
Today, Talos is publishing a glimpse into the most prevalent threats we’ve observed between March 17 and March 24. As with previous roundups, this post isn’t meant to be an in-depth analysis. Instead, this post will summarize the threats we’ve observed by highlighting key behavioral characteristics, indicators of compromise, and discussing how our customers are automatically protected from these threats.
As a reminder, the information provided for the following threats in this post is non-exhaustive and current as of the date of publication. Additionally, please keep in mind that IOC searching is only one part of threat hunting. Spotting a single IOC does not necessarily indicate maliciousness. Detection and coverage for the following threats is subject to updates, pending additional threat or vulnerability analysis. For the most current information, please refer to your Firepower Management Center, [Snort.org](), or [ClamAV.net]().
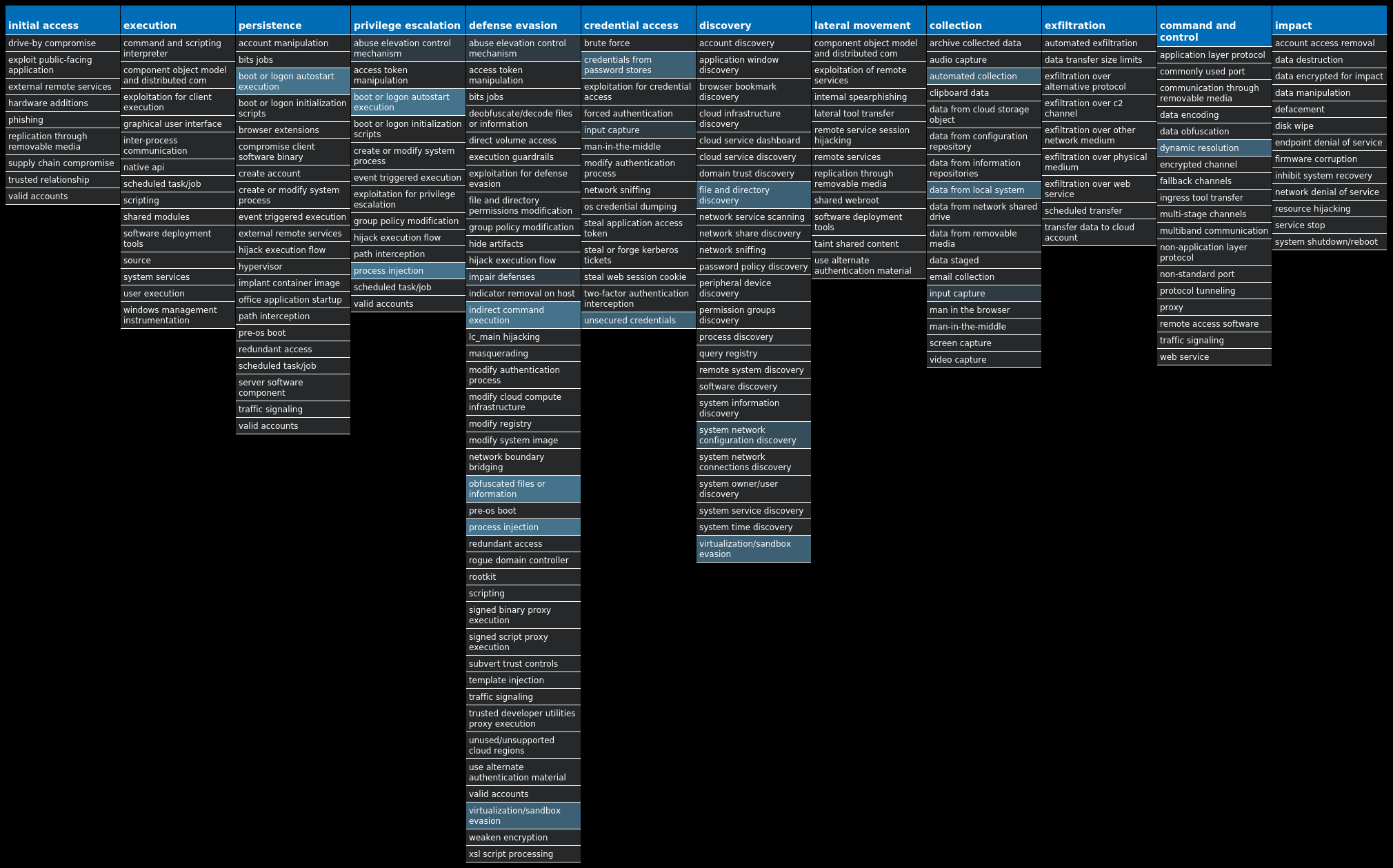
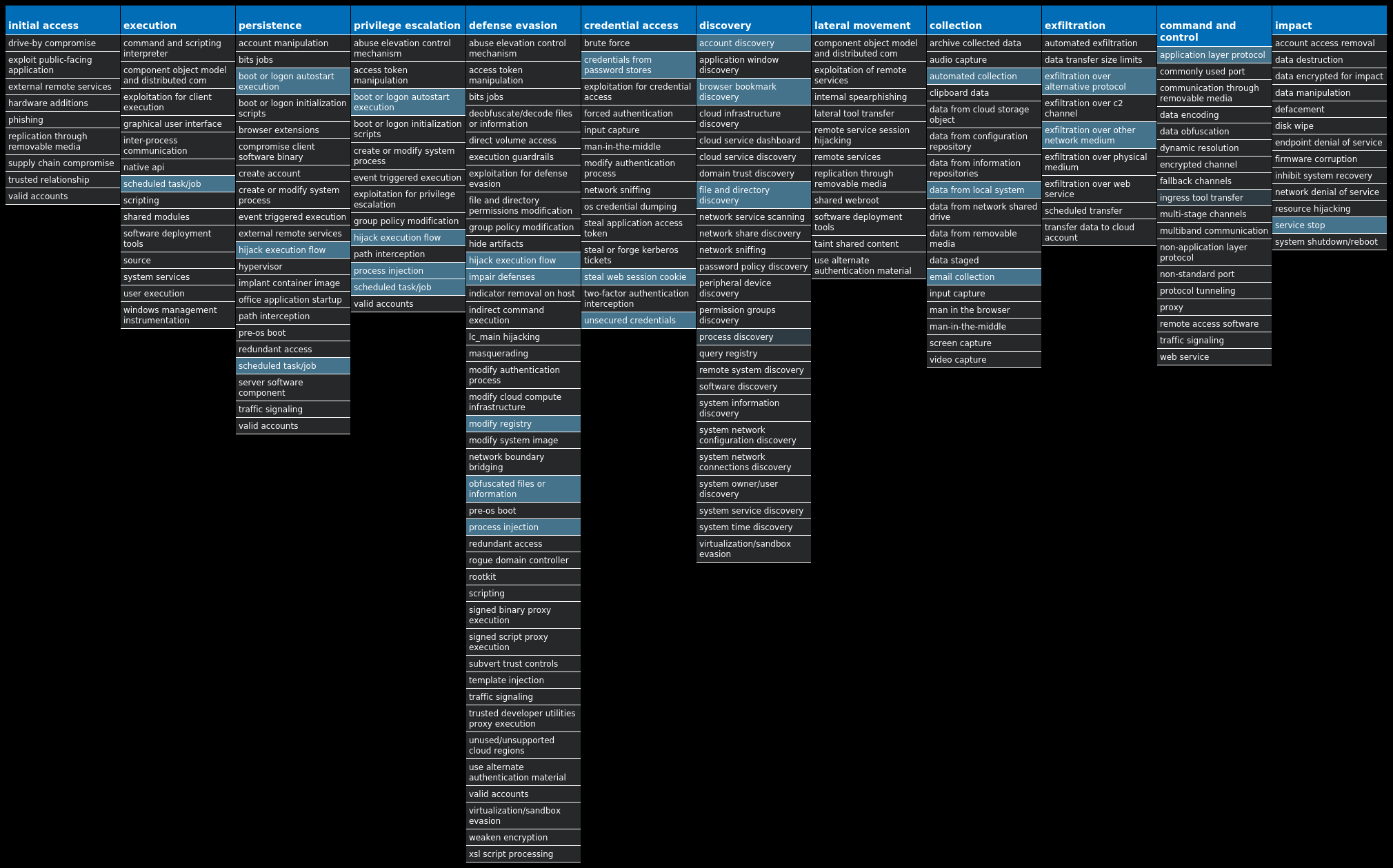
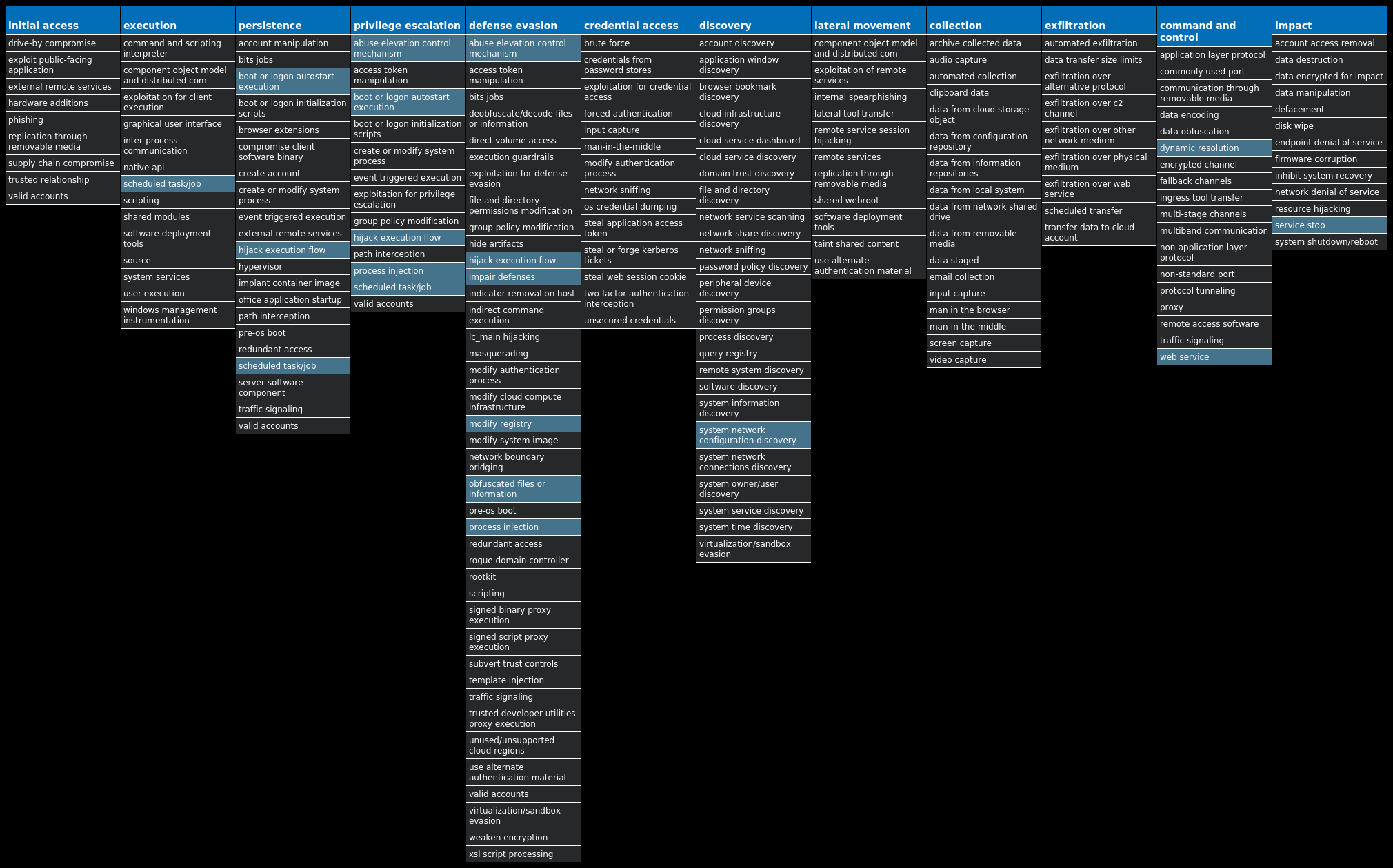
For each threat described below, this blog post only lists 25 of the associated file hashes and up to 25 IOCs for each category. An accompanying JSON file can be found [here]() that includes the complete list of file hashes, as well as all other IOCs from this post. A visual depiction of the MITRE ATT&CK techniques associated with each threat is also shown. In these images, the brightness of the technique indicates how prevalent it is across all threat files where dynamic analysis was conducted. There are five distinct shades that are used, with the darkest indicating that no files exhibited technique behavior and the brightest indicating that technique behavior was observed from 75 percent or more of the files.
The most prevalent threats highlighted in this roundup are:
Threat Name| Type| Description
—|—|—
Win.Dropper.Bifrost-9993163-0| Dropper| Bifrost is a backdoor with more than 10 variants. Bifrost uses the typical server, server builder and client backdoor program configuration to allow a remote attacker who uses the client to execute arbitrary code on the compromised machine. Bifrost contains standard RAT features such as a file manager, screen capture utility, keylogging, video recording, microphone and camera monitoring, and a process manager. To mark its presence in the system, Bifrost uses a mutex that may be named “Bif1234” or “Tr0gBot.”
