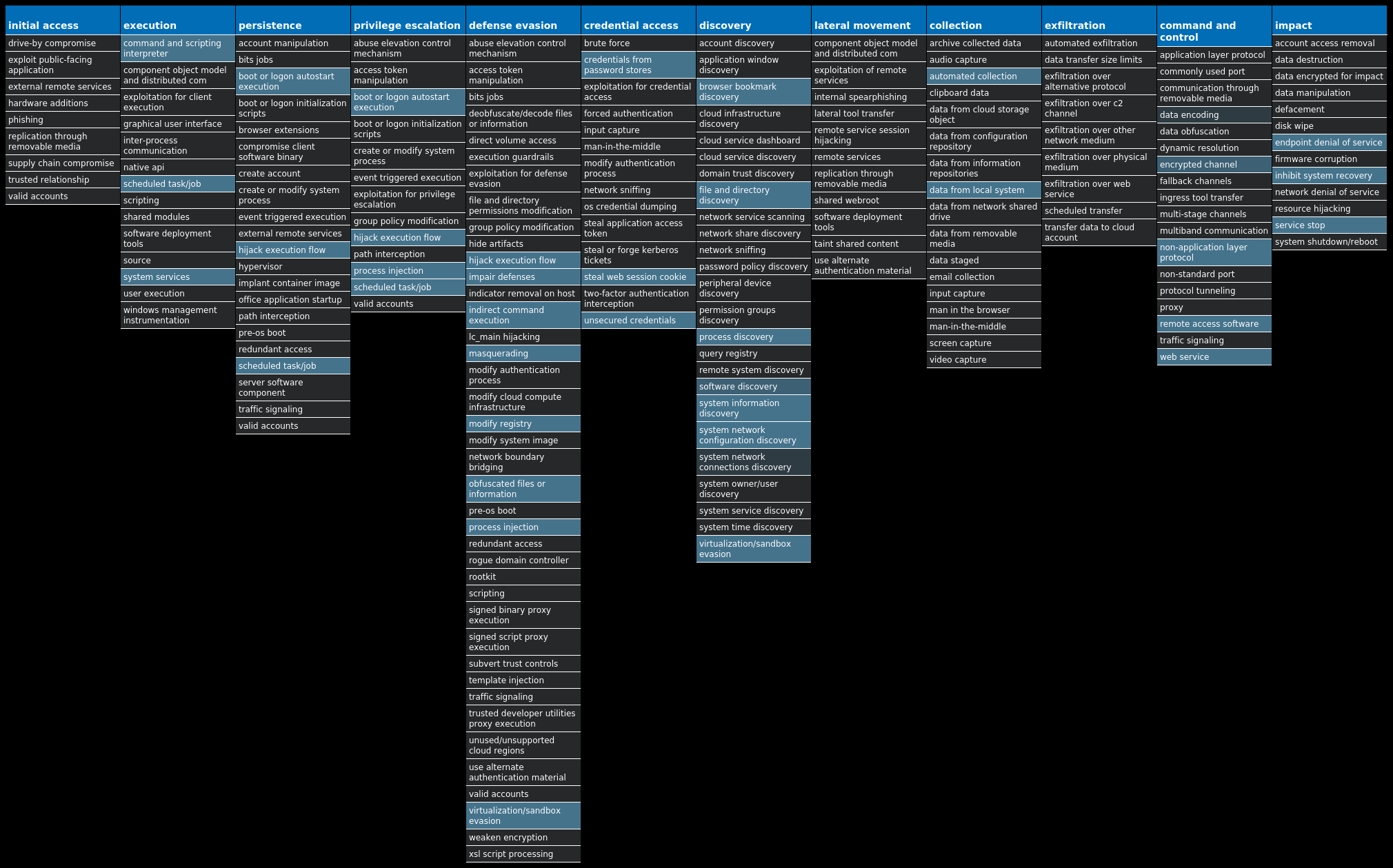
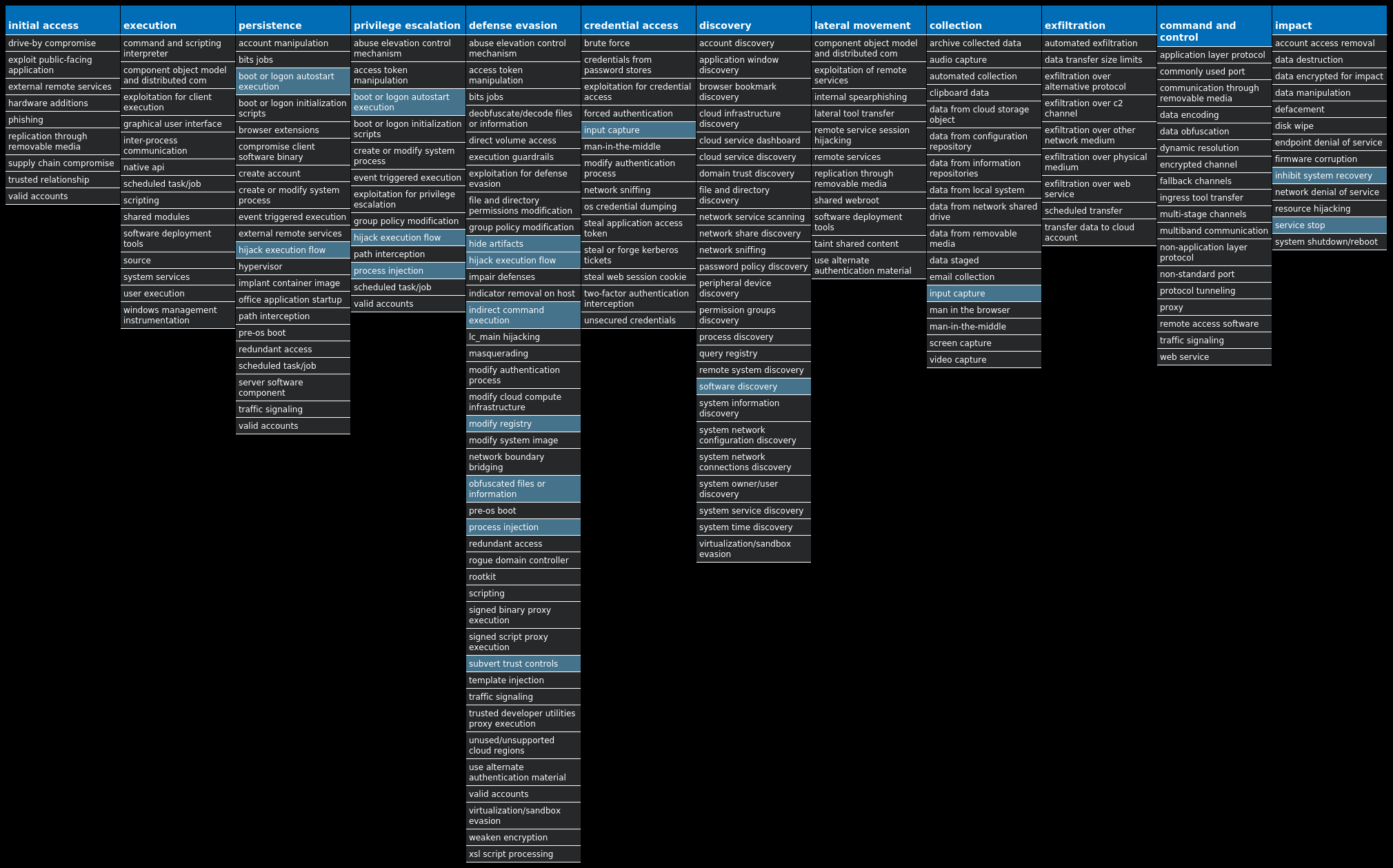
For each threat described below, this blog post only lists 25 of the associated file hashes and up to 25 IOCs for each category. An accompanying JSON file can be found [here]() that includes the complete list of file hashes, as well as all other IOCs from this post. A visual depiction of the MITRE ATT&CK techniques associated with each threat is also shown. In these images, the brightness of the technique indicates how prevalent it is across all threat files where dynamic analysis was conducted. There are five distinct shades that are used, with the darkest indicating that no files exhibited technique behavior and the brightest indicating that technique behavior was observed from 75 percent or more of the files.
The most prevalent threats highlighted in this roundup are:
Threat Name| Type| Description
—|—|—
Win.Downloader.Upatre-10001445-0| Downloader| Upatre is a malicious downloader often used by exploit kits and phishing campaigns. Upatre downloads and executes malicious executables, such as banking malware.
Win.Dropper.Kuluoz-10001444-0| Dropper| Kuluoz, sometimes known as “Asprox,” is a modular remote access trojan that is also known to download and execute follow-on malware, such as fake antivirus software. Kuluoz is often delivered via spam emails pretending to be shipment delivery notifications or flight booking confirmations.
