[]()
CloudFox helps you gain situational awareness in unfamiliar cloud environments. Its an open source [command line]( “command line” ) tool created to help penetration testers and other offensive security professionals find exploitable attack paths in cloud infrastructure.
#### CloudFox helps you answer the following common questions (and many more):
* What regions is this AWS account using and roughly how many resources are in the account?
* What secrets are lurking in EC2 userdata or service specific environment variables?
* What actions/permissions does this [principal] have?
* What roles trusts are overly permissive or allow cross-account assumption?
* What endpoints/hostnames/IPs can I attack from an external starting point (public internet)?
* What endpoints/hostnames/IPs can I attack from an internal starting point (assumed breach within the VPC)?
* What filesystems can I potentially mount from a compromised resource inside the VPC?
## Quick Start
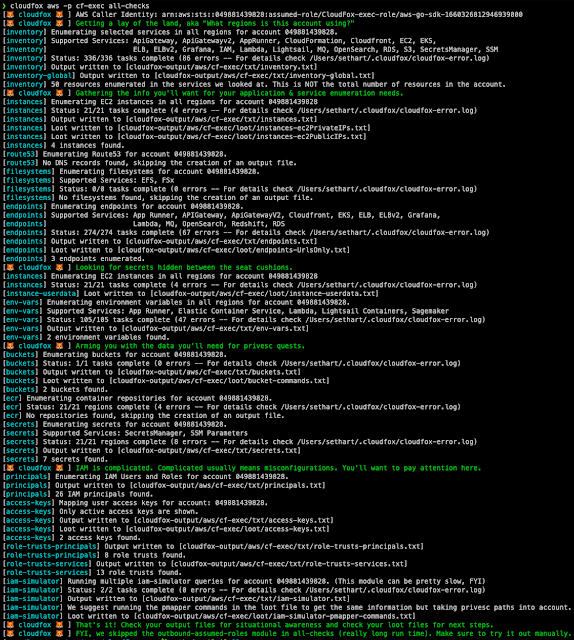
CloudFox is modular (you can run one command at a time), but there is an aws `all-checks` command that will run the other aws commands for you with sane defaults:
`cloudfox aws –profile [profile-name] all-checks`
[]( “Automating situational awareness for cloud penetration tests. (2)” )[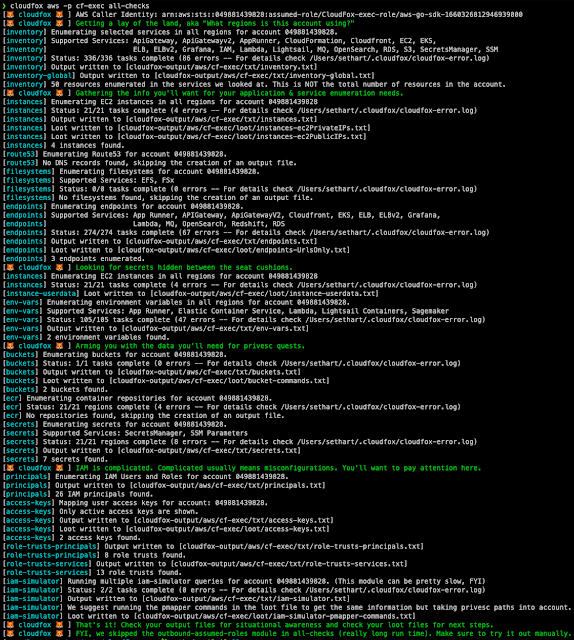]()
CloudFox is designed to be executed by a principal with limited read-only permissions, but it’s purpose is to help you find attack paths that can be exploited in simulated compromise scenarios (aka, objective based penetration testing).
For the full documentation please refer to our [wiki]( “wiki” ).
## Supported Cloud Providers
Provider | CloudFox Commands
—|—
AWS | 15
Azure | 2 (alpha)
GCP | Support Planned
Kubernetes | Support Planned
# Install
**Option 1:** Download the [latest binary release]( “latest binary release” ) for your platform.
**Option 2:** [Install Go]( “Install Go” ), clone the CloudFox repository and compile from source
# git clone https://github.com/BishopFox/cloudfox.git
…omitted for brevity…
# cd ./cloudfox
# go build .
# ./cloudfox
# Prerequisites
### AWS
* AWS CLI installed
* Supports AWS profiles, AWS environment variables, or metadata retrieval (on an ec2 instance)
* A principal with one recommended policies attached (described below)
* Recommended attached policies: **`SecurityAudit` + [CloudFox custom policy]( “CloudFox custom policy” )**
Additional policy notes (as of 09/2022):
Policy | Notes
—|—
[CloudFox custom policy]( “CloudFox custom policy” ) | Has a complete list of every permission cloudfox uses and nothing else
`arn:aws:iam::aws:policy/SecurityAudit` | Covers most cloudfox checks but is missing newer services or permissions like apprunner:*, grafana:*, lambda:GetFunctionURL, lightsail:GetContainerServices
`arn:aws:iam::aws:policy/job-function/ViewOnlyAccess` | Covers most cloudfox checks but is missing newer services or permissions like AppRunner:*, grafana:*, lambda:GetFunctionURL, lightsail:GetContainerServices – and is also missing iam:SimulatePrincipalPolicy.
`arn:aws:iam::aws:policy/ReadOnlyAccess` | Only missing AppRunner, but also grants things like “s3:Get*” which can be overly permissive.