Win.Dropper.Tofsee-9993367-0| Dropper| Tofsee is multi-purpose malware that features several modules used to carry out various activities such as sending spam messages, conducting click fraud, mining cryptocurrency, and more. Infected systems become part of the Tofsee spam botnet and are used to send large volumes of spam messages to infect additional systems and increase the size of the botnet.
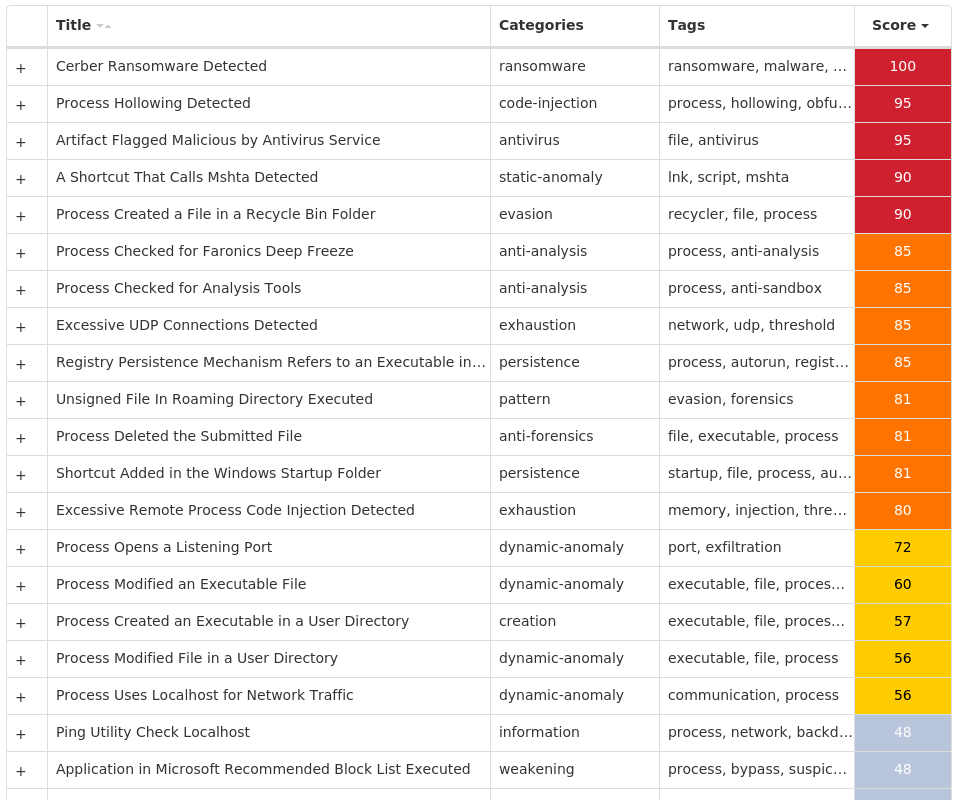
Win.Dropper.Cerber-9993689-0| Dropper| Cerber is ransomware that encrypts documents, photos, databases and other important files. Historically, this malware would replace files with encrypted versions and add the file extension “.cerber,” although in more recent campaigns, other file extensions are used.
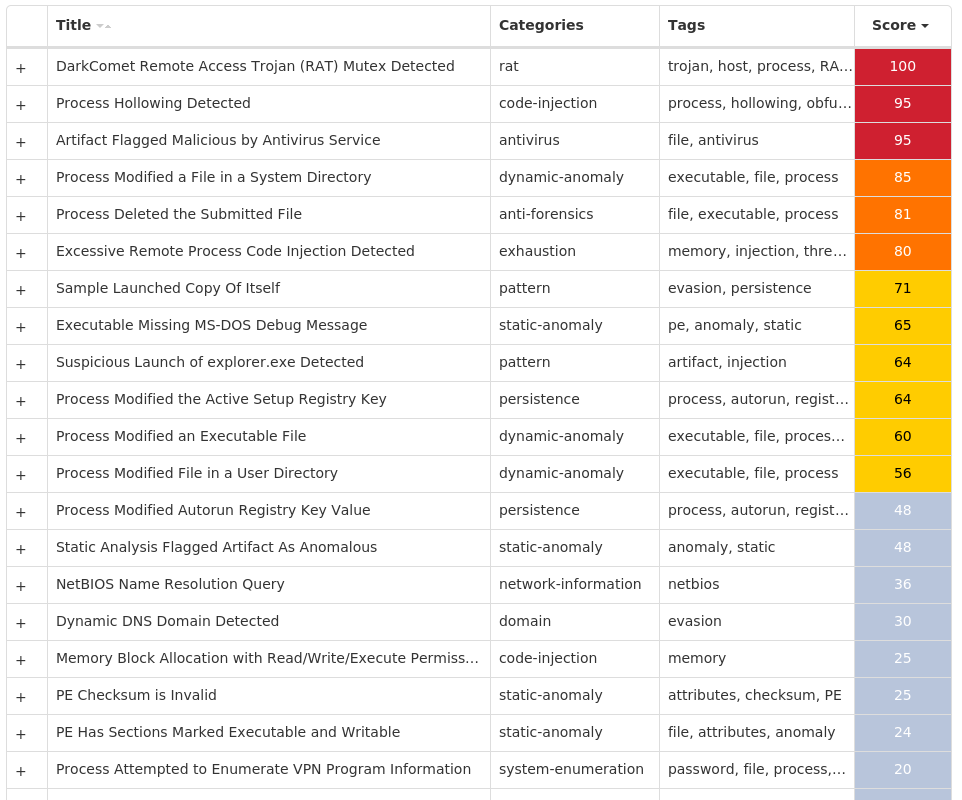
Win.Trojan.DarkComet-9993855-1| Trojan| DarkComet and related variants are a family of remote access trojans designed to provide an attacker with control over an infected system. Capabilities of this malware include the ability to download files from a user’s machine, mechanisms for persistence and hiding, and the ability to send back usernames and passwords from the infected system.
Win.Packed.Zusy-9993358-0| Packed| Zusy, also known as TinyBanker or Tinba, is a trojan that uses man-in-the-middle attacks to steal banking information. When executed, it injects itself into legitimate Windows processes such as “explorer.exe” and “winver.exe.” When the user accesses a banking website, it displays a form to trick the user into submitting personal information.
Win.Packed.Upatre-9993687-0| Packed| Upatre is a malicious downloader often used by exploit kits and phishing campaigns. Upatre downloads and executes malicious executables such as banking malware.
Win.Dropper.LokiBot-9993959-0| Dropper| Lokibot is an information-stealing malware designed to siphon sensitive information stored on an infected device. It is modular in nature, supporting the ability to steal sensitive information from several popular applications. It is commonly pushed via malicious documents delivered via spam emails.
Win.Virus.Ramnit-9993699-0| Virus| Ramnit is a banking trojan that monitors web browser activity on an infected machine and collects login information from financial websites. It also can steal browser cookies and attempts to hide from popular antivirus software.
* * *
## Threat Breakdown
### Win.Dropper.Bifrost-9993163-0
#### Indicators of Compromise
* IOCs collected from dynamic analysis of 21 samples
Registry Keys| Occurrences
—|—
`SOFTWAREWOW6432NODEMICROSOFTWINDOWSCURRENTVERSIONRUNONCE
Value Name: wextract_cleanup0`| 18
`SOFTWAREWOW6432NODEMICROSOFTACTIVE SETUPINSTALLED COMPONENTS{3G4L2686-J4L1-X5MV-12RE-JFH5V38F5030}
Value Name: StubPath`| 2
`SOFTWARECOFFIN OF EVIL
Value Name: FileName`| 2
`SYSTEMCONTROLSET001SERVICESDFMIRAGE
Value Name: Type`| 2
`SYSTEMCONTROLSET001SERVICESDFMIRAGE
Value Name: ErrorControl`| 2
`SYSTEMCONTROLSET001SERVICESDFMIRAGE
Value Name: Tag`| 2
`SYSTEMCONTROLSET001SERVICESDFMIRAGE
Value Name: ImagePath`| 2
`SYSTEMCONTROLSET001SERVICESDFMIRAGE
Value Name: Group`| 2
`SYSTEMCONTROLSET001SERVICESDFMIRAGE
Value Name: Start`| 2
`SYSTEMCONTROLSET001SERVICESEVENTLOGSYSTEMDFMIRAGE`| 2
`SYSTEMCONTROLSET001SERVICESDFMIRAGEDEVICE0`| 2
`SYSTEMCONTROLSET001CONTROLVIDEO{D3A43A86-910D-44AA-BF0C-18BDDCB118B6}`| 2
`SYSTEMCONTROLSET001CONTROLVIDEO{D3A43A86-910D-44AA-BF0C-18BDDCB118B6}VIDEO`| 2
`SYSTEMCONTROLSET001SERVICESDFMIRAGEVIDEO`| 2
`SYSTEMCONTROLSET001CONTROLVIDEO{D3A43A86-910D-44AA-BF0C-18BDDCB118B6}000`| 2
`SYSTEMCONTROLSET001CONTROLCLASS{4D36E968-E325-11CE-BFC1-08002BE10318}003SETTINGS`| 2
`SOFTWAREMICROSOFTWINDOWS NTCURRENTVERSIONINVIDEOINSTALL`| 2
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONSETUPPNPLOCKDOWNFILES
Value Name: %SystemPath%system32DRIVERSdfmirage.sys`| 2
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONSETUPPNPLOCKDOWNFILES
Value Name: %SystemPath%system32dfmirage.dll`| 2
`SYSTEMCONTROLSET001CONTROLGROUPORDERLIST
Value Name: Video`| 2
`SYSTEMCONTROLSET001SERVICESEVENTLOGSYSTEMDFMIRAGE
Value Name: EventMessageFile`| 2
`SYSTEMCONTROLSET001SERVICESEVENTLOGSYSTEMDFMIRAGE
Value Name: TypesSupported`| 2
`SYSTEMCONTROLSET001SERVICESDFMIRAGEDEVICE0
Value Name: HighResBootCompatible`| 2
`SYSTEMCONTROLSET001SERVICESDFMIRAGEDEVICE0
Value Name: CapabilityOverride`| 2
`SYSTEMCONTROLSET001SERVICESDFMIRAGEDEVICE0
Value Name: InstalledDisplayDrivers`| 2
Mutexes| Occurrences
—|—
`Bif1234`| 8
`Global`| 5
`DrvInst.exe_mutex_{5B10AC83-4F13-4fde-8C0B-B85681BA8D73}`| 2
`Spy-Net`| 2
`Spy-Net_Persist`| 2
`Spy-Net_Sair`| 2
`SetuplogMutex`| 2
`Bif123`| 1
Domain Names contacted by malware. Does not indicate maliciousness| Occurrences
—|—
`clmat73[.]duckdns[.]org`| 2
Files and or directories created| Occurrences
—|—
`%TEMP%IXP000.TMPStub.exe`| 6
`%TEMP%IXP000.TMPhaZl0oh.exe`| 6
`%TEMP%IXP000.TMPSERVER.EXE`| 3
`%SystemRoot%SysWOW64logs.dat`| 2
`%SystemRoot%SysWOW64Coffin Of Evil.exe`| 2
`%System32%CatRoot{F750E6C3-38EE-11D1-85E5-00C04FC295EE}oem3.CAT`| 2
`%SystemRoot%INFoem3.inf`| 2
`%System32%DriverStoreINFCACHE.0`| 2
`%SystemRoot%INFoem3.PNF`| 2
`%APPDATA%MastersoftMirage DriverZOOKDriverSetup.exe`| 2
`%APPDATA%MastersoftMirage Driverdfmirage.cat`| 2
`%APPDATA%MastersoftMirage Driverdfmirage.inf`| 2
`%APPDATA%MastersoftMirage Driverx64dfmirage.dll`| 2
`%APPDATA%MastersoftMirage Driverx64dfmirage.sys`| 2
`%APPDATA%MastersoftMirage Driverx86`| 2
`%System32%DriverStoreFileRepositorydfmirage.inf_%PROCESSOR_ARCHITECTURE%_neutral_83b5f055f9286973`| 2
`%TEMP%IXP000.TMPäæÃâ¡ÃÂ.EXE`| 2
`%System32%DriverStoreFileRepositorydfmirage.inf_%PROCESSOR_ARCHITECTURE%_neutral_83b5f055f9286973dfmirage.PNF`| 2
`%System32%DriverStoreFileRepositorydfmirage.inf_%PROCESSOR_ARCHITECTURE%_neutral_83b5f055f9286973x64`| 2
`%TEMP%IXP000.TMPZOOKDriverSetup.exe`| 2
`%TEMP%IXP000.TMPZOOKDriverSetup64.exe`| 2
`%TEMP%IXP000.TMPdfmirage.cat`| 2
`%TEMP%IXP000.TMPdfmirage.dll`| 2
`%TEMP%IXP000.TMPdfmirage.inf`| 2
`%TEMP%IXP000.TMPdfmirage.sys`| 2
*See JSON for more IOCs
#### File Hashes
`0199b8abacc6d10add7b87ba0baf97673e638782ca43b6336ad6da87ce599d1d`
`0357d948e0ad1377a41b06db264b67433553388074496e8a3b9d7e0d464dcfd8`