Win.Packed.Razy-10001440-0| Packed| Razy is oftentimes a generic detection name for a Windows trojan. It collects sensitive information from the infected host and encrypt the data, and send it to a command and control (C2) server. Information collected might include screenshots. The samples modify auto-execute functionality by setting and creating a value in the registry for persistence.
Doc.Dropper.Valyria-10001412-0| Dropper| Valyria is a malicious Microsoft Word document family that is used to distribute other malware, such as Emotet.
Win.Dropper.Glupteba-10001476-0| Dropper| Glupteba is a multi-purpose trojan that is known to use the infected machine to mine cryptocurrency and steals sensitive information like usernames and passwords, spreads over the network using exploits like EternalBlue, and leverages a rootkit component to remain hidden. Glupteba has also been observed using the Bitcoin blockchain to store configuration information.
Win.Dropper.PlasmaRAT-10000760-0| Dropper| PlasmaRAT is a RAT that has many capabilities including mining, denial of service, remote desktop access, and keylogging. PlasmaRAT’s sourcecode is freely available online and has been seen used by threat actors such as APT33.
* * *
## Threat Breakdown
### Win.Downloader.Upatre-10001445-0
#### Indicators of Compromise
* IOCs collected from dynamic analysis of 29 samples
Registry Keys| Occurrences
—|—
`LOCAL SETTINGSMUICACHE8252C64B7E
Value Name: LanguageList`| 29
IP Addresses contacted by malware. Does not indicate maliciousness| Occurrences
—|—
`51[.]222[.]30[.]164`| 29
Domain Names contacted by malware. Does not indicate maliciousness| Occurrences
—|—
`groupesorepco[.]com`| 29
`bulkbacklinks[.]com`| 29
Files and or directories created| Occurrences
—|—
`%TEMP%hummy.exe`| 29
#### File Hashes
`0323edc8d532da1aefe5766303a1e4aebeaab1659add9a74a07139bac4d49e21`
`061783c38fa569ec6943032cd3e89adf46b85058ffce04568bc73de9afb837e4`
`0a762357e7fd4205bffb69d21b994d1d7904f2e3036df78a68f001ea275874b9`
`0cac5a7b8060ca7d072ef200ebe114e79db226c0c77b23a5bfdad6367ea66286`
`0fe6a1a25bc5f8e635ec6858e70a858d8ada70e4c756ce7ead552f9356f1bac1`
`10a891e850d4aa2cd19cd91667e4aa71a3f5c695c5768eaca0de9b7447af40fe`
`119b4aada3e4c30184918106a31fdf69f9761311feaf60911835e36ec45be4d8`
`138cff7ae6280470a0c46263b1c66ff095534dd2fdd55c205790601b35344de3`
`28f6b3ddad4f5eac964b447a327c65da4ebc78aab3a77ab771b4cec0a831e3d4`
`2d92e70ea5454c62b44dd8e103937a7247d8bdc568f781c4b34a6bcc98a05e6d`
`30812a0a04339fb52e41985b348535455af8d3b6b7f0323f26879d61a1eff7fb`
`34bda506acb7ec2bcf103e8ba957b62bd801bb0a7c51d15953088a5ff0e25934`
`35cae9bfee37620eed0623fd3c451b6420bac82066b97392ba4dc1e012e3a2b9`
`36444340684422c57a04de89af9d8ce31014ade3aff049f2f909537efe7f65a5`
`37b5372bfd492c9541d1ddfcb4fd18aa73d4e2afe10c4c94a61b62b59cb41bbc`
`3b14a24946a12d98d5ed001ff5ae0a1a4503e1a142a0aa013e4bdf164fe215ac`
`4537b602ee160ee2e1e6881c43fc89b4805d67e50cd052aa602beb022e85217d`
`48db71773aa5c9f3adad407f2fb053be71a589ddde373cd4d34a0dddbe8a568a`
`4f73987d7bc3fba50f4b5bfc1d5c04e066b2a61297872c1fe3f5241ae8b867bb`
`537ece66bbcc609d5878b3f39a0c5b9dbbe654fe8844991462ea06f00670be88`
`5a5deb3033c8335e05ea29369a24adf6292254ca61a13bfbb4dbf5dcd33aa97d`
`5d69cea5ff1f6d0c9543f94f4a08d474822bbd462f3bd946b87482fb50635648`
`5e0ff03ec2782cdc0d47d71fd5921b585578a6727c6f5d8672a66eaaa1749f7c`
`5eb916933bdc0557ab1f18f0779085afce4c9099525e719447b530b72cd17389`
`6064e1b64a1cdad71b8b2ba1b8f6ee644ee9305d8baf9735a63c5af65233a579`
*See JSON for more IOCs
#### Coverage
Product| Protection
—|—
Secure Endpoint| 
Cloudlock| N/A
CWS| 
Email Security| 