`arn:aws:iam::aws:policy/AdministratorAccess` | This will work just fine with CloudFox, but if you were handed this level of access as a penetration tester, that should probably be a finding in itself 🙂
### Azure
* Viewer or similar permissions applied.
# Supported Commands
Provider | Command Name | Description
—|—|—
AWS | [all-checks]() | Run all of the other commands using reasonable defaults. You’ll still want to check out the non-default options of each command, but this is a great place to start.
AWS | [access-keys]() | Lists active access keys for all users. Useful for cross referencing a key you found with which in-scope account it belongs to.
AWS | [buckets]() | Lists the buckets in the account and gives you handy commands for inspecting them further.
AWS | [ecr]() | List the most recently pushed image URI from all repositories. Use the loot file to pull selected images down with docker/nerdctl for inspection.
AWS | [endpoints]() | Enumerates endpoints from various services. Scan these endpoints from both an internal and external position to look for things that don’t require authentication, are misconfigured, etc.
AWS | [env-vars]() | Grabs the environment variables from services that have them (App Runner, ECS, Lambda, Lightsail containers, Sagemaker are supported. If you find a sensitive secret, use `cloudfox iam-simulator` AND `pmapper` to see who has access to them.
AWS | [filesystems]() | Enumerate the EFS and FSx filesystems that you might be able to mount without creds (if you have the right network access). For example, this is useful when you have `ec:RunInstance` but not `iam:PassRole`.
AWS | [iam-simulator]() | Like pmapper, but uses the IAM policy simulator. It uses AWS’s evaluation logic, but notably, it doesn’t consider transitive access via privesc, which is why you should also always also use pmapper.
AWS | [instances]() | Enumerates useful information for EC2 Instances in all regions like name, public/private IPs, and instance profiles. Generates loot files you can feed to nmap and other tools for service enumeration.
AWS | [inventory]() | Gain a rough understanding of size of the account and preferred regions.
AWS | [outbound-assumed-roles]() | List the roles that have been assumed by principals in this account. This is an excellent way to find outbound attack paths that lead into other accounts.
AWS | [permissions]() | Enumerates IAM permissions associated with all users and roles. Grep this output to figure out what permissions a particular principal has rather than logging into the AWS console and painstakingly expanding each policy attached to the principal you are investigating.
AWS | [principals]() | Enumerates IAM users and Roles so you have the data at your fingertips.
AWS | [role-trusts]() | Enumerates IAM role trust policies so you can look for overly permissive role trusts or find roles that trust a specific service.
AWS | [route53]() | Enumerate all records from all route53 managed zones. Use this for application and service enumeration.
AWS | [secrets]() | List secrets from SecretsManager and SSM. Look for interesting secrets in the list and then see who has access to them using use `cloudfox iam-simulator` and/or `pmapper`.
Azure | [instances-map]() | Enumerates useful information for Compute instances in all available resource groups and subscriptions
Azure | [rbac-map]() | Enumerates Role Assignments for all tenants
# []()
# Authors
* [Carlos Vendramini]()
* [Seth Art (@sethsec]())
# []()
# Contributing
[Wiki – How to Contribute]()
# []()
# TODO
* AWS – Add support for GovCloud and China regions
* AWS – Add support for hardcoded region (which would override the default of looking in every region)
# []()
# FAQ
**How does CloudFox compare with ScoutSuite, Prowler, Steampipe’s AWS Compliance Module, AWS Security Hub, etc.**
CloudFox doesn’t create any alerts or findings, and doesn’t check your environment for compliance to a baseline or benchmark. Instead, it simply enables you to be more efficient during your manual penetration testing activities. If gives you the information you’ll likely need to validate whether an attack path is possible or not.
**Why do I see errors in some CloudFox commands?**
* Services that don’t exist in all regions – CloudFox currently makes the same API calls to every region. However, not all regions support all services. For instance, services like Appstream and AWS Grafana are only supported in a subset of the total regions. In the future, we plan to make CloudFox aware of which services run in each region.
* You don’t have permission – Another reason you might see errors if you don’t have permissions to make calls that CloudFox is making. Either because the policy doesn’t allow it (e.g., SecurityAudit doesn’t allow all of the permissions CloudFox needs. Or, it might be an SCP that is blocking you.
You can always look in the ~/.cloudfox/cloudfox-error.log file to get more information on errors.
# []()
# Prior work and other related projects
* [SmogCloud]() – Inspiration for the `endpoints` command
* [SummitRoute’s AWS Exposable Resources]() – Inspiration for the `endpoints` command
* [Steampipe]() – We used steampipe to prototype many cloudfox commands. While CloudFox is laser focused on helping cloud penetration testers, steampipe is an easy way to query any and all of your cloud resources.
* [Principal Mapper]() – Inspiration for, and a strongly recommended partner to the `iam-simulator` command
* [Cloudsplaining]() – Inspiration for the `permissions` command
* [ScoutSuite]() – Excellent cloud security benchmark tool. Provided inspiration for the `–userdata` functionality in the `instances` command, the `permissions` command, and many others
* [Prowler]() – Another excellent cloud security benchmark tool.
* [Pacu]() – Excellent cloud penetration testing tool. PACU has quite a few enumeration commands similar to CloudFox, and lots of other commands that automate exploitation tasks (something that CloudFox avoids by design)
* [CloudMapper]() – Inspiration for the `inventory` command and just generally CloudFox as a whole
**[Download Cloudfox]( “Download Cloudfox” )**Read More