`0a98d4c81b1abdad17061c0ddec9d6239b4b7141523fe0ed45f9621d01b98583`
`1171fa5d8b2597e9d372c04c0c889f0d99a1074e545ffe2888f1e88a5c999e35`
`14a4c1408da2ae0d9762d82a2161a8a567e425c5b3543c3e9fe225d9aeb680db`
`28cbab6d8ef92706eab11d26cd9ef93fa511b3433790065f88f70f8cbeb86d89`
`3b1c14bda01283311dd7f62882fd74e65735202f635323be30a5f98c0e2d009f`
`4beed9c0549d7ada7dc8ad39669dbad611648c9b8957bc3e25298e00994a0b0f`
`52da358a1b38f8105dd6f19c2601de4fc803cfdcd3b22c473f27701948cb6040`
`54cec1ab049ef4eeca383b00c00e4a2a9845ca58edf123290a60563bc70fa7ce`
`6d8e6e013c7f00884bfb72c06f5d7056b52aa83679a167f4ebf3393c28cfe3bd`
`a2da494eb48b27c0866db394d9da53b78210dd4c68a8fcc68925d5124f9ffdc0`
`aa6482bcaad1facc238ada6b4c550c58acb522cae7502648db8ced6033bde2fa`
`c329a63536aba1515a27e9df136521f49a4f28e905e05c351530a77591403c69`
`c34c66c001427f13ea2927c30d8a7c2e391079deedc02e697837da643334b968`
`cbc8e3d5589a02eef1f1ec1d96870903bc3ce6a445abc6271b7b777f1319d34c`
`d1c56ea372d6245f633d594be70cb61ffdfa5199d140823de63479aaf5872557`
`d47657ffcd7eb8fef58015ef781d47c732220b9652ff4ad225fbb4ed9563ec19`
`db69691fa03da43646cf603dd7c73982d27be89c1cb9b4d3badd3576e42d1832`
`de11ca3b3f81a5b7a9d6d3b6bdb0f23000cd82c4ead1e9c199147776b24fcd9e`
`df8dabcc26df0e40c3e2e2ed7b9477891aeaaa8ee1a1d7f227c83d81b07fe9b2`
#### Coverage
Product| Protection
—|—
Secure Endpoint| 
Cloudlock| N/A
CWS| 
Email Security| 
Network Security| N/A
Stealthwatch| N/A
Stealthwatch Cloud| N/A
Secure Malware Analytics| 
Umbrella| N/A
WSA| N/A
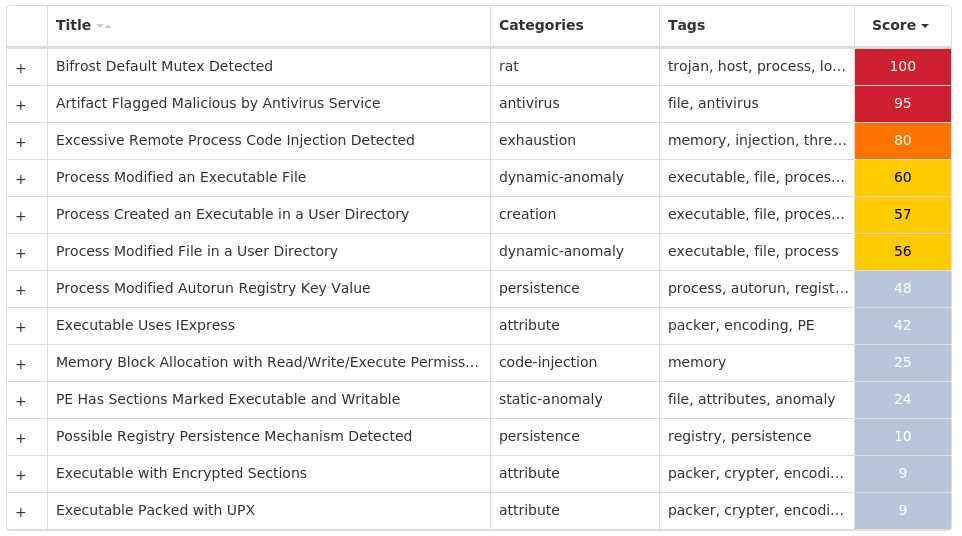
#### Screenshots of Detection
#### Secure Endpoint
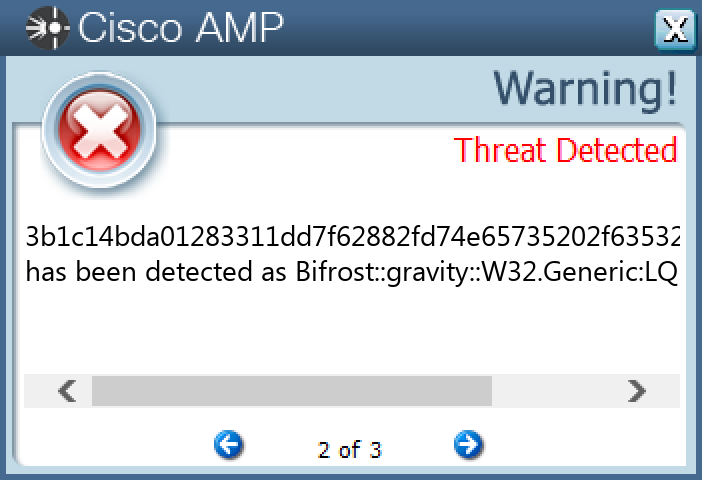
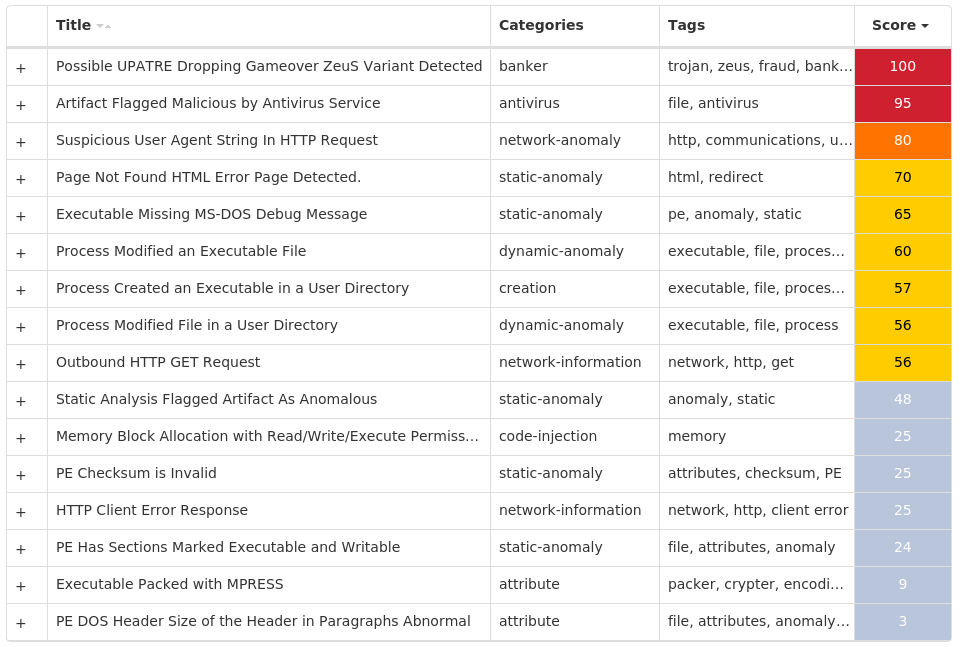
#### Secure Malware Analytics
#### MITRE ATT&CK

* * *
### Win.Dropper.Tofsee-9993367-0
#### Indicators of Compromise
* IOCs collected from dynamic analysis of 45 samples
Registry Keys| Occurrences
—|—
`SOFTWAREPOLICIESMICROSOFTWINDOWS DEFENDER
Value Name: DisableAntiSpyware`| 16
`SYSTEMCONTROLSET001SERVICESWINDEFEND
Value Name: Start`| 16
`SOFTWAREPOLICIESMICROSOFTWINDOWSWINDOWSUPDATEAU`| 16
`SOFTWAREPOLICIESMICROSOFTWINDOWSWINDOWSUPDATEAU
Value Name: NoAutoRebootWithLoggedOnUsers`| 16
`SYSTEMCONTROLSET001SERVICESWUAUSERV
Value Name: Start`| 16
`SOFTWAREPOLICIESMICROSOFTWINDOWSWINDOWSUPDATEAU
Value Name: NoAutoUpdate`| 16
`SOFTWAREPOLICIESMICROSOFTWINDOWS DEFENDERREAL-TIME PROTECTION
Value Name: DisableBehaviorMonitoring`| 16
`SOFTWAREPOLICIESMICROSOFTWINDOWS DEFENDERREAL-TIME PROTECTION
Value Name: DisableOnAccessProtection`| 16
`SOFTWAREPOLICIESMICROSOFTWINDOWS DEFENDERREAL-TIME PROTECTION
Value Name: DisableScanOnRealtimeEnable`| 16
`SOFTWAREPOLICIESMICROSOFTWINDOWS DEFENDERREAL-TIME PROTECTION
Value Name: DisableIOAVProtection`| 16
`SOFTWAREPOLICIESMICROSOFTWINDOWS DEFENDER`| 16
`SOFTWAREPOLICIESMICROSOFTWINDOWS DEFENDERREAL-TIME PROTECTION`| 16
`SOFTWAREPOLICIESMICROSOFTWINDOWSWINDOWSUPDATE`| 16
`SOFTWAREWOW6432NODEMICROSOFTWINDOWS DEFENDERFEATURES`| 16
`SOFTWAREWOW6432NODEMICROSOFTWINDOWS DEFENDERFEATURES
Value Name: TamperProtection`| 16
`SOFTWAREPOLICIESMICROSOFTWINDOWS DEFENDERREAL-TIME PROTECTION
Value Name: DisableRealtimeMonitoring`| 16
`SOFTWAREPOLICIESMICROSOFTWINDOWS DEFENDER SECURITY CENTER`| 16
`SOFTWAREPOLICIESMICROSOFTWINDOWSWINDOWSUPDATEAU
Value Name: AUOptions`| 16
`SOFTWAREPOLICIESMICROSOFTWINDOWSWINDOWSUPDATEAU
Value Name: AutoInstallMinorUpdates`| 16
`SOFTWAREPOLICIESMICROSOFTWINDOWS DEFENDER SECURITY CENTERNOTIFICATIONS`| 16
`SOFTWAREPOLICIESMICROSOFTWINDOWS DEFENDER SECURITY CENTERNOTIFICATIONS
Value Name: DisableNotifications`| 16
`SOFTWAREPOLICIESMICROSOFTWINDOWSWINDOWSUPDATEAU
Value Name: UseWUServer`| 16
`SOFTWAREPOLICIESMICROSOFTWINDOWSWINDOWSUPDATE
Value Name: DoNotConnectToWindowsUpdateInternetLocations`| 16
`SOFTWAREWOW6432NODEMICROSOFTWINDOWSCURRENTVERSIONRUNONCE
Value Name: wextract_cleanup0`| 9
`SOFTWAREWOW6432NODEMICROSOFTWINDOWSCURRENTVERSIONRUNONCE
Value Name: wextract_cleanup1`| 9
Mutexes| Occurrences
—|—
`Global`| 9
`006700e5a2ab05704bbb0c589b88924d`| 7
`{1D6FC66E-D1F3-422C-8A53-C0BBCF3D900D}`| 5
`M5/610HP/STAGE2`| 5
IP Addresses contacted by malware. Does not indicate maliciousness| Occurrences
—|—
`193[.]233[.]20[.]28`| 15
`31[.]41[.]244[.]200`| 7
`149[.]154[.]167[.]99`| 5
`162[.]0[.]217[.]254`| 5
`45[.]159[.]189[.]105`| 5
`116[.]203[.]13[.]130`| 5
`151[.]251[.]19[.]81`| 3
`80[.]66[.]75[.]254`| 2
`86[.]122[.]83[.]142`| 2
`176[.]124[.]193[.]51`| 2
`194[.]25[.]134[.]50`| 1
`104[.]47[.]53[.]36`| 1
`67[.]195[.]204[.]151`| 1
`104[.]47[.]18[.]97`| 1
`37[.]1[.]217[.]172`| 1
`176[.]113[.]115[.]136`| 1
`37[.]34[.]248[.]24`| 1
`109[.]98[.]58[.]98`| 1
`157[.]240[.]241[.]63`| 1
`186[.]182[.]55[.]44`| 1
`142[.]251[.]40[.]164`| 1
`20[.]112[.]52[.]29`| 1
`20[.]103[.]85[.]33`| 1
`211[.]171[.]233[.]129`| 1
`58[.]235[.]189[.]192`| 1
*See JSON for more IOCs
Domain Names contacted by malware. Does not indicate maliciousness| Occurrences
—|—
`t[.]me`| 5
`api[.]2ip[.]ua`| 5
`uaery[.]top`| 5
`zexeq[.]com`| 5
`microsoft-com[.]mail[.]protection[.]outlook[.]com`| 2
`microsoft[.]com`| 2
`muspelheim[.]be`| 2
`249[.]5[.]55[.]69[.]bl[.]spamcop[.]net`| 1
`249[.]5[.]55[.]69[.]cbl[.]abuseat[.]org`| 1
`249[.]5[.]55[.]69[.]dnsbl[.]sorbs[.]net`| 1
`249[.]5[.]55[.]69[.]in-addr[.]arpa`| 1
`249[.]5[.]55[.]69[.]sbl-xbl[.]spamhaus[.]org`| 1
`249[.]5[.]55[.]69[.]zen[.]spamhaus[.]org`| 1
`i[.]instagram[.]com`| 1
`work[.]a-poster[.]info`| 1
`www[.]google[.]com`| 1
`login[.]yahoo[.]com`| 1
`www[.]tiktok[.]com`| 1
`login[.]live[.]com`| 1
`imap[.]t-online[.]de`| 1
`api[.]steampowered[.]com`| 1
`static[.]cdninstagram[.]com`| 1
`android[.]litres[.]ru`| 1
`jnb-efz[.]ms-acdc[.]office[.]com`| 1
`smtp[.]mail[.]yahoo[.]co[.]jp`| 1
*See JSON for more IOCs
Files and or directories created| Occurrences
—|—
`%LOCALAPPDATA%Yandex`| 15
`%LOCALAPPDATA%YandexYaAddon`| 15
`%TEMP%IXP001.TMP`| 9
`%TEMP%IXP001.TMPTMP4351$.TMP`| 9
`%TEMP%IXP002.TMP`| 9
`%TEMP%IXP002.TMPTMP4351$.TMP`| 9
`%TEMP%IXP003.TMP`| 9
`%TEMP%IXP003.TMPTMP4351$.TMP`| 9
`%TEMP%5975271bda`| 7
`%TEMP%5975271bdametafor.exe`| 7
`%System32%Tasksmetafor.exe`| 7
`%TEMP%IXP001.TMPen738609.exe`| 6
`%TEMP%IXP001.TMPkino7002.exe`| 6