Network Security| 
Stealthwatch| N/A
Stealthwatch Cloud| N/A
Secure Malware Analytics| 
Umbrella| 
WSA| 
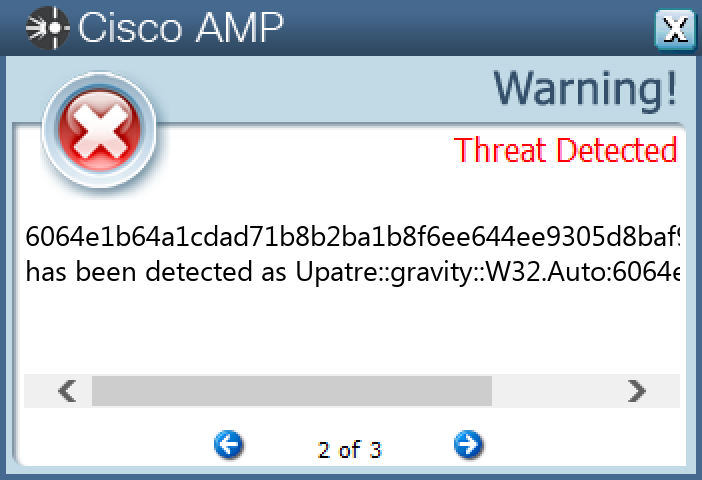
#### Screenshots of Detection
#### Secure Endpoint
#### Secure Malware Analytics
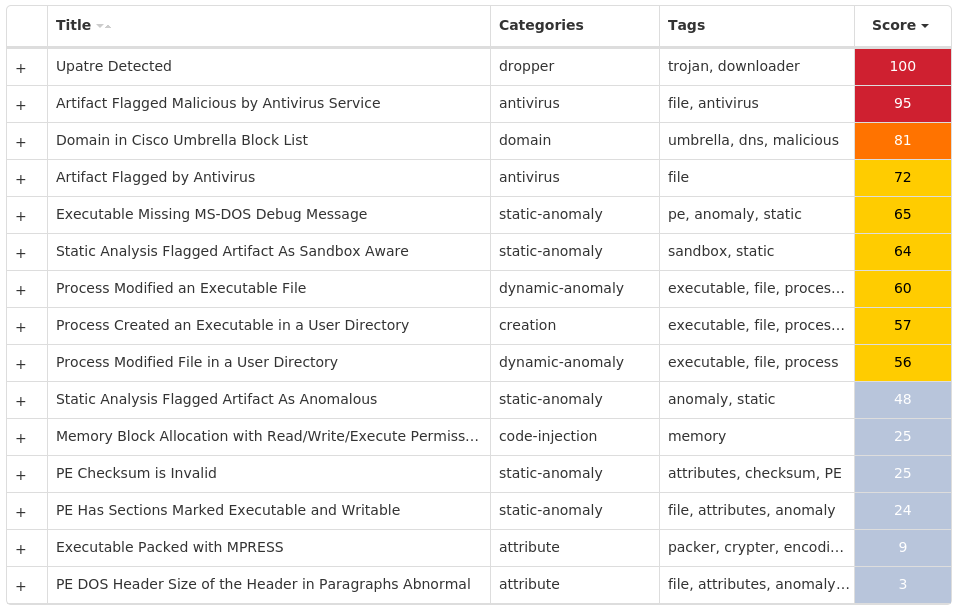
#### MITRE ATT&CK
* * *
### Win.Dropper.Kuluoz-10001444-0
#### Indicators of Compromise
* IOCs collected from dynamic analysis of 32 samples
Registry Keys| Occurrences
—|—
`SOFTWARE`| 23
`SOFTWAREOLFPSCDU
Value Name: gebgrgcs`| 2
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: upeqcbfi`| 2
`SOFTWAREPNHARWEN
Value Name: tkpkvuuv`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: ipujklsd`| 1
`SOFTWAREAIPUCTSM
Value Name: uepvvthp`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: eohpdgar`| 1
`SOFTWARESIJOHJOQ
Value Name: qbolerqh`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: jhqqjnsh`| 1
`SOFTWAREUORQTLIO
Value Name: rhwxoftw`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: dgtkjdtr`| 1
`SOFTWAREMUTKAJBX
Value Name: tdhgnwmq`| 1
`SOFTWAREGCNUFLFR
Value Name: tfrsnxbc`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: kkmcetlr`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: kmenlemq`| 1
`SOFTWAREBLCQSVUT
Value Name: kqkqgnfk`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: mpdsbbhd`| 1
`SOFTWAREECRARMIC
Value Name: uqlbdvjl`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: dpmdtfdd`| 1
`SOFTWAREKPQLPHTV
Value Name: nqikbbnq`| 1
`SOFTWARERJPOTMOR
Value Name: cdjoknmb`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: ebgndtjf`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: jqhgvjhd`| 1
`SOFTWAREIWIJWRJQ
Value Name: nfurxpab`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: vcdhnulu`| 1
Mutexes| Occurrences
—|—
`aaAdministrator`| 23
`abAdministrator`| 23
`Global`| 9
IP Addresses contacted by malware. Does not indicate maliciousness| Occurrences
—|—
`110[.]170[.]30[.]195`| 14
`199[.]59[.]57[.]142`| 14
`162[.]13[.]189[.]52`| 12
`193[.]46[.]84[.]84`| 11
`107[.]170[.]221[.]187`| 11
`23[.]227[.]182[.]207`| 10
`173[.]199[.]182[.]152`| 10
`212[.]129[.]21[.]210`| 10
`158[.]255[.]238[.]9`| 10
Files and or directories created| Occurrences
—|—
`%LOCALAPPDATA%.exe`| 23
#### File Hashes
`00342c05f0faeb777c292a4263a60cf34083f0703cd986e4d1afa9db05ed97c7`
`034085f1acc8151203897dfa8e0c20c23cfdc7fb04dff1d8de9276c11a0fa351`
`06a89d09af32a664b18cf9a3dc223e84a854f7259565c5542278a16cab911021`
`0d4aff7efefaa88ec14b02ed12ca3deed7e6b273b6fda82d7066ae4cf9c85242`
`18dba1ba835356d4cb36781959de355aec57d7bf50526c275ae75f5294433efe`
`1a75b0eab3722538649b377d3f4f930d4870deb2ea120ec7ac0fafaba0350032`
`1c0644456cc0aa070ee81eb08163f46a7a74585857e9d818736e163e36fc6d4a`
`1e3952115d2c916f845d10914bcec73daa539e6ed9a1d404122ccb7315cc0d53`
`22b2f7a50c3abd93ff453f1670aa9f135227e971c2baf11e36f8dc69e84d4e56`
`23154e22b273d45812a4b0f7088db886fa498a4669ee226aac8af08be3ff49b3`
`28fddb43138d7231ad6add2d9d70cb50830577f3fc3d5e0488dfa9a16a50b372`
`33b50a69c558582c1caf27021b1733d7b92b38988fcc04078758b7c20ea0b1da`
`3623e5b40872cd973897a401563c885e57f0cf6c4fa9d15efa2057b0e99c9c43`
`388da6758e0411034e5c294709dab82dab9f9985d21326c615eac557087965fe`
`3af803177e7d2463ca755b70baf550de4b7b506df719345e942f558af8f27c69`
`46290e2b7639d68a9e911e8e4be461b189bc741c76d5245ea3d26d8beb0a9536`
`559cc94f2a183c9db488431fc8d166c0e924907e9fc002968efa77ec9aa7679e`
`561668af320f5a6dd2dfa03ee8eade9441ecd9badd88b1a2d3a6846a36eba092`
`568fa2a7d64aa79b2d4f4ee58e3b296a17952de78a860f87a9b91f3098e0e08c`
`5792a7b159c605f75b864d542491be2e6e97aee4c06e3051b0ee3a019b8fc74f`