`%TEMP%IXP002.TMPdtR78s46.exe`| 6
`%TEMP%IXP002.TMPkino3035.exe`| 6
`%TEMP%IXP003.TMPbus5992.exe`| 6
`%TEMP%IXP003.TMPcon7447.exe`| 6
`%TEMP%IXP000.TMPge884549.exe`| 6
`%TEMP%IXP000.TMPkino3798.exe`| 6
`%APPDATA%MicrosoftNetwork`| 5
`I:5d2860c89d774.jpg`| 5
`SystemID`| 5
`SystemIDPersonalID.txt`| 5
`%LOCALAPPDATA%bowsakkdestx.txt`| 5
`%System32%TasksTime Trigger Task`| 5
*See JSON for more IOCs
#### File Hashes
`03924699129f7f0b9a65041a4dcf96185004b90bd4d6017adfd720412630fbd4`
`03c857615f0b6602b4e501076ba73602b16531b6d83a2aa40e3ea38fb6909418`
`198fcd646496fa679b3ee7127d0dbae4eb42776f3789562afb8c4afff0caec72`
`1a31c3549256936581d375838891a8ad4a71cbd05d225a186e99b5296a25916e`
`1c7cd8e86443aa599665ef2c4d1264f9efd82b4d4d6e0460a18b97c2f1582aea`
`26515e880aaf2e119424c894836ed5c79a590c4764f4bae20d473d217832a01d`
`2849b4a5145d840a746643b01050e13c0bc35151413da47d5b174a00c64b1c73`
`337d917fe321f1e54f3927061475587a278314b7c8266955430bb4b8876cdf4a`
`4228742b043c47e0780ba276d9a8723ed7a510f22d201648122df1cd25802468`
`4521bf6f882807bdbb0c8f5f044c1415a543e2ca257ead36fba04c6a7919e6c0`
`4be0b658faf09a05495a9ae17ac6c58ec392ed6c4624859fc1c5b275eb36f627`
`4e421a44146530c1ac6f0976024b53c3c86d8be05d0f446bc95510de7eeb3925`
`521a9ce550a408da634f02b39b4f8d18c37d9a4a5aa4c92948532dd175afe0ea`
`5a66c05a5d48e8c178f9e656ba1cc6e124e552af6d947af29e3afcb435dd31ce`
`605a483757ecf0738b4b4a019a46a4d6b9e3fc07b6e845f0264b27821df1078c`
`6c4911f38de2b08a9e7015453aeed31956019d78a1219f60dd79c10b3e0b3141`
`6c737394b6f8c4fe504730f4bd3d8c66d6b2e625bf05214c1c4b409f5b0cd3a8`
`6fd8c636c94dc1380aef341cde76a40a02ee7e18161daee955c45c5004d88fb3`
`74f7c20fdee2b0e569b3fc7d42521c2b55b3c280d5e7bc8a767ccef5ab5c17ff`
`768eef12b8082acde11a4d3b62bd5424f8e95bb83f1b7b7a5bc4c62531ff2e20`
`83831a5b5db3553e3a122b266d889349a3380414c27e322266e9d93926831180`
`840b2b2bd08ec79d19b5504debdbad612518346599444e676e23789a8455047d`
`847d9652c563b3315fc34fd708aecdde038aec8c2fb13997a72b6fd894579e34`
`8ce009fe7fadda76ddcc21248231af4358fa92e7f877e73f0e37726476f85b01`
`908bc59262f91f2c86e1159957b7b9adfd6ab186cafd4f767d8723cc5ceeda7d`
*See JSON for more IOCs
#### Coverage
Product| Protection
—|—
Secure Endpoint| 
Cloudlock| N/A
CWS| 
Email Security| 
Network Security| 
Stealthwatch| N/A
Stealthwatch Cloud| N/A
Secure Malware Analytics| 
Umbrella| 
WSA| 
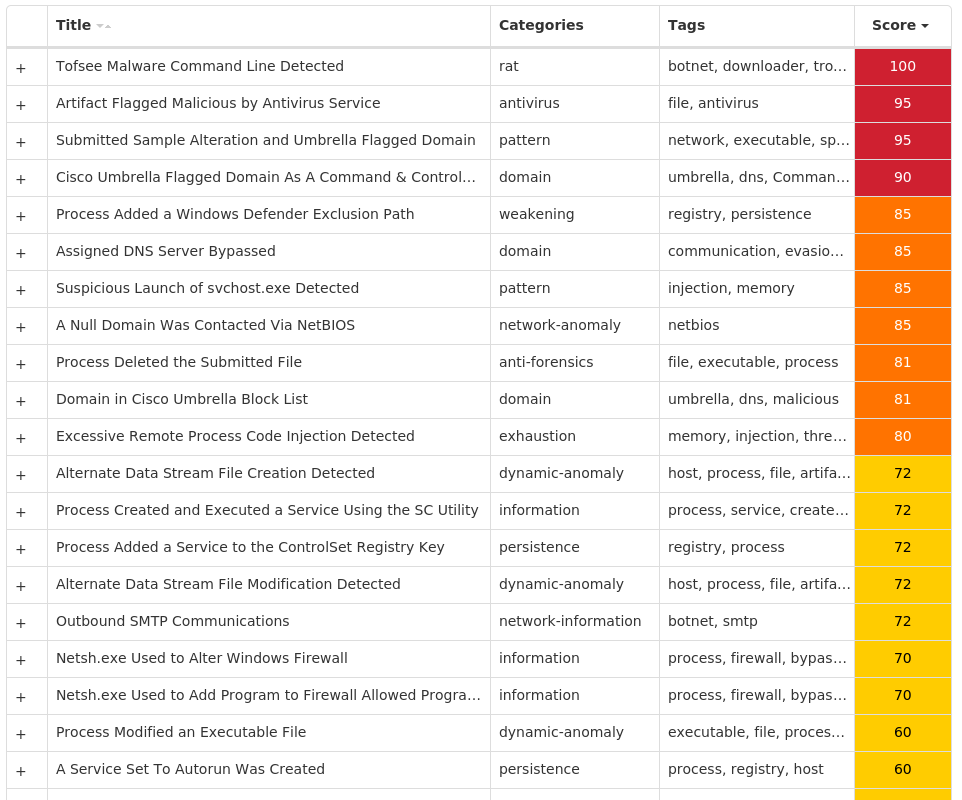
#### Screenshots of Detection
#### Secure Endpoint
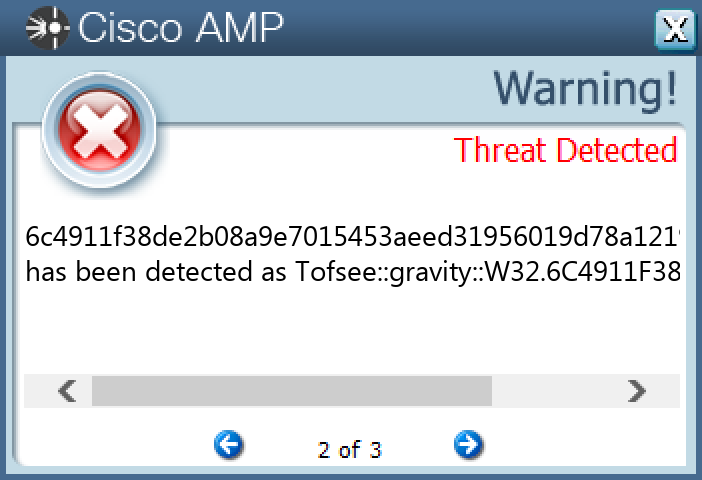
#### Secure Malware Analytics
#### MITRE ATT&CK

* * *
### Win.Dropper.Cerber-9993689-0
#### Indicators of Compromise
* IOCs collected from dynamic analysis of 119 samples
Registry Keys| Occurrences
—|—
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONEXPLORERADVANCED
Value Name: ShowSuperHidden`| 56
`SOFTWAREMICROSOFTOUTLOOK EXPRESS5.0`| 54
`SOFTWAREMICROSOFTOUTLOOK EXPRESS5.0SHARED SETTINGSSETUP30002`| 54
`SOFTWAREMICROSOFTOUTLOOK EXPRESS5.0SHARED SETTINGSSETUP30002
Value Name: DS@Busf`| 54
`SOFTWAREMICROSOFTOUTLOOK EXPRESS5.0SHARED SETTINGSSETUP30002
Value Name: ET@Busf`| 54
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONEXPLORERDISCARDABLEPOSTSETUPCOMPONENT CATEGORIES{F3F18253-2050-E690-FED7-0BE7DF1E790D}`| 54
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONEXPLORERDISCARDABLEPOSTSETUPCOMPONENT CATEGORIES{F3F18253-2050-E690-FED7-0BE7DF1E790D}ENUM`| 54
`SOFTWAREMICROSOFTOUTLOOK EXPRESS`| 54
`SOFTWAREMICROSOFTOUTLOOK EXPRESS5.0SHARED SETTINGS`| 54
`SOFTWAREMICROSOFTOUTLOOK EXPRESS5.0SHARED SETTINGSSETUP`| 54
`SOFTWAREMICROSOFTOUTLOOK EXPRESS5.0SHARED SETTINGSSETUP30002
Value Name: ET@Cu~d`| 54
`SOFTWAREMICROSOFTOUTLOOK EXPRESS5.0SHARED SETTINGSSETUP10002`| 34
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: Adobe System Incorporated`| 11
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: Uoawaq`| 11
`SOFTWAREWOW6432NODEMICROSOFTWINDOWS NTCURRENTVERSIONWINLOGON
Value Name: Taskman`| 5
`SOFTWAREMICROSOFTWINDOWS NTCURRENTVERSIONWINLOGON
Value Name: Shell`| 5
`SYSTEMCONTROLSET001SERVICESWSCSVC
Value Name: Start`| 4
`SYSTEMCONTROLSET001SERVICESWINDEFEND
Value Name: Start`| 4
`SYSTEMCONTROLSET001SERVICESMPSSVC
Value Name: Start`| 4
`SYSTEMCONTROLSET001SERVICESWUAUSERV
Value Name: Start`| 4
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONPOLICIESSYSTEM
Value Name: EnableLUA`| 3
`SYSTEMCONTROLSET001SERVICESSHAREDACCESS
Value Name: Start`| 3
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONPOLICIESEXPLORER
Value Name: TaskbarNoNotification`| 3
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONPOLICIESEXPLORER
Value Name: TaskbarNoNotification`| 3
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONPOLICIESEXPLORER
Value Name: HideSCAHealth`| 3
Mutexes| Occurrences
—|—
`Frz_State`| 54
`shell.{C7036634-CCD0-7DFF-8826-3DEB3B7F4A3E}`| 54
`shell.{18A81F10-BD38-0CDB-EF51-7696490D1424}`| 54
`c731200`| 12
`SSLOADasdasc000300`| 11
`-43993de0Mutex`| 11
`SVCHOST_MUTEX_OBJECT_RELEASED_c000300`| 11
`FvLQ49Ia⬔Ãâ¬zLjj6m`| 11
`SSLOADasdasc000900`| 1
`GH5K-GKL8-CPP4-DE24`| 1
`Local{A95EDA1C-EEE2-09FD-FF48-D36CE9A5618F}`| 1
`Local{DB29A428-90D6-7B8A-FF48-D36CE9A5618F}`| 1
`Local{12B0A59F-9161-B213-FF48-D36CE9A5618F}`| 1
`Local{E54AD8D8-EC26-45E9-FF48-D36CE9A5618F}`| 1
`SVCHOST_MUTEX_OBJECT_RELEASED_c000900`| 1
`-65b46629Mutex`| 1
`FvLQ49IÃÂÃâ¬zLjj6m`| 1
`GLOBAL{}`| 1
`{FFCEE3F2-AB33-AF5A-6FA1-731547ACF820}`| 1
`Globalw5kSbK8156j`| 1
`GlobalV3W6x3pCHBS3`| 1
`GlobalfdjfidjOIAFJ`| 1
`GlobaluAvO6F8bgarN`| 1
`Wipdjrgugx`| 1
`Wipdjrgugx_970`| 1
IP Addresses contacted by malware. Does not indicate maliciousness| Occurrences
—|—
`146[.]185[.]220[.]111`| 54
`199[.]2[.]137[.]29`| 11
`94[.]220[.]232[.]237`| 9
`37[.]143[.]193[.]119`| 7
`72[.]12[.]192[.]41`| 7
`37[.]49[.]224[.]80`| 7
`74[.]242[.]165[.]171`| 7
`132[.]206[.]107[.]8`| 6
`122[.]133[.]88[.]223`| 6
`219[.]66[.]179[.]33`| 6
`99[.]198[.]64[.]149`| 6
`173[.]16[.]22[.]29`| 6
`68[.]41[.]230[.]151`| 6
`72[.]195[.]181[.]32`| 6
`190[.]105[.]70[.]165`| 6
`150[.]107[.]214[.]94`| 6
`221[.]154[.]138[.]182`| 6
`186[.]10[.]71[.]45`| 6
`138[.]130[.]68[.]113`| 6
`182[.]74[.]9[.]51`| 5
`60[.]62[.]134[.]208`| 5
`217[.]117[.]7[.]115`| 5
`172[.]242[.]113[.]103`| 5
`75[.]105[.]52[.]218`| 5