`5873b9c7431e18d1ab7f0b453240c4cba36ccac6a9628e536eb4d391d8494437`
`62205125608aadcdb458db35d865fede56c98722b717a44a2afe5e5a69831876`
`62fac7e247c1362ccf340119f1baa8e4ff6aece558bba7b6ba2995397bff2b1f`
`6f6d8ae4d2731a6ed1edee55880235c7d102900da1cb986db6c76bc0d157f9dc`
`730fdae49c50d5339f8c19ab80c1fce2ce0a5d4d3a33e49bced57e50ea20126d`
*See JSON for more IOCs
#### Coverage
Product| Protection
—|—
Secure Endpoint| 
Cloudlock| N/A
CWS| 
Email Security| 
Network Security| N/A
Stealthwatch| N/A
Stealthwatch Cloud| N/A
Secure Malware Analytics| 
Umbrella| N/A
WSA| N/A
#### Screenshots of Detection
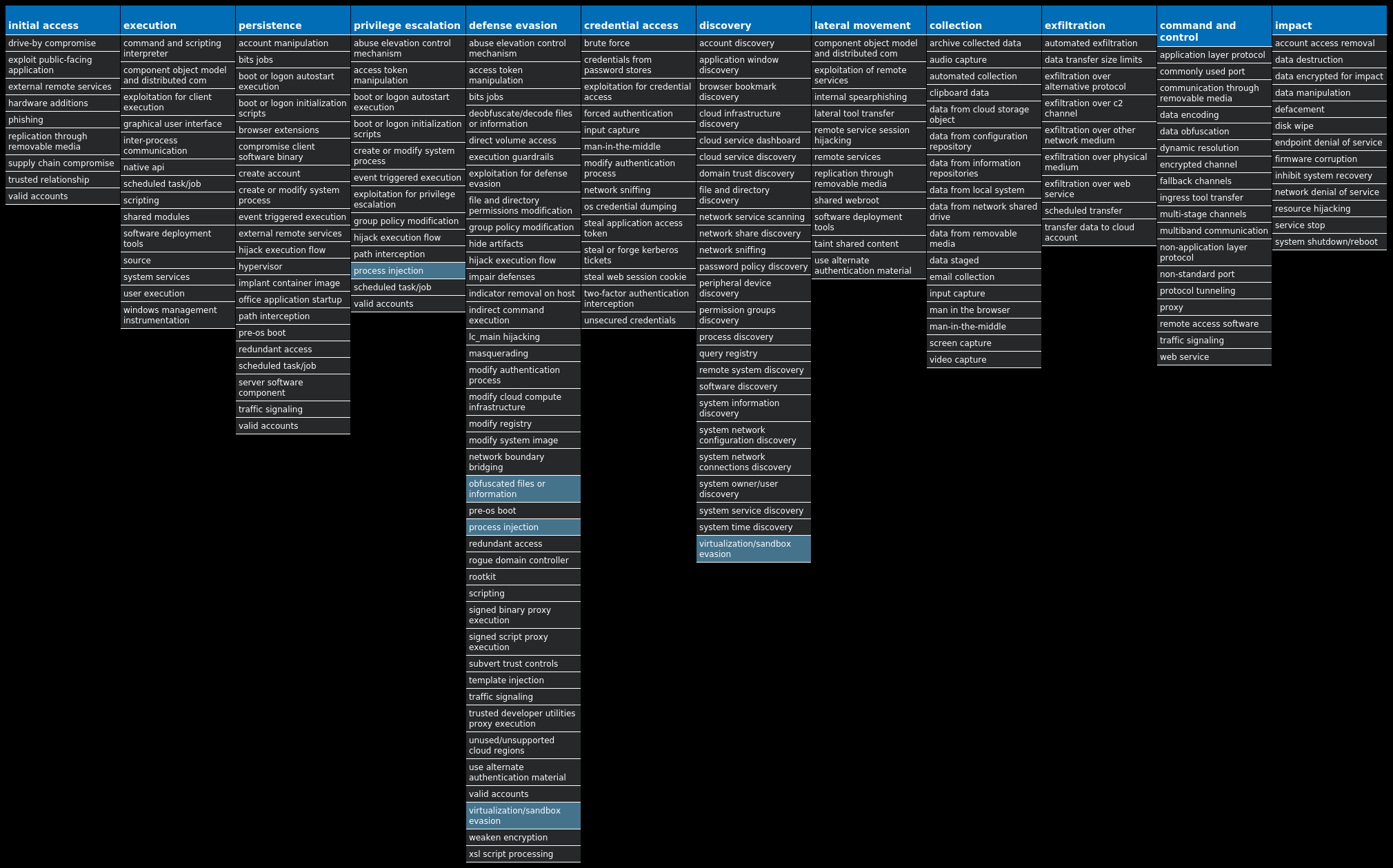
#### Secure Endpoint
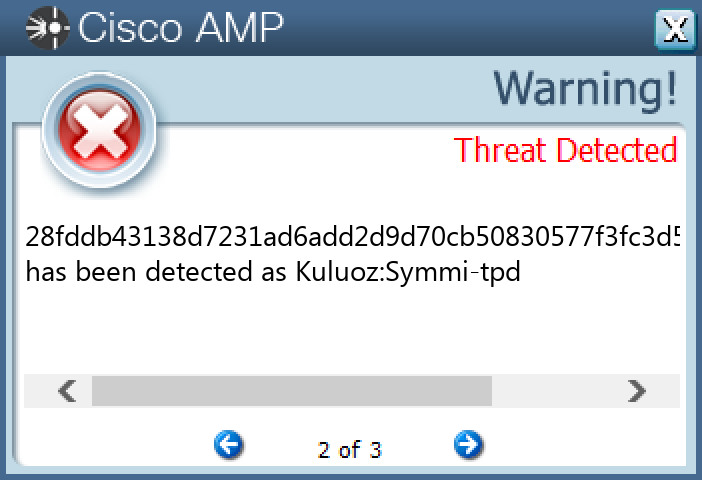
#### Secure Malware Analytics
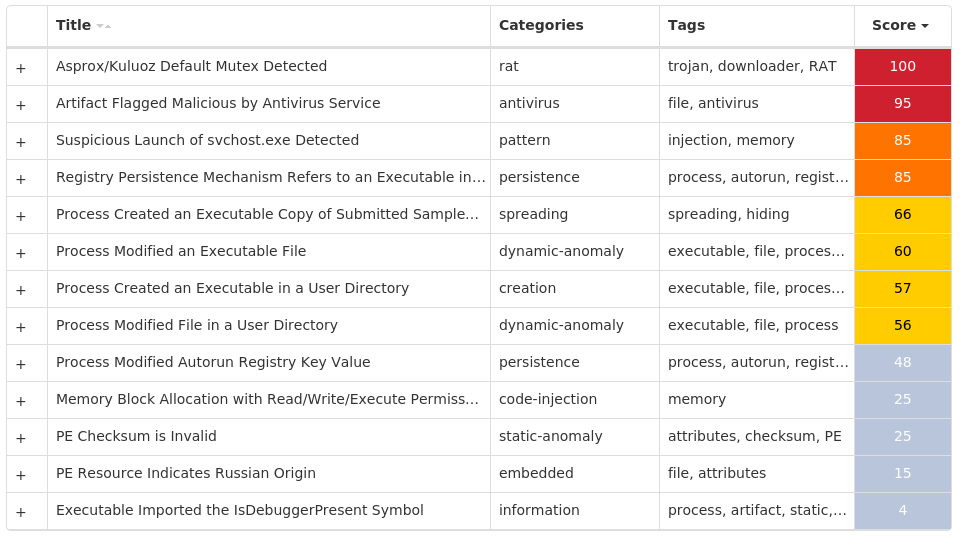
#### MITRE ATT&CK
* * *
### Win.Packed.Razy-10001440-0
#### Indicators of Compromise
* IOCs collected from dynamic analysis of 26 samples
Registry Keys| Occurrences
—|—
`ENVIRONMENT
Value Name: SEE_MASK_NOZONECHECKS`| 7
`S-1-5-21-2580483871-590521980-3826313501-500
Value Name: di`| 5
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: Client`| 2
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONEXPLORERTASKBAND
Value Name: FavoritesVersion`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: 5d5e3c1b562e3a75dc95740a35744ad0`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: d5a38e9b5f206c41f8851bf04a251d26`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: d5a38e9b5f206c41f8851bf04a251d26`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONPOLICIESEXPLORERRUN`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONEXPLORERTASKBAND
Value Name: FavoritesChanges`| 1
`SOFTWARE{WEQ2-67R1-YUU3-EEQ2-TY74}`| 1
`SOFTWARE{WEQ2-67R1-YUU3-EEQ2-TY74}
Value Name: US`| 1
`SOFTWARE9B4E76249AEEC926B2BF5D22AB66FD6A`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: 9b4e76249aeec926b2bf5d22ab66fd6a`| 1
`SOFTWARE9B4E76249AEEC926B2BF5D22AB66FD6A
Value Name: [kl]`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: c0fe9f26ddd18885f6e909b228e16080`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: c0fe9f26ddd18885f6e909b228e16080`| 1
`SOFTWARE85586C1696EEF072F608E599824BECB7`| 1
`SOFTWARE85586C1696EEF072F608E599824BECB7
Value Name: [kl]`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: 5d5e3c1b562e3a75dc95740a35744ad0`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: ff80315b890d700afbcc28650ff0e71b`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: ff80315b890d700afbcc28650ff0e71b`| 1
`SOFTWARE1FF2F8A6E8685E09EE6FCA84830B84DE`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: 1ff2f8a6e8685e09ee6fca84830b84de`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: 1ff2f8a6e8685e09ee6fca84830b84de`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: AhnLab Update`| 1
Mutexes| Occurrences
—|—
“| 7
`RV_MUTEX`| 5
`{WEQ2-67R1-YUU3-EEQ2-TY74}`| 1
`5d5e3c1b562e3a75dc95740a35744ad01234`| 1
IP Addresses contacted by malware. Does not indicate maliciousness| Occurrences
—|—
`172[.]67[.]34[.]170`| 1
Domain Names contacted by malware. Does not indicate maliciousness| Occurrences
—|—
`expres123123[.]zapto[.]org`| 2
`kitty1983[.]ddns[.]net`| 2
`pastebin[.]com`| 1
`dz1993[.]ddns[.]net`| 1
`davidaf[.]ddns[.]net`| 1
`toune16[.]ddns[.]net`| 1
`honma123[.]codns[.]com`| 1
`jeffly12[.]hopto[.]org`| 1
`alwerfalli[.]ddns[.]net`| 1
`cyw0923[.]codns[.]com`| 1
`raeed99[.]ddns[.]net`| 1
`at-44[.]myq-see[.]com`| 1
`rootjuba1[.]ddns[.]net`| 1
Files and or directories created| Occurrences
—|—
`%TEMP%.exe`| 6
`$Recycle.Bin.exe`| 4
`%ProgramData%RevengeRAT`| 4
`%TEMP%RES.tmp`| 4
`%TEMP%.tmp`| 4
`%TEMP%.out`| 4