`114[.]35[.]114[.]129`| 5
*See JSON for more IOCs
Domain Names contacted by malware. Does not indicate maliciousness| Occurrences
—|—
`api[.]wipmania[.]com`| 12
`a[.]najwahaifamelema2[.]com`| 11
`a[.]najwahaifamelema3[.]com`| 11
`a[.]najwahaifamelema4[.]com`| 11
`a[.]najwahaifamelema5[.]com`| 11
`a[.]najwahaifamelema6[.]com`| 11
`a[.]najwahaifamelema7[.]com`| 11
`a[.]najwahaifamelema8[.]com`| 11
`a[.]najwahaifamelema9[.]com`| 11
`a[.]najwahaifamelema10[.]com`| 11
`a[.]najwahaifamelema11[.]com`| 11
`a[.]najwahaifamelema12[.]com`| 11
`a[.]najwahaifamelema13[.]com`| 11
`a[.]najwahaifamelema1[.]com`| 11
`a[.]najwahaifamelema14[.]com`| 11
`a[.]najwahaifamelema15[.]com`| 11
`nutqlfkq123a5[.]com`| 2
`nutqlfkq123a6[.]com`| 2
`nutqlfkq123a9[.]com`| 2
`nutqlfkq123a1[.]com`| 2
`nutqlfkq123a10[.]com`| 2
`nutqlfkq123a2[.]com`| 2
`nutqlfkq123a3[.]com`| 2
`nutqlfkq123a4[.]com`| 2
`count-x[.]com`| 2
*See JSON for more IOCs
Files and or directories created| Occurrences
—|—
`$Recycle.binS-1-5-21-2580483871-590521980-3826313501-500$ast-S-1-5-21-2580483871-590521980-3826313501-500`| 54
`%APPDATA%MicrosoftWindowsIEUpdate`| 54
`%TEMP%tmp.tmp`| 54
`$RECYCLE.BIN.lnk`| 12
`System_Volume_Information.lnk`| 12
`jsdrpAj.exe`| 12
`E:$RECYCLE.BIN.lnk`| 12
`E:System_Volume_Information.lnk`| 12
`E:c731200`| 12
`E:jsdrpAj.exe`| 12
`%APPDATA%c731200`| 12
`%TEMP%c731200`| 12
`%TEMP%Adobe`| 11
`%TEMP%AdobeReader_sl.exe`| 11
`%APPDATA%IdentitiesUoawaq.exe`| 11
`RECYCLER`| 5
`%APPDATA%MicrosoftWindowsStart MenuProgramsStartUpcipher.lnk`| 3
`%APPDATA%MicrosoftWindowsIEUpdatecipher.exe`| 3
`%APPDATA%MicrosoftWindowsStart MenuProgramsStartUpxpsrchvw.lnk`| 2
`%APPDATA%MicrosoftWindowsStart MenuProgramsStartUpwuapp.lnk`| 2
`%APPDATA%MicrosoftWindowsStart MenuProgramsStartUpntkrnlpa.lnk`| 2
`%APPDATA%MicrosoftWindowsStart MenuProgramsStartUpCertEnrollCtrl.lnk`| 2
`%APPDATA%MicrosoftWindowsStart MenuProgramsStartUpPkgMgr.lnk`| 2
`%APPDATA%MicrosoftWindowsStart MenuProgramsStartUpDism.lnk`| 2
`%APPDATA%MicrosoftWindowsIEUpdateDism.exe`| 2
*See JSON for more IOCs
#### File Hashes
`00ec05a0fd4ccd413e28f89d1443089eda2e50becdc97e2b44a6e74c55d65fb8`
`037e63fa3cfd335313e3cb78d14b0e0a779c4da19a7646d75403858a879d70f9`
`0529bd46932a20e14da07133bd2614e7f81ef08a6ad26764ef9d732dd4988e35`
`060fb684fd152f2546906c5b85485c24d4e94c7b5e8b93458097d7014154ccc9`
`06577101079df0a09060e0eb44b8c6eda8255f138ed3c5af2b669039567f51c5`
`072fa77729d844c920070ee8185d91d404c65892bd3ec3324473ad0155b68988`
`0e331f718ab1b3f3fab012b47f555ed2c3e14f751c833f280c0dd822cd18a1c6`
`0f074c20be427e86895db557908d85e833b1c2b1a765ea17bf9d1dcd77aa1ad1`
`0fd02c1cf5e471eccd229ab0534077e3dda91308acbaa6b4e8a15d4fc97b6b98`
`0fd57d56f1a5aa99eb20e4d15a31363292ead1d949734cc54570c9bb3fd53d03`
`0fdec37e33050abc0186bcdac49c6e677fe22dd52174846a87d5b3135fdb7028`
`10362bfd9ff8f18e62e3820f517a90a157b6fa7a546a8c8f5f6130dfdd3de88b`
`129bdda489f6349ec751d65c7ce8723941ed40d1ef1dd546371dccd597720ffc`
`15c99d9e00084189cdb2abc12a57ffdea53ea181371b7d5bef30c7e91d881f38`
`19301e15ac811ffb6bd39380ca618f5c5fb1826e4bc52f6aa6967e00d62dc634`
`1f159d6772407b57400c1d524b97415f66134673ffd8b07c0fe123addea75f90`
`1f9fc37a1c9df0e760d8efc1a8671dc50d214bf55782c091ec382e2a36acc4db`
`203edf058978544a7df0461d63dd601475f37f8dbb27b9707065344e7e6ce8be`
`21ede0344d272a3a8a772dbdaadbacff83b522fcb01728965a8f29a4726358d9`
`2808e6b2ebe3634f82b388f17e007478854ec366cb7fd09321b6ea128d3a2155`
`284e151ec6597ce6ccc0fb1848d44177bdb351ee0ad00b360014ea7ac5a31d84`
`295a3be41b49bd5eacd29948c45be6df94a787c7873c9f73779f6cc473b2d088`
`33c027dc736af58e3cf4d9bd76abbbfc6adf461e1d942db0d0f7d06b513c8c94`
`3445899a37c24d910f0f91f4a330c26054f3f0018b6c44fe619fe4887673786a`
`35752610b7219f53b5a5de2448f0a60175abe48204384ee55ac898dcb95dea66`
*See JSON for more IOCs
#### Coverage
Product| Protection
—|—
Secure Endpoint| 
Cloudlock| N/A
CWS| 
Email Security| 
Network Security| 
Stealthwatch| N/A
Stealthwatch Cloud| N/A
Secure Malware Analytics| 
Umbrella| 
WSA| 
#### Screenshots of Detection
#### Secure Endpoint
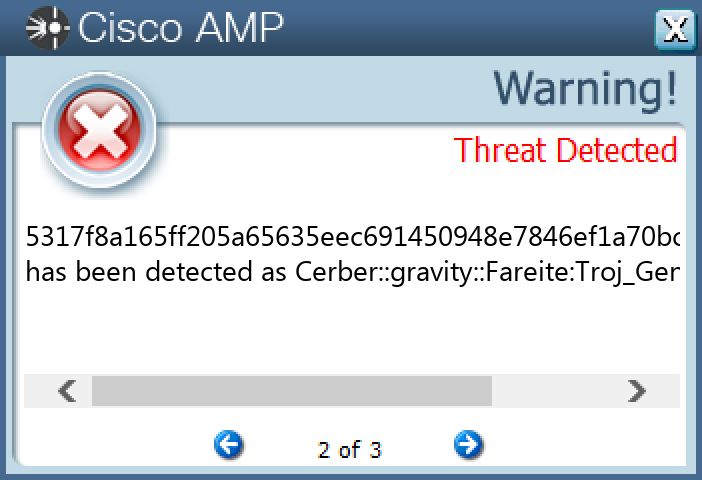
#### Secure Malware Analytics
#### MITRE ATT&CK

* * *
### Win.Trojan.DarkComet-9993855-1
#### Indicators of Compromise
* IOCs collected from dynamic analysis of 12 samples
Registry Keys| Occurrences
—|—
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONPOLICIESEXPLORERRUN`| 8
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONPOLICIESEXPLORERRUN`| 8
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONPOLICIESEXPLORERRUN
Value Name: Policies`| 6
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONPOLICIESEXPLORERRUN
Value Name: Policies`| 6
`SOFTWAREWOW6432NODEMICROSOFTACTIVE SETUPINSTALLED COMPONENTS{08B0E5JF-4FCB-11CF-AAA5-00401C6XX500}`| 3
`SOFTWAREWOW6432NODEMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: HKLM`| 3
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: HKCU`| 3
`SOFTWAREWOW6432NODEMICROSOFTACTIVE SETUPINSTALLED COMPONENTS{08B0E5JF-4FCB-11CF-AAA5-00401C6XX500}
Value Name: StubPath`| 3
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONEXPLORERTASKBAND
Value Name: FavoritesRemovedChanges`| 2
`SOFTWAREWOW6432NODEMICROSOFTACTIVE SETUPINSTALLED COMPONENTS{133O0260-G62R-WKV6-48OL-PO08NOG6SK71}`| 2
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONPOLICIESEXPLORERRUN
Value Name: explorer`| 2
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONPOLICIESEXPLORERRUN
Value Name: explorer`| 2
`SOFTWAREWOW6432NODEMICROSOFTACTIVE SETUPINSTALLED COMPONENTS{133O0260-G62R-WKV6-48OL-PO08NOG6SK71}
Value Name: StubPath`| 2
`SOFTWAREHIDDENVICTIM`| 2
`SOFTWAREHIDDENVICTIM
Value Name: FirstExecution`| 2
`SOFTWAREHIDDENVICTIM
Value Name: NewIdentification`| 2
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONPOLICIESSYSTEM
Value Name: EnableLUA`| 1
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: mstwain32`| 1
`SOFTWARESERVER
Value Name: NewIdentification`| 1
`SYSTEMCONTROLSET001SERVICESVSSDIAGVSSAPIPUBLISHER`| 1
`SOFTWARESERVER`| 1
`SOFTWAREWOW6432NODEMICROSOFTACTIVE SETUPINSTALLED COMPONENTS{CG08B0E5JF-4FCB-11CF-AAA5-00401C6XX500}`| 1
`SOFTWAREHACKED`| 1
`SOFTWAREHACKED
Value Name: NewIdentification`| 1