`%TEMP%.cmdline`| 4
`Documents and Settings.exe`| 3
`MSOCache.exe`| 3
`PerfLogs.exe`| 3
`%ProgramFiles%.exe`| 3
`$Recycle.Bin`| 3
`%ProgramFiles%`| 3
`Documents and Settings`| 3
`PerfLogs`| 3
`MSOCache`| 3
`%APPDATA%Client.exe`| 3
`E:RevengeRAT`| 3
`RevengeRAT`| 3
`RevengeRATClient.exe`| 2
`Recovery.exe`| 2
`RevengeRATUSBPower.exe`| 2
`%TEMP%melt.txt`| 1
`%APPDATA%Microsoftsvchost.exe`| 1
`%APPDATA%MicrosoftWindowsStart MenuProgramsStartupClient.exe`| 1
*See JSON for more IOCs
#### File Hashes
`05a1d8381fd31606265a05d9f4c158c69f574e417201969e67663e73f6f35321`
`0603e5cb577f35a2a5f144724434cdc41862673109967eb9927dc010465b92ee`
`08a5c4cfb2b4cc1ee2a780c7c1309281709817fec2b6cf42a6392e648c83b840`
`09a7facf4e659f04f37d6e00c32e6d670365fb00521c8d35e7ddf4cbca1aae1e`
`0e05d6bbb0b482806dee87457dbdcbc934cea343999829a3c7827e8e635d3c33`
`1fecf366798b47c1b2bf57416201be85561ee853ebd4e604bc9f9abaea36b1ff`
`2317b833127e989c808f8092e7b277734e9ebbccacecae7f185e6c62adeeb4b9`
`2d2bc5b6226d288b9abec0cf2443fd239df63c2eb1bebca28ae2e7cbfe03cb48`
`35b7995b52e41c6a5eabbc6cb7a5f962586466ca4ceb2372ea608daccaead43f`
`3a9a2051c0e02a724d3c33042fb683a68032ec397a6fcb29f7eef4e50d5178db`
`42cb8ee5ee0724540cc2aa48bafa2e205f2449e5101c90f2a07f3d207a115644`
`47c82197b05cd8e01804bc0c934754923e84de7a9485b53c885f662f2fab67dd`
`532199cfe386343914f1f4be093ae6a5eb0755779c967e797443240891c71146`
`5fbaec0c6a28a21433747c6b4e2d3f8d2b484bf5bc02e664682906c95b528ad7`
`62780b161d3ba2c2839caac945bac274f62d8f564a64d620f3cdc8a925e69ddd`
`6947b2474bc0e3305af7c6f64f418d4a8d9395cc25f9843532d939c538093b82`
`7260c6c20676bf6d9a15d58987b528ce716dc51180545966f7c586db15022ea3`
`7b930e43c39e416c81ec3acf2f22964e85d51c5c9c9a1ab95e5ee21f12382044`
`7ec938b09a5d5c0f6dbc1a0ca75cf669568d5df15118cfea89e9db0cc0eb1826`
`8c8b3a3e5a85939f3af1359083876303c483ad2a98d287f1c13187b794006bff`
`95eef31a2af620c79e74f4b6743eb8176e5e50187ab26cd21e6b24e5a5b63357`
`961b88ffa399625ff3cfe6e4161b8dc6b3fd5071ecdaab86889cd42e3ebb6114`
`9ff847764a3a4a2e4f3fba78b87fc6e8a722c3fee5093e9104292db204853314`
`a57667097aa63516b88121a6e5249f7c953003916ced9341406b916b02e07d92`
`a6d757c407570fc1b57ab1e18e77c48ae88ebc965a1a75a610b97f9167f81d4d`
*See JSON for more IOCs
#### Coverage
Product| Protection
—|—
Secure Endpoint| 
Cloudlock| N/A
CWS| 
Email Security| 
Network Security| 
Stealthwatch| N/A
Stealthwatch Cloud| N/A
Secure Malware Analytics| 
Umbrella| N/A
WSA| N/A
#### Screenshots of Detection
#### Secure Endpoint
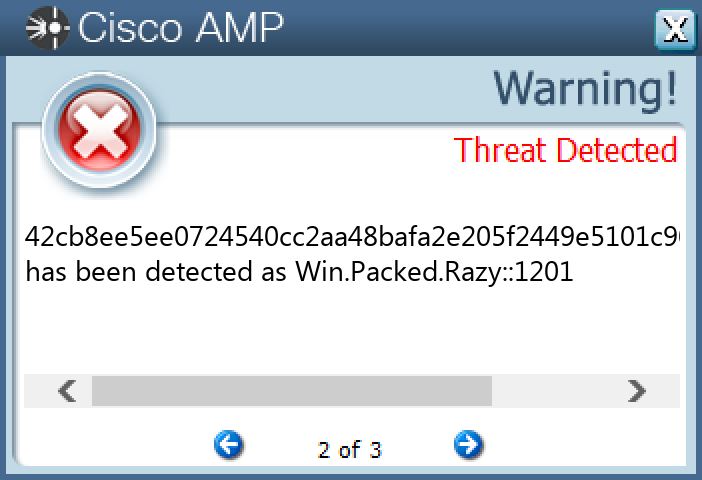
#### Secure Malware Analytics
#### MITRE ATT&CK
* * *
### Doc.Dropper.Valyria-10001412-0
#### Indicators of Compromise
* IOCs collected from dynamic analysis of 14 samples
Mutexes| Occurrences
—|—
`Local10MU_ACB10_S-1-5-5-0-67863`| 14
`Local10MU_ACBPIDS_S-1-5-5-0-67863`| 14
`LocalWinSpl64To32Mutex_10960_0_3000`| 14
`LocalMU_IMDS10_S-1-5-5-0-67863`| 14
IP Addresses contacted by malware. Does not indicate maliciousness| Occurrences
—|—
`104[.]237[.]62[.]211`| 4
`64[.]185[.]227[.]155`| 4
`173[.]231[.]16[.]77`| 4
Domain Names contacted by malware. Does not indicate maliciousness| Occurrences
—|—
`api[.]ipify[.]org`| 12
`templogio[.]com`| 6
`johommeract[.]ru`| 5
`amesibiquand[.]ru`| 3
Files and or directories created| Occurrences
—|—
`%TEMP%if.bin`| 14
`%TEMP%if.bin:Zone.Identifier`| 14
`%TEMP%zoro.kl`| 14
`%TEMP%zoro.kl:Zone.Identifier`| 14
`%APPDATA%MicrosoftTemplates~WRD0000.tmp:Zone.Identifier:$DATA`| 14
`%APPDATA%microsofttemplates~$zoro.doc`| 14
`%APPDATA%microsofttemplates~WRD0000.tmp`| 14
#### File Hashes
`04ece234e8e543a378b27b440c3bfd4b8b5dffdc65f8b5048d625cda9fd6aa25`
`1330a9b1b83a5956ebb74c44a84673a35c1e84a078911e6de6b9a85f8fd80823`
`1c9d20896f1c44c2dbbb6bb05979c1ec374d097b9af4d881c0c1949ddc1d821f`
`59a9d01ae23d1b0632f44d5720265c27a14d24c92d413edf39153d998e6269ec`
`5adb541c551814e964482b45644033ea1c4ad4830d0384047a6906bbb86ac243`
`5f4e57986604f7caf6831a25d3b53542d2665dedc0fedb8fc59dd72a914b0963`
`87ac85417295fde5f181265ebfa8028df41abfa17c7d8f5ab4794dab37af8575`
`8d0486539dacdf2201a32ac6090ec628139185c19099a010a3027bf6b6611fcd`
`a2903ebc67c3549f59ecf6718444f6826030fa29f3701460b9709edbd9aa675b`
`ae4b72f4a31cfee6f08af42333d5bfb1a2500249e8446a2e9fe4fa7e55ec0821`
`b062dd8f8c46cb010cf562145e9a2836f5625f41af329e87ca2bbdc2fd05435d`
`bcdcf1ec9bf276c3e6ea441e64ff91fe836857fc49c0c97b672adc0a64aa6873`
`c1c2fd46ce19afa66360c6db20edba84c460b254dc4676949bf38bdd41cdd577`
`cf4adca8773145cf0a1d4ba32d555643442e14e9181ae8450bfb79ab86144914`
#### Coverage
Product| Protection
—|—
Secure Endpoint| 
Cloudlock| N/A
CWS| 
Email Security| 
Network Security| N/A
Stealthwatch| N/A
Stealthwatch Cloud| N/A
Secure Malware Analytics| 
Umbrella| 
WSA| 
#### Screenshots of Detection
#### Secure Endpoint
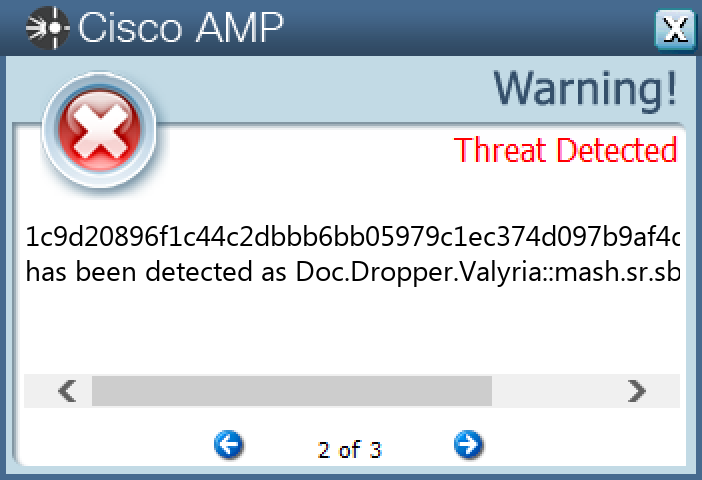
#### Secure Malware Analytics
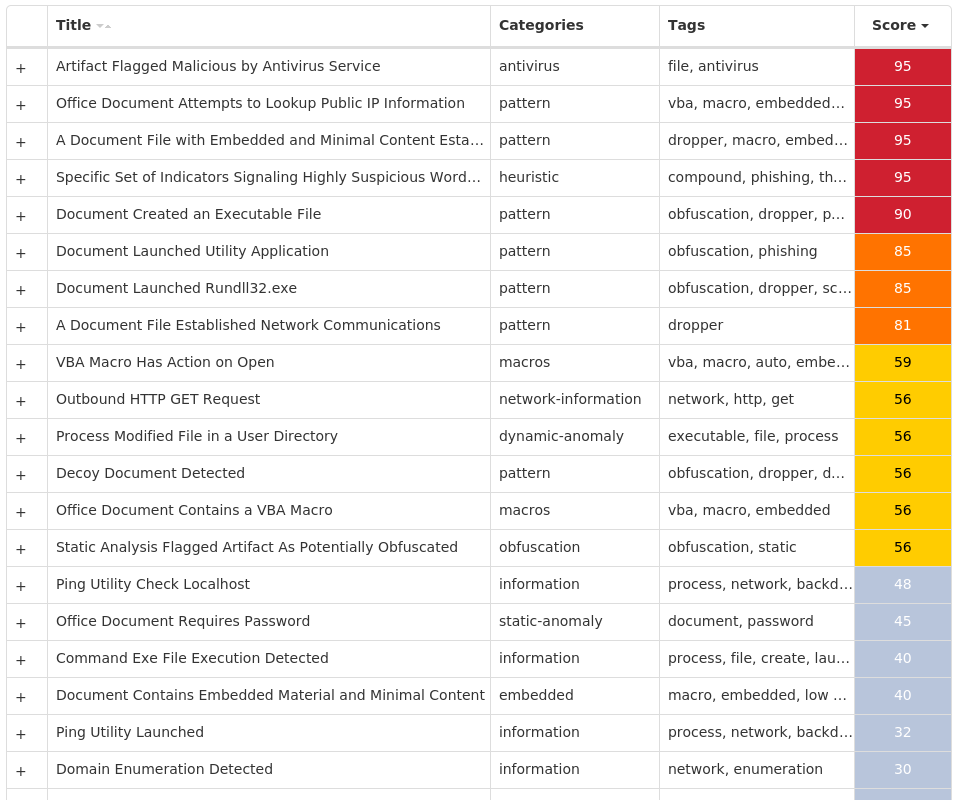
#### MITRE ATT&CK
* * *
### Win.Dropper.Glupteba-10001476-0
#### Indicators of Compromise
* IOCs collected from dynamic analysis of 24 samples
Registry Keys| Occurrences
—|—
`SOFTWAREMICROSOFTA1890984
Value Name: PatchTime`| 24
`SOFTWAREMICROSOFTA1890984
Value Name: PGDSE`| 24
`SYSTEMCONTROLSET001SERVICESVBOXSF
Value Name: WOW64`| 24
`SYSTEMCONTROLSET001SERVICESVBOXSF
Value Name: ObjectName`| 24
`SYSTEMCONTROLSET001SERVICESVBOXMOUSE
Value Name: Type`| 24
`SYSTEMCONTROLSET001SERVICESVBOXMOUSE
Value Name: Start`| 24
`SYSTEMCONTROLSET001SERVICESVBOXMOUSE
Value Name: ErrorControl`| 24
`SYSTEMCONTROLSET001SERVICESVBOXMOUSE
Value Name: ImagePath`| 24
`SYSTEMCONTROLSET001SERVICESVBOXMOUSE
Value Name: DisplayName`| 24
`SYSTEMCONTROLSET001SERVICESVBOXMOUSE
Value Name: WOW64`| 24
`SYSTEMCONTROLSET001SERVICESVBOXMOUSE
Value Name: ObjectName`| 24
`SYSTEMCONTROLSET001SERVICESVBOXGUEST
Value Name: Type`| 24
`SYSTEMCONTROLSET001SERVICESVBOXGUEST
Value Name: Start`| 24
`SYSTEMCONTROLSET001SERVICESVBOXGUEST
Value Name: ErrorControl`| 24
`SYSTEMCONTROLSET001SERVICESVBOXGUEST
Value Name: ImagePath`| 24
`SYSTEMCONTROLSET001SERVICESVBOXGUEST
Value Name: DisplayName`| 24
`SYSTEMCONTROLSET001SERVICESVBOXGUEST
Value Name: WOW64`| 24
`SYSTEMCONTROLSET001SERVICESVBOXGUEST
Value Name: ObjectName`| 24
`SYSTEMCONTROLSET001SERVICESVBOXSERVICE
Value Name: Type`| 24
`SYSTEMCONTROLSET001SERVICESVBOXSERVICE
Value Name: Start`| 24
`SYSTEMCONTROLSET001SERVICESVBOXSERVICE
Value Name: ErrorControl`| 24
`SYSTEMCONTROLSET001SERVICESVBOXSERVICE
Value Name: ImagePath`| 24
`SYSTEMCONTROLSET001SERVICESVBOXSERVICE
Value Name: DisplayName`| 24
`SYSTEMCONTROLSET001SERVICESVBOXSERVICE
Value Name: WOW64`| 24
`SYSTEMCONTROLSET001SERVICESVBOXSERVICE
Value Name: ObjectName`| 24
Mutexes| Occurrences
—|—
`GlobalSetupLog`| 24
`GlobalWdsSetupLogInit`| 24
`Globalh48yorbq6rm87zot`| 24
`WininetConnectionMutex`| 24
`Globalqtxp9g8w`| 24
`GlobalxmrigMUTEX31337`| 6
IP Addresses contacted by malware. Does not indicate maliciousness| Occurrences
—|—
`204[.]79[.]197[.]219`| 24
`20[.]60[.]148[.]196`| 24
`20[.]209[.]34[.]36`| 24
`185[.]82[.]216[.]48/31`| 12
`172[.]67[.]168[.]112`| 9
`104[.]21[.]54[.]103`| 8
`162[.]159[.]135[.]233`| 7
`162[.]159[.]133[.]233`| 6
`162[.]159[.]130[.]233`| 5
`81[.]3[.]27[.]44`| 5
`185[.]82[.]216[.]64`| 5
`162[.]159[.]129[.]233`| 4
`172[.]253[.]120[.]127`| 4
`142[.]250[.]111[.]127`| 4