`SOFTWAREWOW6432NODEMICROSOFTACTIVE SETUPINSTALLED COMPONENTS{CG08B0E5JF-4FCB-11CF-AAA5-00401C6XX500}
Value Name: StubPath`| 1
Mutexes| Occurrences
—|—
`_x_X_BLOCKMOUSE_X_x_`| 8
`_x_X_PASSWORDLIST_X_x_`| 8
`_x_X_UPDATE_X_x_`| 8
`***MUTEX***`| 4
`***MUTEX***_SAIR`| 4
`***MUTEX***_PERSIST`| 2
`***SpyChuck***`| 2
`***SpyChuck***_PERSIST`| 2
`***SpyChuck***_SAIR`| 2
`ASPLOG`| 1
`DENEK`| 1
`Bif123`| 1
`CyberGate1`| 1
`646sdf456sd4af564fsdfsd`| 1
`646sdf456sd4af564fsdfsd_PERSIST`| 1
`646sdf456sd4af564fsdfsd_SAIR`| 1
IP Addresses contacted by malware. Does not indicate maliciousness| Occurrences
—|—
`204[.]95[.]99[.]142`| 1
Domain Names contacted by malware. Does not indicate maliciousness| Occurrences
—|—
`rogerioskynet[.]no-ip[.]biz`| 2
`hasn[.]no-ip[.]org`| 2
`ncn[.]dyndns[.]tv`| 1
`vacinaparaloucos[.]no-ip[.]biz`| 1
`tomjose[.]zapto[.]org`| 1
`abello1[.]no-ip[.]biz`| 1
`dx1-system[.]no-ip[.]org`| 1
Files and or directories created| Occurrences
—|—
`%TEMP%XX–XX–XX.txt`| 8
`%TEMP%UuU.uUu`| 8
`%TEMP%XxX.xXx`| 8
`%APPDATA%logs.dat`| 8
`dir`| 2
`dirinstall`| 2
`dirinstallinstall`| 2
`%SystemRoot%SysWOW64install`| 2
`%SystemRoot%SysWOW64installserver.exe`| 2
`%SystemRoot%SysWOW64system32`| 2
`%SystemRoot%SysWOW64system32system32.exe`| 2
`dirinstallinstallwindows.exe`| 2
`%APPDATA%addons.dat`| 1
`%SystemRoot%mstwain32.exe`| 1
`%SystemRoot%cmsetac.dll`| 1
`%SystemRoot%ntdtcstp.dll`| 1
`%APPDATA%install`| 1
`%SystemRoot%win32`| 1
`%APPDATA%installserver.exe`| 1
`%SystemRoot%win32server.exe`| 1
`%SystemRoot%SysWOW64Installer`| 1
`%SystemRoot%SysWOW64Installertaskmgr.exe`| 1
#### File Hashes
`142f94160c09be675fe3bf06a5fe84b3e023dce455322ec11cceee1511258921`
`36b8535bdefbea5c1cb74fcee2dda32b1456ac9df5e44aac0c107edf249693f6`
`3ac59633aa4d92f9c21862042bb1b15c39e4dd37082ee8b5bcbfedf778eb4ea8`
`3d073fe21b27a7c2db7366704cd004e76148258864ca0b10d795316c32388cfa`
`4d03acca31439bff32d232c6a18e94fa8472f36ca9ef567783269234f4bd9ac4`
`69921e80a8e832e09f70910394061439b15041a3a5034c67d34569d6f68c7254`
`737e28a69d807f7498eacbeab45fc12d076823aaa5b5a6fe37d069e896d59caa`
`842ea6781e660a24d0cb03a1dee05244214f2f05f5f301f7f4d3f2dda2679f20`
`85cdce0feb238fb93d2fa90e4e58ac1d590915dbc49e83bf0d749b7f4a1e726c`
`9078c43f5035ac673c127949d8a3701259adf61d682cd0f77c2b8c353dfab463`
`ddf5296ee0edec8fa1fd6bbd5d5403fdc23a56c47a58690ec71c13f1cc3ef602`
`ee6ddc525cea2008b299981528f4b73962cc98e09362fae560ed77ed490e6186`
#### Coverage
Product| Protection
—|—
Secure Endpoint| 
Cloudlock| N/A
CWS| 
Email Security| 
Network Security| 
Stealthwatch| N/A
Stealthwatch Cloud| N/A
Secure Malware Analytics| 
Umbrella| N/A
WSA| N/A
#### Screenshots of Detection
#### Secure Endpoint
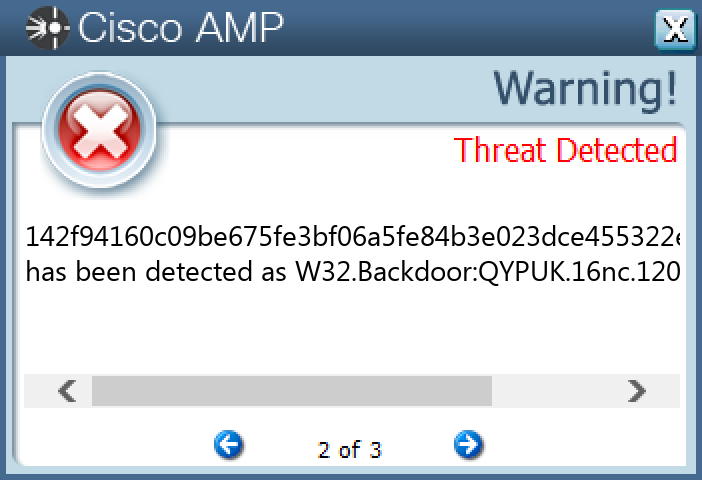
#### Secure Malware Analytics
#### MITRE ATT&CK
* * *
### Win.Packed.Zusy-9993358-0
#### Indicators of Compromise
* IOCs collected from dynamic analysis of 15 samples
Registry Keys| Occurrences
—|—
`SOFTWARELOCAL APPWIZARD-GENERATED APPLICATIONS`| 15
`SOFTWARELOCAL APPWIZARD-GENERATED APPLICATIONSCDB`| 15
`SOFTWARELOCAL APPWIZARD-GENERATED APPLICATIONSCDBRECENT FILE LIST`| 15
`SOFTWARELOCAL APPWIZARD-GENERATED APPLICATIONSCDBSETTINGS`| 15
`SOFTWAREMICROSOFTWINDOWS NTCURRENTVERSIONSCHEDULETASKCACHETREE
Value Name: Index`| 1
`SOFTWAREMICROSOFTWINDOWS NTCURRENTVERSIONSCHEDULETASKCACHETREE
Value Name: Id`| 1
Mutexes| Occurrences
—|—
`GLOBAL{}`| 15
IP Addresses contacted by malware. Does not indicate maliciousness| Occurrences
—|—
`122[.]117[.]90[.]133`| 14
`210[.]2[.]149[.]202`| 12
`36[.]91[.]117[.]231`| 10
`36[.]95[.]23[.]89`| 10
`202[.]9[.]121[.]143`| 9
`110[.]172[.]137[.]20`| 9
`103[.]123[.]86[.]104`| 8
`103[.]75[.]32[.]173`| 7
`36[.]89[.]228[.]201`| 7
`45[.]115[.]172[.]105`| 7
`103[.]146[.]232[.]154`| 7
`36[.]91[.]88[.]164`| 6
`117[.]222[.]61[.]115`| 6
`58[.]97[.]72[.]83`| 6
`139[.]255[.]65[.]170`| 5
`202[.]65[.]119[.]162`| 5
`118[.]91[.]190[.]42`| 5
`117[.]222[.]57[.]92`| 5
`103[.]9[.]188[.]78`| 4
`103[.]47[.]170[.]130/31`| 4
`139[.]255[.]6[.]2`| 1
`36[.]91[.]186[.]235`| 1
`103[.]194[.]88[.]4`| 1
Files and or directories created| Occurrences
—|—
`%System32%TasksBrowser Lite Tools for WindowsM2WS`| 1
`%System32%TasksBrowser Lite Tools for WindowsJNFF`| 1
`%System32%TasksBrowser Lite Tools for WindowsD9HP`| 1
`%System32%TasksBrowser Lite Tools for WindowsZRRZ`| 1
`%System32%TasksBrowser Lite Tools for WindowsS6KQ`| 1
`%System32%TasksBrowser Lite Tools for WindowsXXD9`| 1
`%System32%TasksBrowser Lite Tools for WindowsNJ73`| 1
`%System32%TasksBrowser Lite Tools for WindowsLD19`| 1
`%System32%TasksBrowser Lite Tools for WindowsI4MO`| 1
`%System32%TasksBrowser Lite Tools for WindowsHTD1`| 1
`%System32%TasksBrowser Lite Tools for WindowsY6OA`| 1
`%System32%TasksBrowser Lite Tools for WindowsK4QY`| 1
`%System32%TasksBrowser Lite Tools for WindowsCAAK`| 1
`%System32%TasksBrowser Lite Tools for Windows1PXP`| 1
#### File Hashes
`1087adf31edf1f9a8ab19b6053072366d495f191c187eda56a0c94c79d4d7d3c`
`2c88abd04b18282dc60484bbee15574dc3816cfbfcb3a4f0299ff92d41da9120`
`39d7cab782004e79f16f695e96fc996e95a0f9e6a1ec37b391c091dc01f7eea2`
`482f66d7a734f9cee31de1ee7a74dc2286fb493fee080040dda43ad6b15bff2e`
`582f066cc3904e23a604829b004a3b1602b86947a4c1b5752dd62e4b5b264357`
`669bddcbb2a4ccce13365b6a664517cc5c6fc149ad2cf1fbc936c2ec82916bf6`
`9d8a148b40e15d1a374ec81fb4aad1e09c8fc7cfee33c2141cae6b47c0b70983`
`a844f4b4cd3aa66b10306bfa01209bcb519d19d7e87b219669a9be984935528b`
`ab4baa4103f7a5efe79a644977e40901d35ca7b4a166e5912a1de4ec3b34ba8a`
`ac387553d29a6cc41f7c702e80ba8aa3ce0f18cfb15522da52e10dc45c3134ee`
`afcd87ae0ca9a66f107d89ae0abecff5cf23b36685d7a13a3ed815b109c5e006`
`bf5401e25df5fcc0d5a05c64cef5e391692f28c3b290edd23c9487ba77e7204a`
`e1cc4cf92cb5d5a4a803f4ee1f29e4298998e3639e64ebe96accc9d15ae5d226`
`e326eebba8ca1bdf084fb18157d56ab250ce10ddd58508264fb5443dbdfbbe61`
`f1f1a6424de9cc0e4c9b3770e785a1e544c46bb6f4c7be61108f0b6276d8e140`
#### Coverage
Product| Protection
—|—
Secure Endpoint| 
Cloudlock| N/A
CWS| 
Email Security| 
Network Security| 
Stealthwatch| N/A
Stealthwatch Cloud| N/A
Secure Malware Analytics| 
Umbrella| N/A
WSA| N/A
#### Screenshots of Detection
#### Secure Endpoint
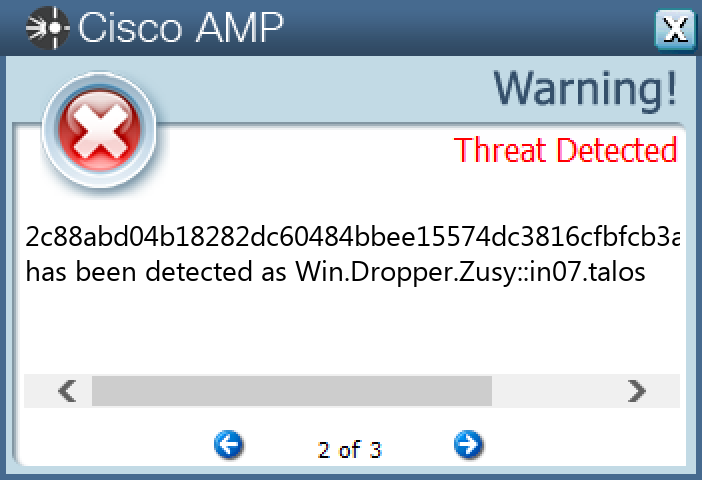