`142[.]250[.]15[.]127`| 3
`74[.]125[.]128[.]127`| 3
`108[.]177[.]102[.]127`| 3
`51[.]159[.]136[.]111`| 3
`188[.]138[.]33[.]149`| 2
`193[.]0[.]213[.]42`| 2
`94[.]100[.]6[.]27`| 2
`162[.]159[.]134[.]233`| 2
`192[.]99[.]43[.]171`| 2
`162[.]55[.]91[.]19`| 2
`157[.]90[.]183[.]103`| 2
*See JSON for more IOCs
Domain Names contacted by malware. Does not indicate maliciousness| Occurrences
—|—
`msdl[.]microsoft[.]com`| 24
`vsblobprodscussu5shard35[.]blob[.]core[.]windows[.]net`| 24
`vsblobprodscussu5shard60[.]blob[.]core[.]windows[.]net`| 24
`cdn[.]discordapp[.]com`| 24
`twopixis[.]com`| 17
`stun[.]ipfire[.]org`| 5
`e93c35a1-5b7c-447e-bcec-65b84e83dd99[.]uuid[.]mastiakele[.]icu`| 5
`stun[.]l[.]google[.]com`| 4
`stun3[.]l[.]google[.]com`| 4
`e93c35a1-5b7c-447e-bcec-65b84e83dd99[.]uuid[.]zaoshanghaoz[.]net`| 4
`stun[.]stunprotocol[.]org`| 3
`stun1[.]l[.]google[.]com`| 3
`stun2[.]l[.]google[.]com`| 3
`stun4[.]l[.]google[.]com`| 3
`e93c35a1-5b7c-447e-bcec-65b84e83dd99[.]uuid[.]mastiakele[.]xyz`| 3
`stun[.]sipgate[.]net`| 2
`server2[.]mastiakele[.]xyz`| 2
`server13[.]mastiakele[.]icu`| 2
`e93c35a1-5b7c-447e-bcec-65b84e83dd99[.]uuid[.]cdneurops[.]shop`| 2
`e93c35a1-5b7c-447e-bcec-65b84e83dd99[.]uuid[.]zaoshanghao[.]su`| 2
`server4[.]cdneurops[.]pics`| 1
`server15[.]zaoshanghaoz[.]net`| 1
`server13[.]xn--j1ahhq[.]xn--p1ai`| 1
`server14[.]zaoshanghaoz[.]net`| 1
`server2[.]zaoshang[.]moscow`| 1
*See JSON for more IOCs
Files and or directories created| Occurrences
—|—
`%SystemRoot%rsscsrss.exe`| 24
`%TEMP%csrssdsefix.exe`| 24
`%TEMP%csrsspatch.exe`| 24
`%System32%driversWinmon.sys`| 24
`%System32%driversWinmonFS.sys`| 24
`%System32%driversWinmonProcessMonitor.sys`| 24
`%TEMP%Symbols`| 24
`%TEMP%Symbolsntkrnlmp.pdb`| 24
`%TEMP%Symbolsntkrnlmp.pdb9E22A5947A15489895CE716436B45BE02`| 24
`%TEMP%Symbolsntkrnlmp.pdb9E22A5947A15489895CE716436B45BE02download.error`| 24
`%TEMP%Symbolspingme.txt`| 24
`%TEMP%Symbolswinload_prod.pdb`| 24
`%TEMP%Symbolswinload_prod.pdbB7B16B17E078406E806A050C8BEE2E361`| 24
`%TEMP%Symbolswinload_prod.pdbB7B16B17E078406E806A050C8BEE2E361download.error`| 24
`%TEMP%dbghelp.dll`| 24
`%TEMP%ntkrnlmp.exe`| 24
`%TEMP%osloader.exe`| 24
`%TEMP%symsrv.dll`| 24
`%TEMP%csrssDBG0.tmp`| 24
`%System32%Taskscsrss`| 24
`%TEMP%csrssinjector`| 24
`%TEMP%csrssinjectorNtQuerySystemInformationHook.dll`| 24
`%TEMP%csrssinjectorinjector.exe`| 24
`%TEMP%csrsstorTorcached-certs.tmp`| 24
`%TEMP%csrsstorTorcached-microdesc-consensus.tmp`| 24
*See JSON for more IOCs
#### File Hashes
`071b33b943aac7e83b9534293b6f1972222a5afdcb999592f9e790b5ba57f521`
`08003c380d1819ccc5e873f60951d79372ffd2b3796251e988dafae9c70427a3`
`2437108d3504ad5ceeb7d274cad347762bf30bb5c17c4a8fa1f4222819443d1c`
`28876d2e47d69866f632c84b6b636d778a2e7b1713953400743d166bf139b570`
`56d685cb54f89d8d9db25793565e9381d290836d202fe0bff795c1671592306b`
`5bac4d0210a77cd7d329b5a3755ffff5bc99eb64c2dcd9c7d07768fc06a22bf0`
`5f63d5bb5153ce469c558a3ab7d4400364538dcb9a9778373beb8a4cfa479dd5`
`74f2ebd1054d1da087fbbfa3e9bf179b596b7b6054a12a55266e06deea5f2d44`
`786d44033834713cfccdc5b64ea4b0d6994cee31c39656a517eba77379cb80ea`
`81b636167f8d4b1b3f53b7de2cc2ba3452dd292cfe2848934e31aca62a389d25`
`8506dce2e894bf764b5f3a3f1e31a5417cec38b9d341ad95f3fba31c76774195`
`9087940ad07100e45ed7bb0cbc65d4f95ce396302a73c2464b39b9781e937ce0`
`a7b70a33159339131b1988befefefc61b43234769fa3016e54bc88dc6c4597bc`
`b95d39e3a37f70aa9f4a755f919ae58692b575811d4a66859dc15f49d6f39cc5`
`c2905fa662b31dc9409849b05a79a183330102a0de333db6b22c7e581bc385f6`
`c9fda7212f9772ec3f2a48d4221de27d7aed46c8f2feaf31c526212027cb2b0f`
`cd0220e3d48cd61ed5c802f3808c860b2d6e518ef0114c9a32ea9418cb6e0aec`