#### Secure Malware Analytics
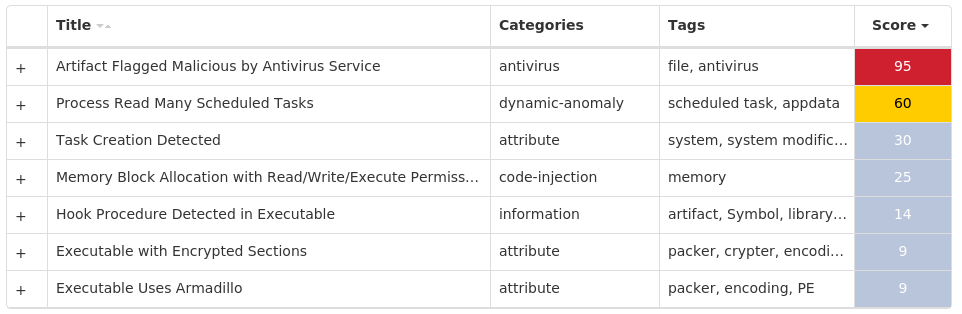
#### MITRE ATT&CK

* * *
### Win.Packed.Upatre-9993687-0
#### Indicators of Compromise
* IOCs collected from dynamic analysis of 18 samples
IP Addresses contacted by malware. Does not indicate maliciousness| Occurrences
—|—
`207[.]148[.]248[.]143`| 18
Domain Names contacted by malware. Does not indicate maliciousness| Occurrences
—|—
`aatextiles[.]com`| 18
Files and or directories created| Occurrences
—|—
`%TEMP%budha.exe`| 18
#### File Hashes
`0e25453d0e0055690295e27bf06f8576978a7f723ae1fb94d9dcf211a690ed6b`
`16008473272fbf4065bbc9601c67c54445c27241c38b60aa2bad8bb045e8e65e`
`1a29c62f02b5c636c507f6cdc36a81b5188a4a598ffb339cfa092288c3e6a781`
`3001f5ac516c69a8668e3fb1f1f8894d2cf9b1388f33989335f82cb99ffb2f20`
`3016f39b5da400f546881ba5628db1d570f2cc2c0064bf14773fd267102688bc`
`5dc9a3c8cc080070ffc4f21348093020641806b7aeb4dd11e2d28d51358df3d2`
`74f32dcfaa51e61fb520641c893c4e28237859be347af74d326f0a4b15d50c2d`
`7855251519672468876b60b8c35541a992cb5767b148d8f2079a499701d76512`
`7879400b65d6df96d0aa9c00ec3c7dd1dcfbc83841dc34cb175db4fea2c1bb20`
`7e60bc0d3894082f8c7d634761083c1c3c9b3293670877f716d5aaa0c9d0985b`
`7fca81eba218f66884c7bb0373a5c6e8f1b6495c7aa67928d9c8e7657f878b24`
`a73bab9b6dc013f658d6697a19f1d05c4f32b57753a3852290561f034839580a`
`b31ee4a8ac5fbe56665c674033747599f48d32fc054cae2b0161adf9e7314f5a`
`cbb5a2f33ed4be9210208ec4c81ae64e2a7d0d97c1264af1e232359db8354caf`
`d3a6f9e579a0dc46883c85abedae67503b3bc1d41459c558769ab093449998df`
`e75775da8316b3ee239cb01583c15383234d77ff1324b26c84e30b144f674ae6`
`ef738e5f133b99f03a35dd442fee4fa77d6f902726e496e5e9ab54830b8e62a0`
`fcf5c338d09cf3a4f31cee0040a5f9d7b81cc222b0bdfe1dfd573423a4c1a053`
#### Coverage
Product| Protection
—|—
Secure Endpoint| 
Cloudlock| N/A
CWS| 
Email Security| 
Network Security| 
Stealthwatch| N/A
Stealthwatch Cloud| N/A
Secure Malware Analytics| 
Umbrella| N/A
WSA| N/A
#### Screenshots of Detection
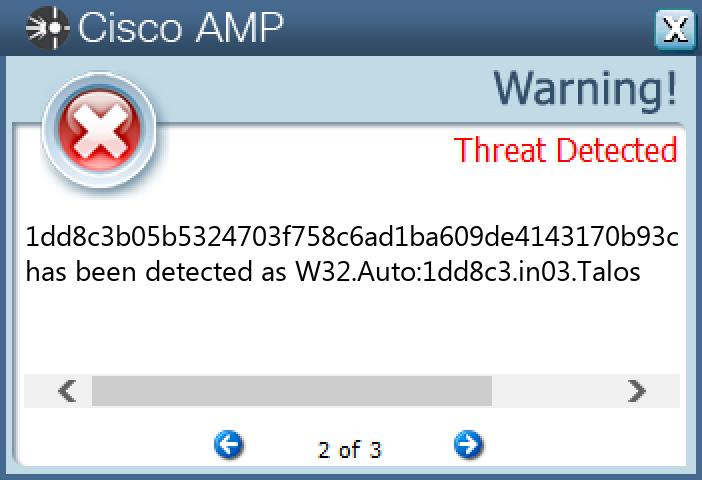
#### Secure Endpoint
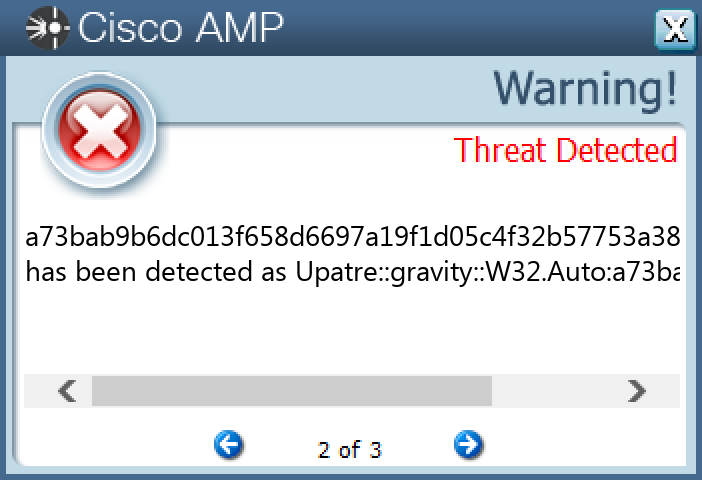
#### Secure Malware Analytics
#### MITRE ATT&CK

* * *
### Win.Dropper.LokiBot-9993959-0
#### Indicators of Compromise
* IOCs collected from dynamic analysis of 46 samples
Registry Keys| Occurrences
—|—
`SOFTWAREPOLICIESMICROSOFTWINDOWS DEFENDER
Value Name: DisableAntiSpyware`| 45
`SYSTEMCONTROLSET001SERVICESWINDEFEND
Value Name: Start`| 45
`SOFTWAREWOW6432NODEMICROSOFTWINDOWSCURRENTVERSIONRUNONCE
Value Name: wextract_cleanup0`| 45
`SOFTWAREPOLICIESMICROSOFTWINDOWSWINDOWSUPDATEAU`| 45
`SOFTWAREPOLICIESMICROSOFTWINDOWSWINDOWSUPDATEAU
Value Name: NoAutoRebootWithLoggedOnUsers`| 45
`SYSTEMCONTROLSET001SERVICESWUAUSERV
Value Name: Start`| 45
`SOFTWAREPOLICIESMICROSOFTWINDOWSWINDOWSUPDATEAU
Value Name: NoAutoUpdate`| 45
`SOFTWAREPOLICIESMICROSOFTWINDOWS DEFENDERREAL-TIME PROTECTION
Value Name: DisableBehaviorMonitoring`| 45
`SOFTWAREPOLICIESMICROSOFTWINDOWS DEFENDERREAL-TIME PROTECTION
Value Name: DisableOnAccessProtection`| 45
`SOFTWAREPOLICIESMICROSOFTWINDOWS DEFENDERREAL-TIME PROTECTION
Value Name: DisableScanOnRealtimeEnable`| 45
`SOFTWAREWOW6432NODEMICROSOFTWINDOWSCURRENTVERSIONRUNONCE
Value Name: wextract_cleanup1`| 45
`SOFTWAREWOW6432NODEMICROSOFTWINDOWSCURRENTVERSIONRUNONCE
Value Name: wextract_cleanup2`| 45
`SOFTWAREWOW6432NODEMICROSOFTWINDOWSCURRENTVERSIONRUNONCE
Value Name: wextract_cleanup3`| 45
`SOFTWAREPOLICIESMICROSOFTWINDOWS DEFENDERREAL-TIME PROTECTION
Value Name: DisableIOAVProtection`| 45
`SOFTWAREPOLICIESMICROSOFTWINDOWS DEFENDER`| 45
`SOFTWAREPOLICIESMICROSOFTWINDOWS DEFENDERREAL-TIME PROTECTION`| 45
`SOFTWAREPOLICIESMICROSOFTWINDOWSWINDOWSUPDATE`| 45
`SOFTWAREWOW6432NODEMICROSOFTWINDOWS DEFENDERFEATURES`| 45
`SOFTWAREWOW6432NODEMICROSOFTWINDOWS DEFENDERFEATURES
Value Name: TamperProtection`| 45
`SOFTWAREPOLICIESMICROSOFTWINDOWS DEFENDERREAL-TIME PROTECTION
Value Name: DisableRealtimeMonitoring`| 45
`SOFTWAREPOLICIESMICROSOFTWINDOWS DEFENDER SECURITY CENTER`| 45
`SOFTWAREPOLICIESMICROSOFTWINDOWSWINDOWSUPDATEAU
Value Name: AUOptions`| 45
`SOFTWAREPOLICIESMICROSOFTWINDOWSWINDOWSUPDATEAU
Value Name: AutoInstallMinorUpdates`| 45
`SOFTWAREPOLICIESMICROSOFTWINDOWS DEFENDER SECURITY CENTERNOTIFICATIONS`| 45
`SOFTWAREPOLICIESMICROSOFTWINDOWS DEFENDER SECURITY CENTERNOTIFICATIONS
Value Name: DisableNotifications`| 45
Mutexes| Occurrences
—|—
`006700e5a2ab05704bbb0c589b88924d`| 45
IP Addresses contacted by malware. Does not indicate maliciousness| Occurrences
—|—
`31[.]41[.]244[.]200`| 45
`193[.]233[.]20[.]30`| 45
Files and or directories created| Occurrences
—|—
`%TEMP%IXP001.TMP`| 45
`%TEMP%IXP001.TMPTMP4351$.TMP`| 45
`%TEMP%IXP002.TMP`| 45
`%TEMP%IXP002.TMPTMP4351$.TMP`| 45
`%TEMP%IXP003.TMP`| 45
`%TEMP%IXP003.TMPTMP4351$.TMP`| 45
`%LOCALAPPDATA%Yandex`| 45
`%LOCALAPPDATA%YandexYaAddon`| 45
`%TEMP%5975271bda`| 45
`%TEMP%5975271bdametafor.exe`| 45
`%System32%Tasksmetafor.exe`| 45
`%TEMP%IXP001.TMPen467862.exe`| 45
`%TEMP%IXP001.TMPkino4251.exe`| 45
`%TEMP%IXP002.TMPdAE02s16.exe`| 45
`%TEMP%IXP002.TMPkino2751.exe`| 45
`%TEMP%IXP003.TMPbus7719.exe`| 45
`%TEMP%IXP003.TMPcon6935.exe`| 45
`%TEMP%IXP000.TMPge023694.exe`| 45
`%TEMP%IXP000.TMPkino6903.exe`| 45
`%TEMP%1000005051`| 1
`%TEMP%1000005051foto0162.exe`| 1
`%TEMP%IXP000.TMPsi449430.exe`| 1
`%TEMP%IXP000.TMPunio6664.exe`| 1
`%TEMP%IXP001.TMPrgE97s18.exe`| 1
`%TEMP%IXP001.TMPunio2273.exe`| 1
*See JSON for more IOCs
#### File Hashes
`00a41c3cdaa424eeb6319db533ba421d00deef10194ec3ed41baaff069abfbc6`
`08129aba55d0282cf9bddbbd2b04499e972e321bec4477110a3df8ba5e26731a`
`09ab7483ce488bc6cf7be401bf1246cf59cde5bc4ebe81d3aebb43ff2cd85398`
`09c60f53c40df2a7318c619692756096a1a4a5c485f14e033aae08dcd653df22`
`0ddd516729c268faf26249955752d44054a9b574bb4b7c98a734ec4c35513f7c`
`189fb3451b47f12e1fa298faf29a657bcf1451b9eecf8894e390a9b49bf065a7`
`1bda936bb3a63072cd7ec02d904d5797e604d892e448ae92745c0b99bcb920ca`
`1d1f6ee67baf7713754ef87f61397cbc50201d2163c893fc48ef17fd5490f041`
`1dd8c3b05b5324703f758c6ad1ba609de4143170b93c1eefc20c14545bd44b08`
`23ee90260a961a345f216fa590850992a50af61aa6a8e8934d23fc4c44529634`
`2558cf38481549c9fdd11d2b3fde4b0168c8d7fb7726dd8f588e60e22794ac6b`