`cf33241ede6bb57890ad95293b9b04e183156d1d1bd44f6409007a74b461c25e`
`dcb3ff440482062b597f384763466e432e7548753419dbd9099f2b2c87894899`
`dcfffa036aa6b63672055b26d5c318ebeae94ec1870cf33b8928a7e5f72da649`
`eed1582389bfbba92eaf222a033f525f073362c6bb68b3973ad5ddfc31c3b4d4`
`f11f94d98dbd6b48af597e3d6461dfb2d9cd1e4bc565f9e726a7350e2244ba83`
`f427bca7295f908f9c03656decabaa0c0e383a3e0adfca81b800ed2fb1265532`
`fd726415da878f03c5faa72b3527b0d519b59adc86ff32a5c0685bde75fe55e5`
#### Coverage
Product| Protection
—|—
Secure Endpoint| 
Cloudlock| N/A
CWS| 
Email Security| 
Network Security| 
Stealthwatch| N/A
Stealthwatch Cloud| N/A
Secure Malware Analytics| 
Umbrella| 
WSA| 
#### Screenshots of Detection
#### Secure Endpoint
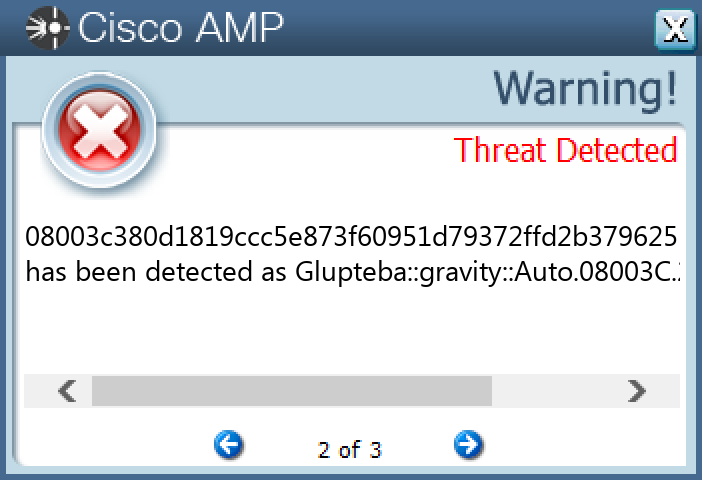
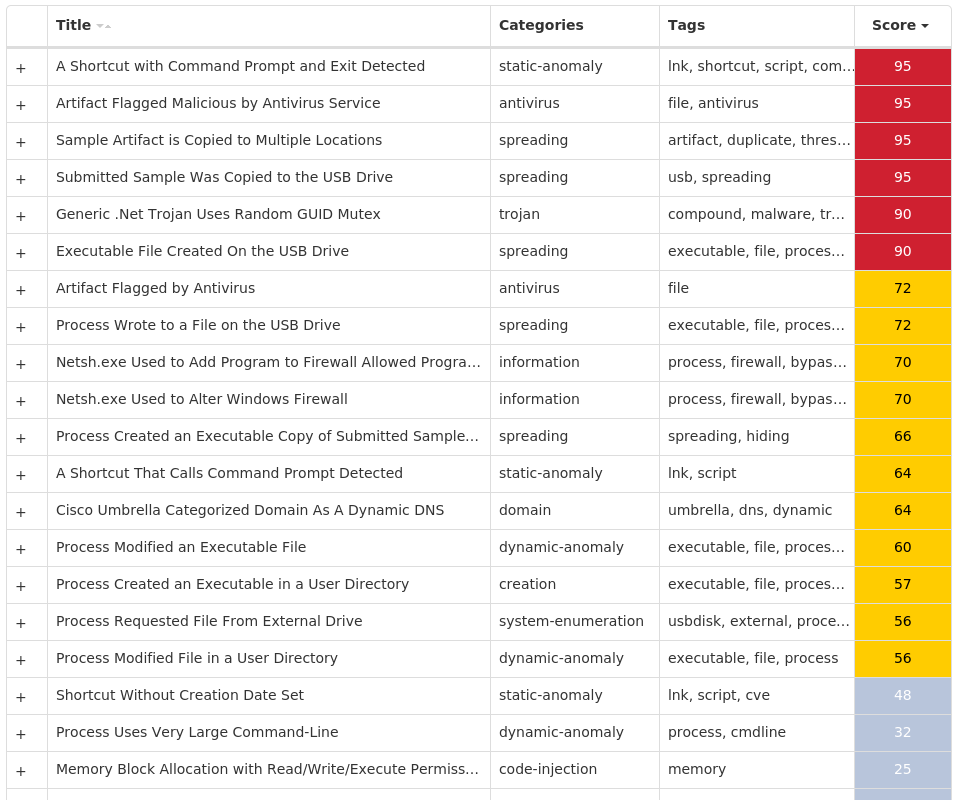
#### Secure Malware Analytics
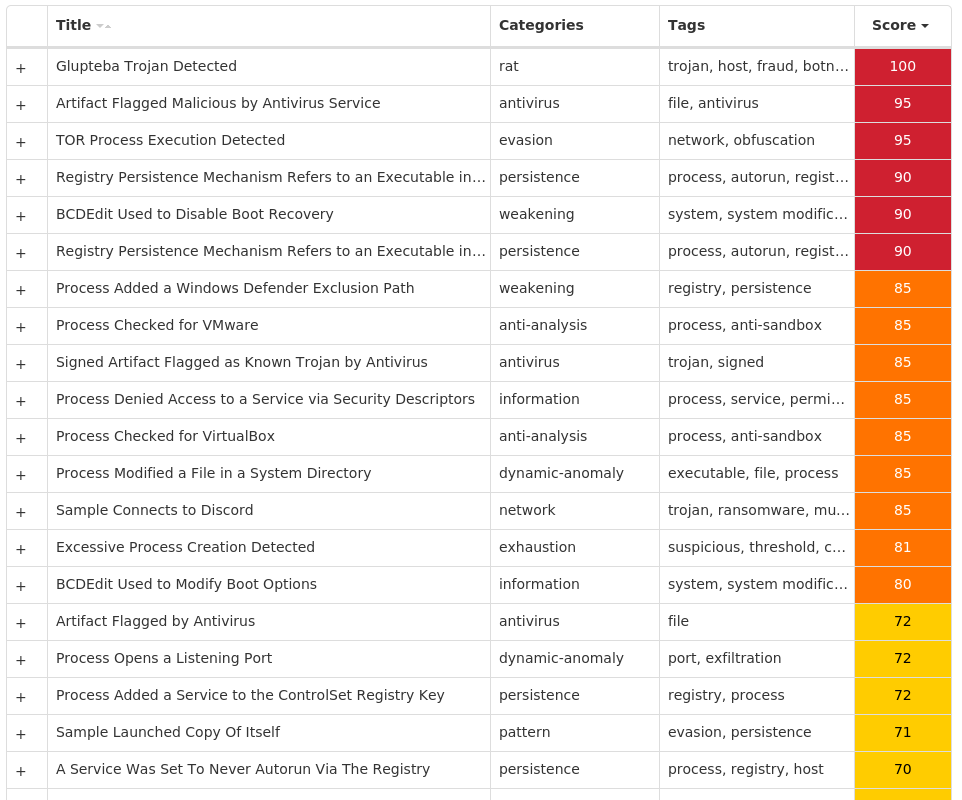
#### MITRE ATT&CK
* * *
### Win.Dropper.PlasmaRAT-10000760-0
#### Indicators of Compromise
* IOCs collected from dynamic analysis of 15 samples
Registry Keys| Occurrences
—|—
`SOFTWAREWOW6432NODEMICROSOFTWINDOWS NTCURRENTVERSIONSYSTEMRESTORE
Value Name: DisableSR`| 15
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONEXPLORERADVANCED
Value Name: ShowSuperHidden`| 15
`SOFTWAREWOW6432NODEMICROSOFTWINDOWS SCRIPT HOSTSETTINGS
Value Name: REG_DWORD`| 15
`SYSTEMCONTROLSET001SERVICESSCHEDULE
Value Name: Start`| 15
`SOFTWAREVB AND VBA PROGRAM SETTINGS`| 15
`SOFTWAREVB AND VBA PROGRAM SETTINGSMICROSOFT`| 15
`SOFTWAREVB AND VBA PROGRAM SETTINGSMICROSOFTSYSINTERNALS`| 15
`SOFTWAREMICROSOFTWINDOWS NTCURRENTVERSIONWINLOGON
Value Name: shell`| 15
`SOFTWAREVB AND VBA PROGRAM SETTINGSMICROSOFTSYSINTERNALS
Value Name: 9481`| 15
`SOFTWAREVB AND VBA PROGRAM SETTINGSMICROSOFTSYSINTERNALS
Value Name: PROCID`| 15
Mutexes| Occurrences
—|—
`4919245`| 15
`83729184726481`| 15
Domain Names contacted by malware. Does not indicate maliciousness| Occurrences
—|—
`klobert[.]no-ip[.]biz`| 15
Files and or directories created| Occurrences
—|—
`%APPDATA%msconfig.ini`| 15
`%SystemRoot%SysWOW64Windows Server`| 15
`%SystemRoot%SysWOW64Windows Serverwserver.exe`| 15
#### File Hashes
`07acf6655f3bd9f7efb8fb9673abf14a91d8e53c9c8b3d1712b730f79301b4dd`
`10a24172f7877aa5174373a5a66f03d9e8239212ce0a4069b9f9f7a8fb8d869b`
`344232ecff398382a51f3821fe03aed41419ed5d4bd9cdf1e2538c6504971dd5`
`45109c4b615ac61874e8559bc29c1e7aa4763963349870e3167a45c1e5e2b8d5`
`5901a1c2ee44b552a1de4ace0c80f12fc599b960bef0376b539322dcf3aa3d51`
`734d82c665505125a70f3d0fa5efb17a0d83bdbe41e4f65fb086380610267293`
`8c6b4b0dee6804fc5099abeb62c65e1ebcb44d44dacaaab862534b4da2628495`
`a44d872660a3f839106f90c931aafd42471aded2897f1001fd43bac172829ae3`
`a86ff8947d470e364a74a4472ba36d7d012ca8cd160114ec49338dbcfe8b6b5d`
`a8fc38426ef5e166448dfa69708bd765e684f2c2458d15630b8be8d2ee87e251`
`b011b70a43700abfe0ec72edac2223216485aba02192887b738443abd96a7fc5`
`c27c8c22462a0b8de5b80d3ca846ee400ae9f8e55da94b3595892358f88daf66`
`c3ef3d5a345574dbab0f1535f4617b96e95a330f647788d3cb56c83302f92be4`
`ea7485c628bce7f9b446ea559c3744cc7484aa2675f38298ea06beef15bc679d`
`eaf2c2366fbdc1ab0ba09c9358abf3969167e6fe9f9ba360654bdf7af3a26631`
#### Coverage
Product| Protection
—|—
Secure Endpoint| 
Cloudlock| N/A
CWS| 
Email Security| 
Network Security| N/A
Stealthwatch| N/A
Stealthwatch Cloud| N/A
Secure Malware Analytics| 
Umbrella| N/A
WSA| N/A
#### Screenshots of Detection
#### Secure Endpoint
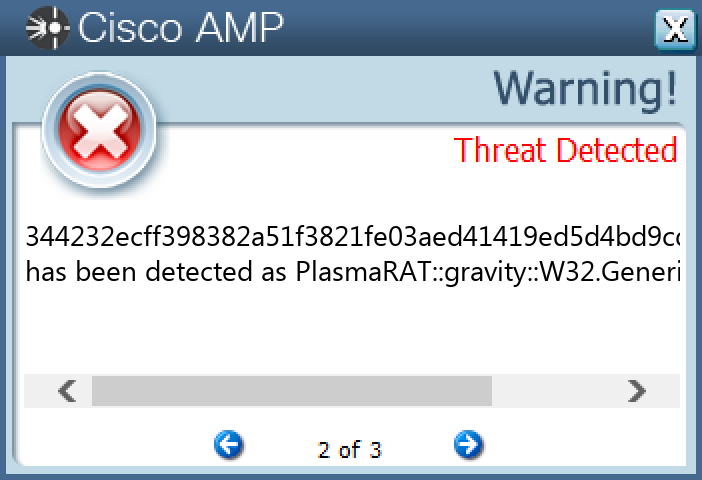
#### Secure Malware Analytics
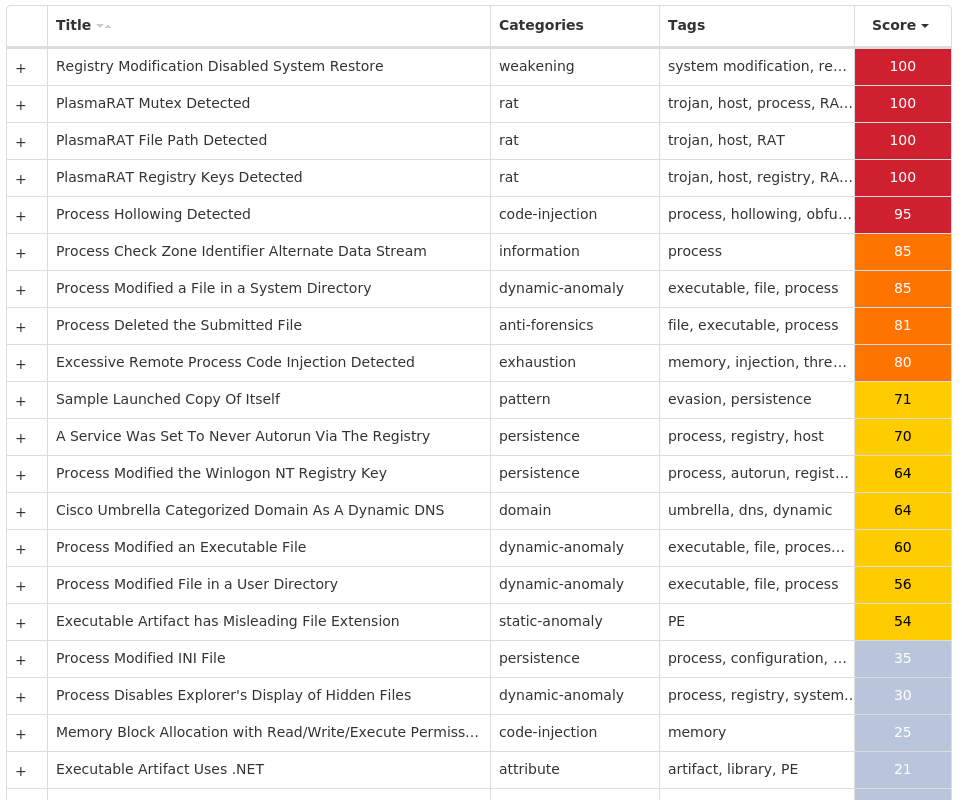
#### MITRE ATT&CK
* * *Read More
References

Back to Main