`3970c7b91720a57f356bc895c164f92e776f8e946ff1b059ea0b210b260c256c`
`3badfd1548575cffa198d8be072123c415b9a8ec0f5e88338a9dc0b49259fa1c`
`45cfd7b084155ba74c37f46ef6c7932e736ab50979b5a904cd0521c8ef894e28`
`4dc866260dab99e966d7c6b6bb95f687349109366aa42bd605bc75d4b9e47719`
`54ab28a4fea3aab1315aa73ac2a1b89ce71761878e7c7a8392bf6f95f3d0e775`
`66293653ca713a861eb03ca30166d83f848795a08d0f3cbc552753dd06a4f49c`
`82d3a9e6afd813acc280c1ed2b49d268528aca6d9b0ccba3933f1c734600dd16`
`879914057bce3a36fc6736cfdcf0492b622ed5eeb3a2e930f9cda48d1c6157fd`
`8897996ae1cd40ab8ba2edb577e5845a65b3fe0c6efe90f3c27ee920ad591c2c`
`9a7075f81112630b9569f5463293a6a96a7d0624d47e5bf786cff0d479ce50dd`
`9b86d3eceda1e624e9881973daec758e29304f0f6fefd5c5debaf62200462545`
`9cb370cedb049039b08ef47c226518ff3881bc8309c89b57e25dc042169ab96a`
`a1974279f06f9e589582df17a106e0830baa549780f65ece88488acb535d0179`
`a3d578e74702ef75d093a8889312c107c4d13dda49e2b5a3691889fbe2974b37`
*See JSON for more IOCs
#### Coverage
Product| Protection
—|—
Secure Endpoint| 
Cloudlock| N/A
CWS| 
Email Security| 
Network Security| 
Stealthwatch| N/A
Stealthwatch Cloud| N/A
Secure Malware Analytics| 
Umbrella| N/A
WSA| N/A
#### Screenshots of Detection
#### Secure Endpoint
#### Secure Malware Analytics
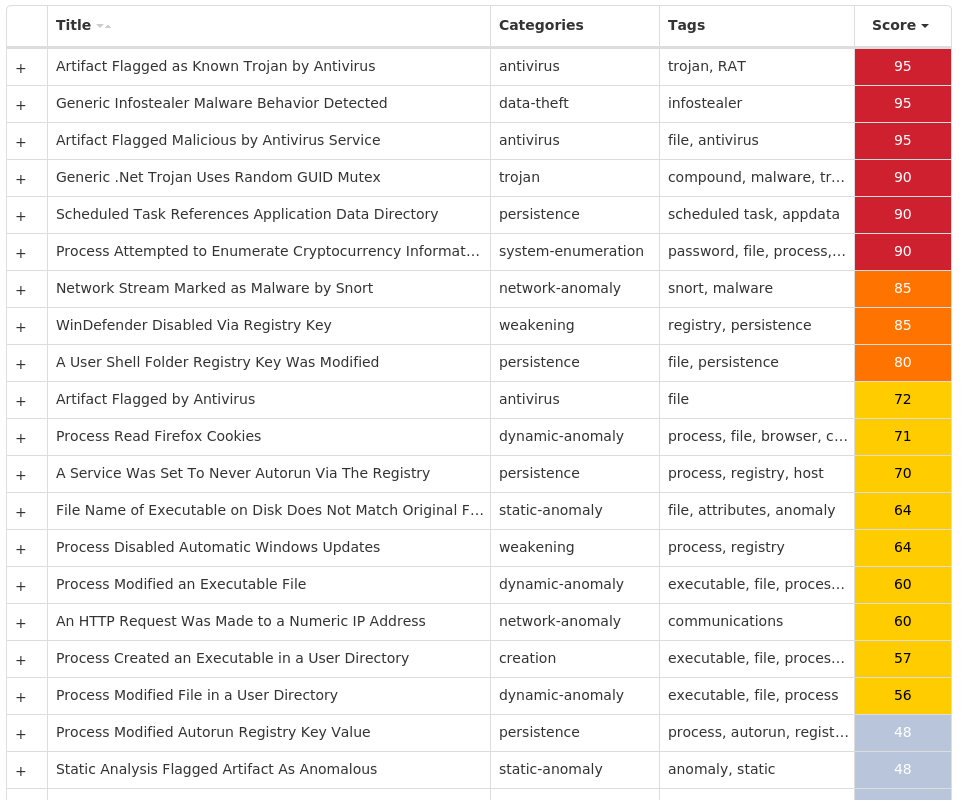
#### MITRE ATT&CK
* * *
### Win.Virus.Ramnit-9993699-0
#### Indicators of Compromise
* IOCs collected from dynamic analysis of 25 samples
Registry Keys| Occurrences
—|—
`SOFTWAREWOW6432NODEMICROSOFTSECURITY CENTER
Value Name: AntiVirusOverride`| 25
`SOFTWAREWOW6432NODEMICROSOFTSECURITY CENTER
Value Name: AntiVirusDisableNotify`| 25
`SOFTWAREWOW6432NODEMICROSOFTSECURITY CENTER
Value Name: FirewallDisableNotify`| 25
`SOFTWAREWOW6432NODEMICROSOFTSECURITY CENTER
Value Name: FirewallOverride`| 25
`SOFTWAREWOW6432NODEMICROSOFTSECURITY CENTER
Value Name: UpdatesDisableNotify`| 25
`SOFTWAREWOW6432NODEMICROSOFTSECURITY CENTER
Value Name: UacDisableNotify`| 25
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONPOLICIESSYSTEM
Value Name: EnableLUA`| 25
`SYSTEMCONTROLSET001SERVICESSHAREDACCESSPARAMETERSFIREWALLPOLICYSTANDARDPROFILE
Value Name: EnableFirewall`| 25
`SYSTEMCONTROLSET001SERVICESSHAREDACCESSPARAMETERSFIREWALLPOLICYSTANDARDPROFILE
Value Name: DoNotAllowExceptions`| 25
`SYSTEMCONTROLSET001SERVICESSHAREDACCESSPARAMETERSFIREWALLPOLICYSTANDARDPROFILE
Value Name: DisableNotifications`| 25
`SYSTEMCONTROLSET001SERVICESWSCSVC
Value Name: Start`| 25
`SYSTEMCONTROLSET001SERVICESWINDEFEND
Value Name: Start`| 25
`SYSTEMCONTROLSET001SERVICESMPSSVC
Value Name: Start`| 25
`SOFTWAREWOW6432NODEMICROSOFTWINDOWS NTCURRENTVERSION
Value Name: jfghdug_ooetvtgk`| 25
`SOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: JudCsgdy`| 25
`SYSTEMCONTROLSET001SERVICESWUAUSERV
Value Name: Start`| 25
`SOFTWAREWOW6432NODEMICROSOFTWINDOWSCURRENTVERSIONRUN
Value Name: Windows Defender`| 25
`SOFTWAREMICROSOFTWINDOWS NTCURRENTVERSIONWINLOGON
Value Name: Userinit`| 25
`SOFTWAREWOW6432NODEMICROSOFTWINDOWS NTCURRENTVERSIONWINLOGON
Value Name: Userinit`| 25
Mutexes| Occurrences
—|—
`{7930D12C-1D38-EB63-89CF-4C8161B79ED4}`| 25
`{79345B6A-421F-2958-EA08-07396ADB9E27}`| 25
IP Addresses contacted by malware. Does not indicate maliciousness| Occurrences
—|—
`142[.]251[.]35[.]174`| 23
`46[.]165[.]254[.]201`| 22
`72[.]26[.]218[.]70`| 22
`195[.]201[.]179[.]207`| 22
`208[.]100[.]26[.]245`| 22
`206[.]191[.]152[.]58`| 22
`72[.]251[.]233[.]245`| 22
`64[.]225[.]91[.]73`| 22
Domain Names contacted by malware. Does not indicate maliciousness| Occurrences
—|—
`google[.]com`| 23
`testetst[.]ru`| 23
`iihsmkek[.]com`| 22
`mtsoexdphaqliva[.]com`| 22
`uulwwmawqjujuuprpp[.]com`| 22
`twuybywnrlqcf[.]com`| 22
`wcqqjiixqutt[.]com`| 22
`ubgjsqkad[.]com`| 22
`tlmmcvqvearpxq[.]com`| 22
`flkheyxtcedehipox[.]com`| 22
`edirhtuawurxlobk[.]com`| 22
`tfjcwlxcjoviuvtr[.]com`| 22
Files and or directories created| Occurrences
—|—
`%LOCALAPPDATA%bolpidti`| 25
`%LOCALAPPDATA%bolpidtijudcsgdy.exe`| 25
`%APPDATA%MicrosoftWindowsStart MenuProgramsStartupjudcsgdy.exe`| 25
`TEMPwV6jD23`| 25
#### File Hashes
`0edef9c023045ca327cbdc4afcb26a729e863a406ededeea620a5156161bd65b`
`246f6b0f79d75adae9cd20b4be32421c3876d8d5c190710647b0f8487fde16d6`
`250fde02ed82039d271893fb9c57c21566e1306885ffa0ab9ef1d76b8e637450`
`4460c8d695928d9791c2c56caa4f4d7f4e89b2f5f79f6cfd3f4104513c7b0caf`
`4a3ea8cc597c3dc0f78ac61c7cb05cdf3b6f4fc583a041611eafa10ad48775e7`
`5148c0ea49147b1ad5b61fdb21690b36a8df66cd887c5f7a5860593e9cd33da6`
`5bcdb4fef1ef0db979cc431233e8ee60df86ff9a58dccb130b6cb14deaf20165`
`5d4fafce265952687dc0457c9371e608ad495dcf34f9197dd111814fc0c12f16`
`6025eb9ff332381ae1b18ce3fabe0604f01fe42b313ea8ac0525dd92f368330f`
`6f7100b0a2575c3f4c6830642168a8dd9dfc779c5adb58959958bad267e1d2c6`
`708f61e53aff6e67f8cb80e4267d4030ef0744dc5517a979d5ac4ca098a0c271`
`748fadc2257b32a766624b33448b2c665f627ab4783e5364f8b6de9be6fb4595`
`76b0732dbca956b771375e08286e64791b5151951df75c3333d330c3fc64b5ad`
`892e127dea47acb58bdcf6dcbba6d1c0825578e17eda71aeca70753ca1392d87`
`978ee0b56f6aa31b0f09a1558c9712d187910e7f88e6b1cccaf91c6353fc951b`
`a30850408cd40360a1d146dd6523e3abe9eb077076f00030d6f4cb854144300e`
`a9e66a3df0d91547902987d153025a1db11c40eb69ab34941ceba3e69edff825`
`cb06c7223d2180727a5367df89303aa6477ab7dab6c0fd8e8a1fe64da2eae4d3`
`d2ab5a17cb955c177a73f6dee869140bf30ae2c6211bf22e62d4bd3069f87fef`
`d73d7848785595c34dea1a57ddaf4c83bdcd17e1deae76750856454215e9e369`
`e1efa5a4e2d6e7b4dd1bb810b702de584a27cecadc6ee3d9c52bf602837536cd`
`e23251582f9c3bff3b9e08303b9715c004db7235ca09c6888fe7673acba251f7`
`e94a7c984848c929bafaba780216e6f83ea4e02641f7feecbf3e08792882e20d`
`f6b24b4f953a12a464c11c8c6eea113c7da1d447ed9a9c39754d26bb1de15f6b`
`ff8f64ba99905d7afb1bc98ec5dc64611bb73d508c8f6c40c26e30d2a61306b1`
#### Coverage
Product| Protection
—|—
Secure Endpoint| 
Cloudlock| N/A
CWS| 
Email Security| 
Network Security| 
Stealthwatch| N/A
Stealthwatch Cloud| N/A
Secure Malware Analytics| 
Umbrella| 
WSA| 
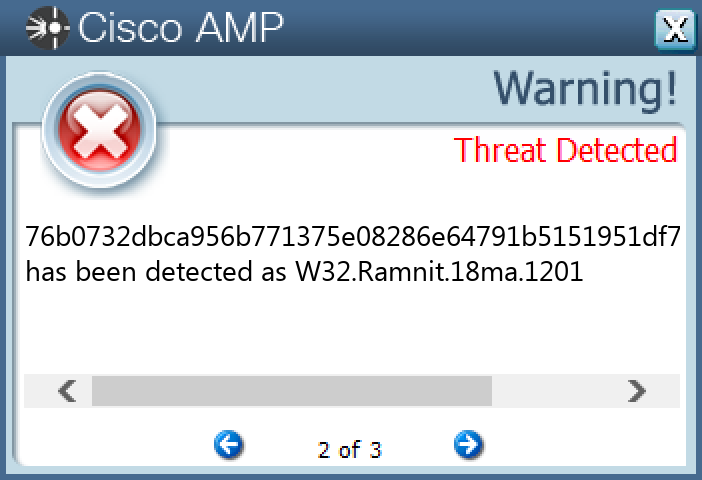
#### Screenshots of Detection
#### Secure Endpoint
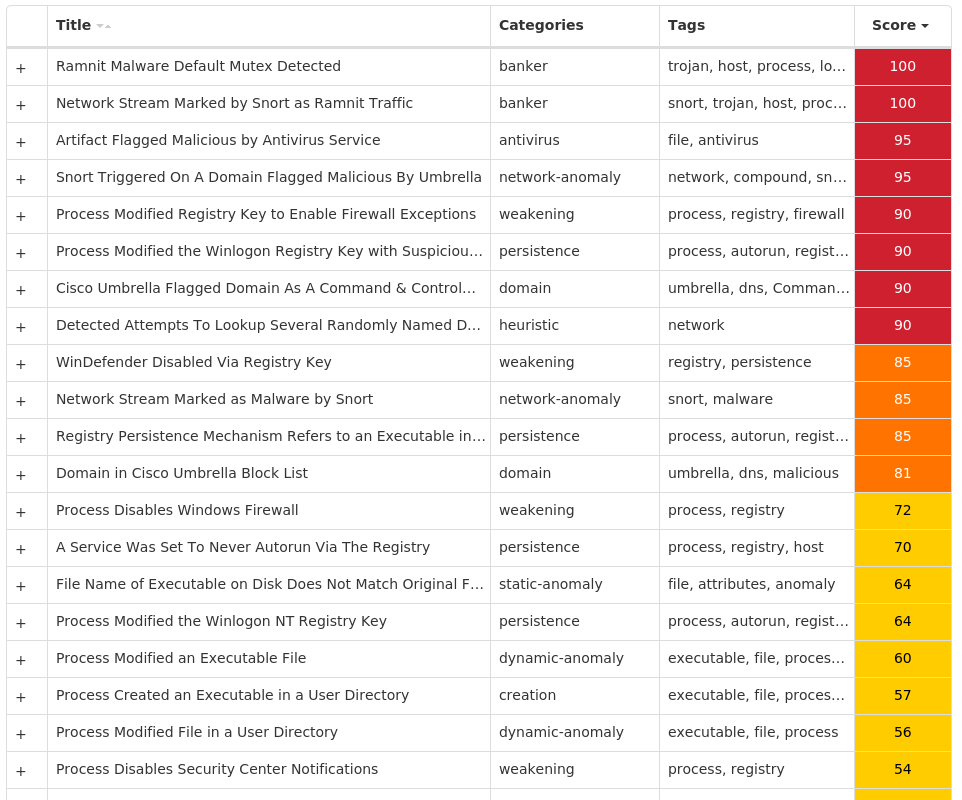
#### Secure Malware Analytics
#### MITRE ATT&CK
* * *Read More

